Active Directory: Beyond The Basics
Active Directory: Beyond The Basics. Howard Marks Chief Scientist Networks are Our Lives, Inc!. Agenda. Active Directory Security Issues Replication and Bandwidth Management New Features with Windows 2003 Server Multiple forests. Active Directory Security Issues.

Active Directory: Beyond The Basics
E N D
Presentation Transcript
Active Directory:Beyond The Basics Howard Marks Chief Scientist Networks are Our Lives, Inc!
Agenda • Active Directory Security Issues • Replication and Bandwidth Management • New Features with Windows 2003 Server • Multiple forests
Active Directory Security Issues • Enterprise administrators can “elevate” themselves to administrate a domain • Directory access can be controlled
Tree Security • Just as folders and files have ACL's, so do objects in an ADS tree • A user’s permissions determine what the user or group can do to an object • This is used to create administrative boundaries within a tree • An all powerful Administrator is no longer necessary, but advisable
Assigning Tree Permissions • ACL information on an object flows down to the child objects of the container when a new object is formed • Future ACL changes to a parent object must be propagated to child objects to affect changes down the tree • This is exactly how the file system works
Full Control OU OU OU Full Control Full Control OK Cancel Apply Using Permissions Inheritance • Permissions Flow Down to Child Objects • Preventing Inheritance Stops the Flow of Permissions Allow inheritable permissions from parent to propagate to this object.
Directory Attributes • An object’s DACL can contain ACEs that protect individual attributes • Access permissions include • Read attribute • Write attribute • Deny read • Deny write • Where appropriate, objects also have permissions that control actions, such as • The creation/deletion of Child objects • Adding or removing an object from a group
Controlling Object Visibility • Most objects have a default explicit ACE defined that allows the Authenticated Users group to read the object • If you wish to limit the visibility of objects, this ACE must be removed
Delegate permissions to create and delete all objects of a specific type OU OU OU OU OU OU OU Delegate Access Control at the OU Users Object Type = User Permissions = Create Child Delete Child
Delegate permissions to administer a specific property for all objects of a certain type OU OU OU OU OU OU OU Delegating Permissions and Rights at the Object Property Levels Inherit Object Type = Group Object Type = Group Membership Permissions = Read Property Write Property Inheritance = Inherit Only Groups
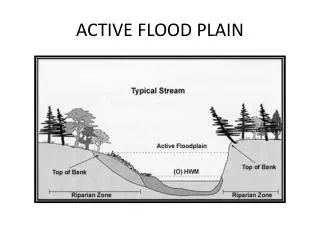
Active Directory Sites Replication Controlled Domain Controller • A site is one or more TCP/IP subnets with good network connectivity • Sites are used to isolate replication traffic Site User Logs On Domain Controller Site
Types of Replication Domain B Controller Domain A Controller Domain A Controller Intra-Site Replication Inter-Site Replication Site 1 Domain C Controller Domain B Controller Domain B Controller Domain A Controller Domain A Controller Site 2 Domain C Controller Domain C Controller
Types of Replication • Intrasite replication • Frequent • Uses IP and RPCs • Intersite replication • Scheduled • Frequency • Allowable hours • Route controlled via assigned costs • Can use RPCs or SMTP
Examining Site Locations • If there is no domain controller • No replication traffic • No logon traffic to and from the business location • The business location does not need to be a separate site • If there is a domain controller • There is replication traffic to and from the business location • There may not be any logon traffic • Determine whether the location should be a site
Determining Connectivity and Available Bandwidth • Only subnets that are considered fast, inexpensive, and reliable should be combined into a site • Consider controlling replication traffic and logon requests • An important consideration is available bandwidth
Planning Sites to Control Workstation Logon Traffic • Defining Sites • Workstations always look to the local site for a Domain Controller • Disadvantages of Multiple Sites in a Single Location • If a local site Domain Controller is not available, the workstation may log onto a DC anywhere on the WAN
Planning Sites to Control Replication Traffic • Multiple Sites in Replication • Replication time and the transport (RPC or SMTP) can always be specified • Replication traffic is always compressed reducing traffic 10% to 12% • Network Replication Traffic • Only changed attributes on changed objects are replicated
Planning Sites to Control Both Logon and Replication Traffic • A balancing act between: • The organization’s need to access directory information quickly • Speed and reliability of network links • Decide if Domains are a better solution • Refer to prior section
Windows 2003 Server AD Improvements • Domain Rename • Schema Redefine (Schema change undo) • Application mode • Improved Group Policy Management • Cross-Forest Trust • Improved Group Membership replication • Better branch office support
Domain Rename • You can now: • Change DNS and/or NETBIOS name of domain • Move domain position in forest • Create new tree • You still can’t: • Change which domain is the forest root • Split off domain or Add domain to forest • Reuse names • OK you can in 2 steps • Rename domains with Exchange 2000 servers in them
Domain Rename Limitations • All DCs must be on line • DCs that can’t participate are ejected from domain • All DCs reboot in process • All stations must reboot Twice • NT 4 stations must be rejoined manually • Forest must be in
Ownership Concept • In Windows NT Domains a single “person” owned the whole pie • AD allows us to separate to 2 roles: • Service owner • Responsible for service availability • Data owner • Responsible for data maintenance • Day to day administration ‘
The Forest Owner Role • Service owner • Ultimately responsible for the delivery of directory services in the forest • Set policy, process for changes to shared configuration, schema • Gatekeeper for new domains • Domain owners are service owners • Must be carefully managed
All business units share centralized DS infrastructure Forest Model #1: Strong Central Control Division 1 Division 2 Division 3
Business units opt-in/opt-out of centralized infrastructure Model #2: Hybrid/Subscription Division 1 Division 2 Division 3
Each business unit maintains separate DS infrastructure Model #3: Distributed Infrastructure Division 1 Division 2 Division 3
distributed Administrative Autonomy centralized low high Collaboration Assign Forests Multiple forests with MMS Multiple forests Long term trend Subscription forest Single forest
Identify Candidate Forest Owners • What IT groups are chartered to deliver NOS directory services? • Common to find multiple groups • Owners of Master User Domains (MUDs) • Previously-deployed forests • The Anti-Social • Legal reasons • Create list of candidate forest owners
Forest Participation Criteria • Satisfied with terms of service • Schema, config change control policies • Disaster recovery • Security considerations • Trust forest owner and all domain owners • DCs placed in secure locations • Have clear forest ownership • Attempting to share forest management may present organizational challenges • Do not extend forest management across multiple outsourcers
Inter-forest Implications • No automatic trust • Explicit trust is one-way, non-transitive • Fixable in 2003 • Kerberos not available between forests • No mutual authentication • Global catalog has forest scope • Aggregate view across forests requires synchronization technology • Microsoft Metadirectory Services (MMS) • Simple Sync