Exploring Public Key Encryption and Digital Signatures: Secure Communication in Cybersecurity
100 likes | 230 Views
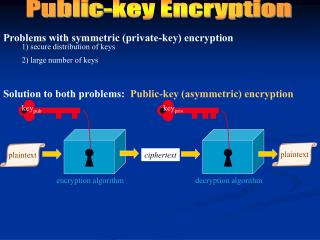
Discover how public key encryption and digital signatures secure communications. Ken Coder sends Dee a secret message protected by encryption, ensuring only she can unlock it. With innovative ideas like locking one box inside another, public and private keys play a crucial role. This system also allows legal validity, as documents signed digitally became legally binding in the US in 2000. Explore the implications of digital signatures in modern cybersecurity and the inherent trust they establish in electronic communications.

Exploring Public Key Encryption and Digital Signatures: Secure Communication in Cybersecurity
E N D
Presentation Transcript
Public Key Encryption 3 Digital Signatures or The Box within a Box
It could have come from Pre Tender! Yves Dropper's evil cousin
Dee's Idea: Lock your box in a second one using my public key.
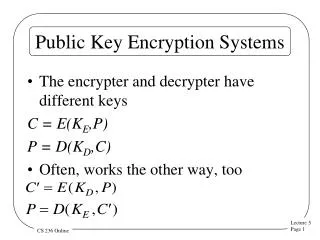
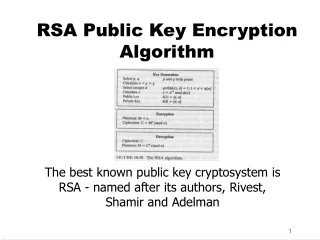
Digital Signatures • In any public key cryptosystem, one can implement digital signatures. • To send a signed message M from A to B using keys AE, AD, BE, BD: A sends cyphertext C = BE(AD(M)) B recovers text T = AE(BD(C)) T = AE(BD(BE(AD(M)))) = AE(AD(M)) = M A's Private Key B's private key
It's the law • Documents with Digital Signatures became legally binding in the United States in the year 2000.