Addressing
Addressing. The ‘What’ and ‘Where’ of Communication. Addressing. Addressing is necessary for any communication To talk: Appearance, name, … To call: Telephone numbers To mail: Postal address To visit: Postal address + directions To E-Mail: E-Mail addresses

Addressing
E N D
Presentation Transcript
Addressing The ‘What’ and ‘Where’ of Communication
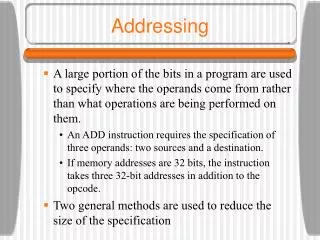
Addressing • Addressing is necessary for any communication • To talk: Appearance, name, … • To call: Telephone numbers • To mail: Postal address • To visit: Postal address + directions • To E-Mail: E-Mail addresses • To instant message: ICQ#, AIM ID, etc. • These ‘addresses’ allow us to uniquely identify the entity with which we wish to communicate
Addressing a la Shoch • Name/Identifier: What • Names normally identify the entity • If an entity moves, the name/identity will remain the same • Address: Where • Addresses identify the location of the entity • If an entity moves, the address will change • Route: How to get there • Routes identify the path to get to an entity • If an entity moves, the route will change
Addressing • Addressing deals with how to define an entity’s location (uniquely) • Addressing is necessary for message delivery • An address is the start and end point for the route • However, routing is another subject • Where do we want the message to go?
Addresses • We have already seen MAC addresses (for Ethernet and some other LANs): • e.g. 02-60-8C-08-E1-0C • 6 octet address • Globally unique • Defined statically by the hardware manufacturer • Most people are familiar with the IP addresses used by TCP/IP networks: • e.g. 137.207.32.2 • 4 octet address • Not necessarily globally unique • Defined dynamically by DHCP servers or negotiated by the operating system
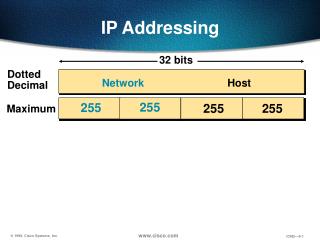
IP Addressing A Closer Look
IP Addresses • TCP/IP networks use IP for the network layer protocol • IP defines 4 octet addresses • 4 billion possible addresses • Usually written in the form A.B.C.D • A, B, C, and D are each 1 octet (0-255), normally written in decimal notation • Thus, IP addresses fall in the range: 0.0.0.0 – 255.255.255.255
IP Addresses • Originally intended for separate internets (interconnected LANs) • Thus, the 32 bit size was not a concern • 48 bits is generally considered a fairly safe size for globally unique addressing • Computers connected to ARPANET (and later incarnations) were just given consecutive addresses 1.0.0.0, 1.0.0.1, 1.0.0.2, …
IP Addresses • Any computer connected to a TCP/IP network (e.g. the Internet) must have an IP address • Further, any network interface card (NIC) using TCP/IP to access an network (e.g. the Internet) must have a different IP address
IP Addresses • Even though there are 4 billion possible IP addresses, they are running out • Here’s why: • Some of the bits are dedicated to header information (discussed later) • ½ the addresses for each lost bit • Addresses are categorized, and some of the categories are running out of addresses (while others are not)
Non-Classed Addresses • Part of the address represented the network the computer resided on, and part represented the computer itself • Network: 7 bits (up to 128 networks) • Computer: 24 bits (up to 1.6 million computers on each network) • Since there were very few networks on ARPANET originally, this wasn’t a problem
Address Classes • When private organizations started joining the Internet, the needs became obvious • Some (fewer) networks have multitudes of computers (thousands) • e.g. The @Home network • Some (many) networks have very few computers (a few hundred or less) • e.g. The Windsor Police Department
Address Classes • Quickly, the addresses were separated into 3 classes (plus room for more classes if needed): • Class A: Fewer networks, many nodes • Class B: Medium networks, medium nodes • Class C: Many networks, fewer nodes
IP Address Classes Class A: bit index: 0 1-7 8-31 0 network host (machine) Class B: bit index: 0 1 2-15 16-31 1 0 network host Class C: bit index: 0 1 2 3-23 24-31 1 1 0 network host
IP Address Classes • Class A: • Range: 1.0.0.0 – 126.0.0.0 • Networks: 128 max, Machines: 65537-1.6 million • e.g. huge networks, such as large military/government organizations (e.g. FBI), the @Home network, etc… • Class B: • Range: 128.1.0.0 – 191.255.0.0 • Networks: 16384 max, Machines: 257-65536 • e.g. Internet service providers (ISPs) (dial-up) • Class C: • Range: 192.1.0.0 – 223.255.255.0 • Networks: 2 million max, Machines: 1-256 • e.g. Small businesses
IP Address Classes • The IP address classes are self-identifying • Which means that given the address, you can determine what class an address is • Actually, using only the first number • Examples: • 137.207.32.2 (server.uwindsor.ca) • 137 -> Class B • 24.0.0.1 (@Home DHCP server) • 24 -> Class A
Other IP Address Classes Class D: bit index: 0 1 2 3 4-31 1 1 1 0 Multicast group address • These addresses are used to represent multicast groups • Discussed later Class E: bit index: 0 1 2 3 4 5-31 1 1 1 1 0 Reserved for future use • These addresses were left open to be used and divided into classes as needed
Special IP Addresses • 0.0.0.0: Used to indicate that this machine is without an assigned IP • Used during bootstrapping (e.g. requesting an IP from a DHCP server) • <all 0s (binary)><hostID>: Used to send messages to some machine on this network • 255.255.255.255: Used to send broadcast messages across this machine’s network • <netID><all 1s (binary)>: Used to send broadcast messages to the specified network • 127.0.0.1: Used to send messages back to this machine (called loopback or localhost)
IP Addressing Comments • In IP addressing: • 0’s usually represent ‘this’ • 1’s usually represent ‘all’ • Broadcasting, although discussed here in terms of addressing, will be discussed further
Loopback • The 127.0.0.1 address, does not normally exist on the network • Either as the source address or destination address of a packet • The address is used internally by NICs • When a NIC receives a message addressed with 127.0.0.1 to be transmitted, it passes the message directly to the receiver hardware • The receiver hardware returns the message to the operating system exactly as if the message were received from the network • However, the message never entered the network medium
Internal IP Addresses • Depending on the address class needed by an organization, a range of internal addresses is available: • Class A: 10.0.0.0 – 10.255.255.255 • Class B: 172.16.0.0 – 172.31.255.255 • Class C: 192.168.0.0 – 192.168.255.255 • IP routers outside a private (connection-shared) network, will not forward datagrams designated for addresses in these ranges
Multi-homed Machines • There is no restriction preventing machines from participating in multiple networks • A machine could have multiple NICs • Each NIC would have its own MAC address • On TCP/IP networks, each of these NICs would be given a different IP address
M M M M M M Multi-homed Machines 192.168.0.1 192.168.0.2 192.168.0.3 192.168.0.8 192.168.0.4 Class C private network M M M M M M M 192.168.0.7 M 192.168.0.6 192.168.0.5 172.16.3.16 172.16.3.15 172.16.3.14 172.16.3.17 M M 172.16.3.18 Class B private network 172.16.0.1 172.16.0.2 172.16.0.3 172.16.0.4
Multi-homed Machines 192.168.0.1 192.168.0.2 192.168.0.3 192.168.0.8 192.168.0.4 Class C private network 192.168.0.7 192.168.0.6 192.168.0.5 172.16.3.16 172.16.3.15 172.16.3.14 172.16.3.17 172.16.3.18 Class B private network 172.16.0.1 172.16.0.2 172.16.0.3 172.16.0.4
Routers • Routers are multi-homed machines • They have a number of network ports, each of which represents a different path • Routers use tables that relate destinations to network paths • Internet routers relate destination network addresses with one of their network ports • When a datagram arrives at a router: • Its destination address is used to determine the network address • The network address is used to look up the destination port in the routing table
Network Addresses • An IP address can be used to calculate the address of the network • The machine address is passed through a filter (called a subnet filter): • This filter extracts the bits of the address that represent the network and sets the bits that represent the machine to zero • The filter determines which part of the address represent the network address, by using the subnet mask
Subnet Mask • The subnet mask is a binary number, that has 0s in the machine portion of the address, and 1s in the network portion • Most networks of each type use a constant subnet mask • Class A: 255.0.0.0 (Binary: 11111111000000000000000000000000) • Class B: 255.255.0.0 (Binary: 11111111111111110000000000000000) • Class C: 255.255.255.0 (Binary: 11111111111111111111111100000000)
Using Subnet Masks • Example: • Address: 137.207.32.2 • Subnet Mask: 255.255.0.0 Address: 10001001110011110010000000000010 Mask: 11111111111111110000000000000000 Net Address: 10001001110011110000000000000000 • Network address: 137.207.0.0
Routing in Action Internet Network N1 (Class B) Address: 137.207.0.0 P4 P1 P2 P3 Network N2 (Class C) Address: 194.201.61.0 Network N3 (Class A) Address: 24.0.0.0
IPv6 Next Generation Addressing in TCP/IP Networks
IPv6 • Due to the limited nature of existing IP addressing (IPv4), a new version of IP addressing was developed • This new scheme uses 16 octets for addresses, instead of 4 octets • Written using hex notation: 3A57:0000:0000:9CD5:3412:912D:6738:1928
IPv6 Features • 16 octet addresses (128 bits) • Larger numbers of address classes • More accurate control of network/machine counts • Variable-sized headers • Optional information can be placed into the header when needed • Reduces header size in most cases • Extendible protocol • IPv6 allows for new header information to be added to support different protocols
IPv6 Features • Automatically reconfigurable • Addresses can be automatically reassigned dynamically • e.g. when a certain number of nodes join the network, a different address class may be desired • Autoconfigurable • The use of autoconfiguration (such as DHCP) allows dynamic private addressing and dynamic public addressing
IPv6 Datagram Format optional header extension headers data
IPv6 Header Format 0 4 12 31 version traffic class flow label 32 48 56 63 payload length next header hop limit 64 96 128 source address destination address
IPv6 Integration • Will IPv6 replace IP addresses? • Who knows? • Currently, temporary solutions have made IPv4 addresses capable of lasting longer than originally predicted • If and when IPv6 is to be integrated, the process must be a transition • Closing the entire Internet down to convert hardware and software to IPv6 not going to happen • Some stations may take longer to transition than other stations • e.g. Bob’s Internet Shack vs. the Telus Network
IPv6 Integration • NAT (network address translators) provide one example of such a temporary solution • NATs provide three benefits: • NATs provide IP masquerading • Messages using these addresses pass through a network address translator (NAT) to be transformed into external IPs • NATs provide IP sharing • ISPs for example, have many customers, but significantly less at any given time are logged onto their system • IP addresses can be assigned dynamically to these customers when they log in • NATs provide schemes to allow networks to use either IPv4 or IPv6 • Addresses would be converted as they pass through a NAT
IPv6 Integration • Another method that may be used for the transition between IPv4 and IPv6 is address inclusion: • IPv4 addresses could be embedded into IPv6 addresses • Translation between the two types of addresses is possible without any other information • Some problems exist with this approach, but in general it simplifies communication between IPv6 networks and IPv4
Special IPv6 Addresses • 0:0:0:0:0:0:0:0 Used to indicate that this machine is without an assigned IP • Used during bootstrapping (e.g. requesting an IP from a DHCP server) • 0:0:0:0:0:0:0:1 Used to send messages back to this machine (called loopback) • These two addresses are not valid on the actual network medium (same as with IPv4) • 00:… Reserved (including IPv4 and IPX address inclusion) • FF:… Multicast addresses
IPX Internetwork Packet Exchange Addresses
IPX • IPX was originally created to replace IP • In reality, it is used primarily on LANs • In conjunction with the SPX protocol, formed one of the two protocol suites used in Netware networks • SPX is to TCP, what IPX is to IP • Still can be (although rarely is) used today in Windows networks
IPX Addresses • IPX uses a 2 component address (like IP): • The network portion (4 octets) • The machine portion (6 octets) • Unlike IP, these sizes are constant • So there are no IPX address classes • IPX uses sizes large enough to accommodate all categories of networks
IPX Addresses • The network portion of an IPX address is 4 octets (32 bits) • This allows for 4.29*109 networks (4 billion) • This is almost enough for everyone on earth to have their own network • The machine portion of an IPX address is 6 octets (48 bits) • This allows for 2.81*1014 machines on each network (281,475 trillion)
IPX Addresses • The scalability of IPX addresses is not their only benefit • The constant size of the network and machine address portions simplifies extracting each portion • As a result, machines that process IPX networks can process IPX datagrams more quickly • Such as network nodes, routers, etc.
IPX Addresses • Why 48 bits for the machine portion? • 48 bits allows for way too many machines, more than will be needed for many years • By the time machine IDs run out, network hardware and software will have been obsolete by many years! • Using 48 bits allows hardware to use the machine’s MAC address as the machine portion • This makes auto-configuration (dynamic IPX address assignment) easier/faster
IPX Addresses • If IPX has been around since the NetWare days, why don’t we use it for the Internet, instead of IP? • Good question! Why don’t we? • Frankly, IPX has a bad reputation, because initially it was used with SPX and other bandwidth-munching protocols • IPX can be used in conjunction with TCP (TCP/IPX), and it would make an excellent replacement for TCP/IP • However, standards organizations (e.g. ISO) want to use the protocols they develop, and not ones developed by corporations, such as Novell
Fragmentation & Reassembly • Packets can arrive out of order in connectionless networks • Packets must be reordered during reassembly • During fragmentation, the portion of data that each fragment represents must be identified • Since the length of a packet’s data can always be determined, all that is necessary is to use the offset of the start of the packet’s data in the larger data chunk
Fragmentation & Reassembly 0 1500 3000 4500 6000 6800 Logical Data Chunk Length:1500 Length:1500 Length:1500 Length:1500 Length:800 Offset:0 Offset:1500 Offset:3000 Offset:4500 Offset:6000 Packet 1 Packet 2 Packet 3 Packet 4 P5
Fragmentation & Reassembly • Why do we use the data offset, and not just a sequence of numbers to determine packet order? • Sometimes, packets can be fragmented at one location, and must be re-fragmented at another location (such as while passing through a network incompatible with larger frame sizes) • These situations would require renumbering of all packets in the sequence, which is not always possible
Fragmentation & Reassembly Length:1500 Length:1500 Length:1500 Length:1500 Length:800 Offset:0 Offset:1500 Offset:3000 Offset:4500 Offset:6000 Packet 1 Packet 2 Packet 3 Packet 4 P5 Packet 1 Packet 2 P3a P3b Packet 4 P5 Length:1000 Length:500 Offset:3000 Offset:4000