A Brief History of Cryptography: From Ancient Techniques to Modern Encryption
E N D
Presentation Transcript
Public Key Encryption Kyle Schmidt
A Brief History of Cryptography • Ancient Greeks • Scytale Cipher • Julius Caesar • Caesar Cipher • “Enigma” • Automated Cipher
What is Cryptography? • Secure and private communication • Encryption • Rendering a message unintelligible WEDNESDAY THE SIXTEENTH JRQARFQNL GUR FVKGRRAGU
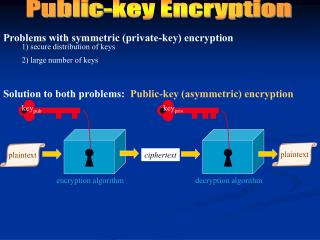
Symmetric vs. Asymmetric • Symmetric • Single key • Asymmetric (Public Key) • Two keys • Public key & Private key • Mailbox Concept • Digital Signature
Branches of Cryptology Cryptology Cryptography Cryptanalysis Symmetric Asymmetric Message Authentication Encryption Encryption
Advantages of Asymmetric • Secure Exchange of Keys • Can’t trust the middleman • Nonrepudiation • Keep track of your own key • More Uses • Encryption • Message Authentication • Digital Signatures
Modular Arithmetic • Most cryptosystems based on finite, discrete sets modulus = 12
Modulus Operation • Formal Definition: Given integers a, r, and m, we say a ≡ r mod m if (r – a) is divisible by m • Note that there are infinitely many remainders • Not to be confused with: a = r mod m
The Ring Zm • Ring of integers with properties: • Arithmetic operations always yield result in Zm • e.g. ∀a, bεZm then (a + b) ε Zm • Neutral elements 0 for addition, 1 for multiplication • e.g. ∀a εZm, a + 0 ≡ a mod m • Additive inverse always exists • i.e. ∀a εZm, ∃b = -a such that a + b ≡ 0 mod m • Multiplicative inverse only exists for some elements
Euclidean Algorithm • Calculates Greatest Common Divisor (GCD) • Simplify the problem • GCD(a, b) = GCD(a – b, b)
Euclidean Algorithm a = bq + r a = su b = tu b = s’v r = t’v r = a – bq a = bq + r r = (su) – (qt)u a = (s’v)q + (t’v) r = (s – qt)u a = (s’q + t)v
Euclidean Algorithm Procedure of Euclidean Algorithm
Extended Euclidean Algorithm • Modular Division • Multiplication by multiplicative inverse • ba-1 instead of b/a • Multiplicative Inverse: • aa-1≡ 1 mod m • Extended Euclidean Algorithm: • Fast, efficient way to find multiplicative inverse
Extended Euclidean Algorithm • Perform regular Euclidean Algorithm • GCD(a, b) must be 1 • Then for ax + by = 1, • x is the multiplicative inverse of a, and • y is the multiplicative inverse of b
Extended Euclidean Algorithm a = bq1 + r1 b = q2 r1 + r2 r1 = q3 r2 + r3 rn-2 = qn rn-1 + 1 r1 = a – bq1 r2 = b – q2 r1 r3 = r1 – q3 r2 1 = rn-2 – qn rn-1 1 = rn-2 – qn rn-1 1 = rn-2 – qn (r1 – q3 r2) 1 = rn-2 – qn (r1 – q3 (b – q2 r1)) 1 = rn-2 – qn (r1 – q3 (b – q2 (a – b q1))) 1 = ax + by
Extended Euclidean Algorithm • Proof ax + by = 1 ax + by 1 mod a by 1 mod a aa-1 1 mod a
Euler’s Totient Function • Essential for RSA Scheme • and most likely others • Totient (n) • Number of totatives of an integer n • Totative: An integer m, 0 < m < n, GCD(m, n) = 1 • Prime factorization of n must be known
Example: (30) C = 5 25 (5) {1, 2, 3, …, 30} S = 10 15 2 20 30 3 4 8 14 A = 9 = B 6 12 21 (2) 16 22 (3) 24 27 18 26 28 13 17 19 1 7 11 23 29
Example: (30) • Calculate totients from frequency • De Morgan’s Theorem: • Probability a number is in a subset is equal to Probability a number is not in all other subsets • Probability a number is NOT in a set is equal to 1 – (Probability of being IN the set) • Probability= (1 – 1/2) * (1 – 1/3) * (1 – 1/5) • Frequency = (1 – 1/2) * (1 – 1/3) * (1 – 1/5) * 30
Euler’s Totient Function • Formula: (n) = n(1 – 1/p1)(1 – 1/p2)…(1 – 1/pm) = (n) = (p1 – 1)p1k1–1(p2 – 1)p2k2–1 …(pm – 1)pmkm–1
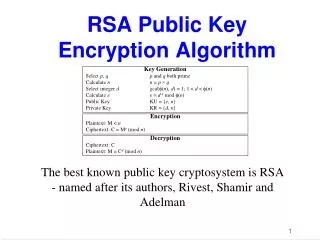
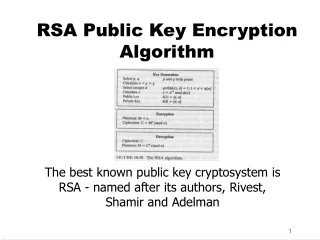
RSA • Ronald Rivest, Adi Shamir, Leonard Adleman • 1977 • Most widely used asymmetric scheme today • Two main uses: • Secure exchange of keys • Digital signatures
How RSA Works • Keys are pairs of integers • Encrypting key: (e, n) • Decrypting key: (d, n) • Encryption/Decryption: Exponentiation within Zn • Encrypt message: C = Me • Decrypt cyphertext: M = Cd • Before encrypting: • Convert plaintext to integer with hash function
RSA: Key Generation • Choose two arbitrary prime numbers p and q • Calculate n = pq • Calculate (n) • = (p – 1)(q – 1) • Choose arbitrary integer e < (n) – 1 such that GCD(e, (n)) = 1 • Calculate d = multiplicative inverse of e mod (n) using Extended Euclidean Algorithm
RSA: Key Generation • Basic requirement: • After choosing p, q, choose e, d, k satisfying: • ed – 1 = k(p – 1)(q – 1) • Extended Euclidean Algorithm requires two integers that are relatively prime • Thus, requiring e and (n) to be relatively prime ensures that there will be a matching private key
How RSA Works • Me = C; Cd = M • Prove Cd≡(Me)d ≡ Med≡ M mod n • Fermat’s Little Theorem • M(n)≡ 1 mod n if M and n are relatively prime • Mk(n) ≡ 1 mod n • M*Mk(n) ≡ M mod n • Mk(n)+1 ≡ M mod n • ed – 1 = k(p – 1)(q – 1) • ed = k(p – 1)(q – 1) + 1 • ed = k (n) + 1 Med ≡ M mod n
How RSA Works • M = Med • = M1+(n)k • = (M)M(n)k • = (M)(M(n))k • = (M)(1)k • = M • M = M
RSA: Faster Encryption • “Square-and-Multiply” Algorithm • Quick and efficient, even with large numbers • Based on binary representation of exponent • Iterative through bits, left to right • Consider y = xh mod n • Starting with 2nd bit from left: • Calculate y = x • Calculate y = y2 mod n • If current bit of h is 1, calculate y = yx mod n • Repeat steps 2 and 3 for each bit in exponent
Iteration Current Bit Calculation Value of y y = x 2 1 1 [1] 0 1 0 y = y2 mod n 4 mod 5 = 4 1 1 [1] 0 1 0 y = y * x mod n 8 mod 5 = 3 2 1 1 [0] 1 0 y = y2 mod n 9 mod 5 = 4 3 1 10 [1] 0 y = y2 mod n 16 mod 5 = 1 3 1 10 [1] 0 y = y * x mod n 2 mod 5 = 2 4 1 10 1 [0] y = y2 mod n 4 mod 5 = 4 RSA: Faster Encryption • Example: y = 226 mod 5
RSA: Faster Encryption • Square-and-Multiply has complexity O(log n), where n is the number of bits in the exponent • Relatively efficient • Although still intensive for small devices • Speed up encryption more: smaller public key • No significant loss of security
RSA: Faster Decryption • Can’t use smaller private key • Major security loss • Chinese Remainder Theorem • Allows computation of y = x mod (pq) given: • y1 = x mod p and y2 = x mod q • Break down Cd mod n into smaller computations • More computations, but less intensive • Requires knowledge of p and q, thus cannot be used to speed up encryption
RSA: Faster Decryption • Variation of Fermat’s Little Theorem: • xp-1 ≡ 1 mod p • Using this, break down exponent d into d1 = d mod (p – 1) and d2 = d mod (q – 1) • Decryption now requires two exponentiations: • Using Chinese Remainder Theorem, compute: y ≡ y1q(q–1mod p) + y2p(p–1mod q) mod n • On average, four times faster
Practical Uses of RSA • Even with these methods to speed up RSA, it is still much slower than symmetric systems • Not typically used for large-scale encryption • Encrypt smaller messages • Passwords • Symmetric keys • Digital Signatures • Used together with symmetric systems • Secure key exchange + fast, efficient encryption
Problem • Modern computers becoming more efficient • Factoring large numbers is becoming easier • Larger keys required for RSA to remain secure • RSA becoming slower and slower
Alternative • Elliptic Curve Cryptography (ECC) • 1985 • Neal Koblitz, Victor S. Miller • Estimated to be widespread within next decade
Elliptic Curve Cryptography: Premise • Point “Addition” (addition of ordered pairs) • Given a set E of points, and an operator “+”: • Compute “sum” of two points as another point • P + Q = R; P, Q, RɛE • NOT actual arithmetic addition • Point “Multiplication” • G = P + P + … + Pk = kP; G, P ɛ E, k ɛR
Elliptic Curve Cryptography: Premise • The set E is drawn from points of an elliptic curve • y2 = x3 + ax + b • Security comes from difficulty of finding k if given G and P • Elliptic Curve Discrete Logarithm Problem • Can’t just divide G by P • Not arithmetic multiplication! • More similar to finding k in a = bk • No efficient algorithm exists to solve this problem
Computing P + Q • Since elliptic curves are cubic, there are generally three points a line intersects the curve • Use this fact to calculate P + Q • Draw line from P to Q • Define the third point of intersection to be –R • Thus R is the mirror reflection of –R
Computing P + Q • If there is no third point (the line is vertical), P + Q is said to be “infinity”, denoted as O • O is an additive identity (P + O = P) • To compute P + P, use P’s tangent line instead
Elliptic Curve Algebra • Algebraic Formulae: • P + Q • xP+Q = β2 – xP – xQ • yP+Q = β(xP – xR) – yP • β is the slope of the line • P + P (or 2P) • x2P= ([3x2P + a] / 2yP)2 – 2xP • y2P = ([3x2P + a] / 2yP) * (xP– xR) – yP • ais the same parameter from the cubic equation
How it is Applied to Cryptography • To ensure security, some restrictions: • Curve must be smooth (no cusps, intersections, etc) • Can’t use all real numbers – must be discrete • In particular, prime numbers or binary numbers • No longer a “curve,” but algebra still holds • Why ECC is harder to crack than RSA: • Algebra is more complex than factoring numbers
Secure Key Exchange • Variation of Diffie-Hellman Scheme • Alice and Bob agree on parameters for curve • a, b in y2 = x3 + ax + b and a point Gɛ E • Alice chooses a private integer XAand calculates a point YA = XAG • Bob does similar, calculating YBfrom integer XB • Alice and Bob publicly exchange YA and YB • The secret key K is computed by: • For Alice, K = XAYB • For Bob, K = XBYA
Secure Key Exchange • Alice and Bob get the same private key, because: • K = XAYB • = XA(XBG) • = XBXAG • = XBYA • = K
The Bigger Picture • ECC found to be 10x faster than RSA • Requires less memory and computational power • Equal security as RSA • Ideal for use on: • Smart cards • Wireless devices • Other constrained devices RSA is unsuitable for
Symmetric Key Size RSA Key Size ECC Key Size 80 1024 160 112 2048 224 128 3072 256 192 7680 384 256 15360 521 The Bigger Picture • Security of RSA • Increasingly more vulnerable • Security of ECC • No significant increase in vulnerability over 25 years NIST Recommended Key Sizes for Equal Security
References [1] Alayont, Feryâl. (2005). “RSA: A Public Key Cryptosystem”. <http://faculty.gvsu.edu/alayontf/talks/rsa.pdf> [2] Kak, Avi. (2011). “Elliptic Curve Cryptography and Digital Rights Management”. Lecture Notes on Computer and Network Security. <https://engineering.purdue.edu/kak/compsec/NewLectures/Lecture14.pdf> [3] Kotas, William A. (2000). “A Brief History of Cryptography”. University of Tennessee Honors Thesis Projects. <http://trace.tennessee.edu/utk_chanhonoproj/398> [4] National Security Agency. (2009). “The Case for Elliptic Curve Cryptography”. <http://www.nsa.gov/business/programs/elliptic_curve.shtml> [5] Paar, Christof and Pelzl, Jan. (2010). “Introduction to Cryptography”. Understanding Cryptography – A Textbook for Students and Practitioners (online slides). <http://www.crypto-textbook.com> [6] Paar, Christof and Pelzl, Jan. (2010). “The RSA Cryptosystem”. Understanding Cryptography – A Textbook for Students and Practitioners (online slides). <http://www.crypto-textbook.com> [7] RSA Laboratories. (2000). “RSA Laboratories’ Frequently Asked Questions About Today’s Cryptography, Version 4.1”. <http://www.rsasecurity.com/rsalabs/faq/files/rsalabs_faq41.pdf> [8] Turner, Clay S. (2008). “Euler’s Totient Function and Public Key Cryptography”. <http://web.cs.du.edu/~ramki/courses/security/2011Winter/notes/RSAmath.pdf> [9] Vinck, A.J. Han. (2011). “Introduction to Public Key Cryptography”. <http://www.exp-math.uni-essen.de/~vinck/crypto/script-crypto-pdf/add-to-3.pdf> [10] Wagner, Neal R. (2003). “The RSA Public Key Cryptosystem”. The Laws of Cryptography with Java Code. <http://www.cs.utsa.edu/~wagner/lawsbookcolor/laws.pdf> [11] Weisstein, Eric W. “Euclidean Algorithm”. MathWorld – A Wolfram Web Resource. <http://mathworld.wolfram.com/EuclideanAlgorithm.html>
References • Additional images for this presentation retrieved from: • http://en.wikipedia.org/wiki/Enigma_machine • http://en.wikipedia.org/wiki/Public-key_cryptography • http://www.usc.edu/dept/molecular-science/RSA-2003.htm • http://en.wikipedia.org/wiki/Leonhard_Euler • http://physicsworld.com/cws/article/news/47723 • http://en.wikipedia.org/wiki/Credit_card