ElGamal Public Key Encryption
ElGamal Public Key Encryption. CSIS 5857: Encoding and Encryption. ElGamal Public Key Encryption. Structure similar to RSA (discrete logs ) Component of many secure systems Digital Signature Standard (DSS) S/MIME (Email). Components of ElGamal. Components: Large prime q

ElGamal Public Key Encryption
E N D
Presentation Transcript
ElGamal Public Key Encryption CSIS 5857: Encoding and Encryption
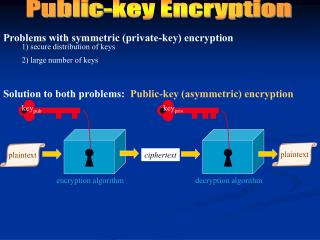
ElGamal Public Key Encryption • Structure similar to RSA (discrete logs) • Component of many secure systems • Digital Signature Standard (DSS) • S/MIME (Email)
Components of ElGamal • Components: • Large prime q • a = some primitive root of q • a is primitive root of q if • For all 0 <p <qthere exists some n < q such that an mod q = p • That is, powers of a “generate” all integers mod q • Necessary to make sure encryption has unique inverse, as this insures that (an mod q) ≠ (am mod q) for n ≠ m
Primitive Roots • Example: q = 19 Only primitive roots: 2 3 10 13 14 15
Public and Private Keys Example: q = 19, a = 10 • Generate random integer XA • 1 < XA < q-1 XA = 5 • Compute YA =aXAmod qYA = 3 • Public key: {q, a , YA} • Private key: {XA} • Security similar to RSA • Must be able to solve modular logarithm XA = logαYA to crack
Encrytion • Sender creates “one time key” for encryption • Message encrypted using modular exponentiation on one time key and public keys • Key “encrypted” using modular exponentiation and public keys • Recipient “decrypts” one time key using their private key • Recipient then decrypts message using that key
Encryption • Sender generates random integer k < q • Sender computes one-time key K = (YA)k mod q • Message M encrypted as two integers (C1 , C2) C1 = αk mod q C2 = KM mod q • Example: Plaintext message M = 17 Choose random k = 6 K = 36 mod 19 = 7 C1 = 106 mod 19 = 11 C2 = 7 x 17mod 19 = 5
Decryption • Recipient recovers K = C1XAmod q Example: K = 115 mod 19 = 7 • Recipient then recovers M = (C2 K-1) mod q • K-1is inverse of K mod q Example: 7-1 mod 19 = 11 (77 = 4 x 19 + 1) M = 5 x 11 mod 19 = 17
Why Does This Work? K = (YA)k mod q Definition of K = (aXAmod q)k mod q Definition of YA = (aXAk ) mod q Rules of modular exponentiation = (ak XA) mod q = (C1XA) mod q Definition of C1
Why Does This Work? M = (C2 K-1) mod q = (KM mod qK-1) mod q Definition of C2 = (M KK-1) mod q Rules of modular exponentiation = (M) mod q = M If M < q
Implementation Details • If M > q must break into smaller blocks M1, M2, M3 … < q • Must use differentk for each block • Otherwise single known Mi allows all blocks to be decrypted by factoring outK • C21 = KM1mod q = M1mod qC22KM2mod qM2mod q • If M1 known then M2 = C21-1C22M1mod q