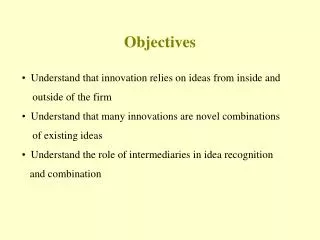
OBJECTIVES
OBJECTIVES. 1. Install Windows NT 4.0 and Windows 2000 to new systems. 2. Upgrade systems from Windows 9x or Windows NT 4.0 to Windows 2000. 3. Describe the bootup sequence employed by Windows NT/2000.

OBJECTIVES
E N D
Presentation Transcript
OBJECTIVES 1. Install Windows NT 4.0 and Windows 2000 to new systems. 2. Upgrade systems from Windows 9x or Windows NT 4.0 to Windows 2000. 3. Describe the bootup sequence employed by Windows NT/2000. 4. Navigate through the Windows NT/2000 system, including the Internet Explorer. 5. Explain the structure of Windows NT/2000. 6. List the core files in the Windows NT and Windows 2000 structures. 7. Identify the components of the Windows NT/2000 Registry structure. 8. Install and access printers in Windows NT 4.0 and 2000. 9. Install and access software applications in Windows NT and 2000. 10. Install and configure hardware devices and drivers in Windows NT and 2000. 11. Install and configure Local Area Networking functions in Windows NT and 2000. 12. Install and configure Wide Area Networking and Internet functions in Windows NT 4.0 and 2000.
It was built around a new operating system kernel that focused on enhanced reliability, scalability, and security elements required for corporate applications, while retaining the strengths of the Windows operating system.
The Windows NT operating system actually exists as three distinct products: A Workstation operating system A Server operating system An Extended Server operating system to manage large enterprise networks
The Windows NT 4.0 Server package provides the same features and functions found in the Windows NT Workstation. However, the Server package also provides the tools necessary to administer and control a network from its central location.
Enterprise networks are those networks designed to facilitate business-to-business, or business-to-customer operations. Because monetary transactions and customers’ personal information travel across the network in these environments, enterprise networks feature facilities for additional, highly protective security functions.
An intranet is a network built on the TCP/IP protocol that belongs to a single organization. It is in essence a private Internet. Like the Internet, intranets are designed to share information and are accessible only to the organization’s members, with authorization.
Windows 2000 is the successor of the Windows NT 4.0 operating system. As a matter of fact, it was originally titled Windows NT 5. This operating system brings together the stability and security of Windows NT 4.0 and the Plug-and-Play capabilities of Windows 9x.
Like previous NT versions, Windows 2000 comes in two basic variations: the corporate workstation version, titled Windows 2000 Professional, and the network server version, called Windows 2000 Server. The server product is also available in two extended enterprise versions — Windows 2000 Advanced Server and Windows 2000 Datacenter Server.
The standard Windows 2000 Server package can manage up to 4 GB of RAM and is capable of distributing work between two microprocessors at a time. This type of operation is referred to as Symmetrical Microprocessing (SMP). If Windows 2000 Server has been installed as an upgrade to an existing Windows NT 4.0 Server, it can support up to four different microprocessors simultaneously.
NOTE Recall that an intranet is simply a private, web-based network, typically established by an organization for the purpose of running an exclusive web site not open to the public (i.e., company web sites for internal company use only). Intranets can be based on local or wide area networks, or constructed as combinations of the two.
The Advanced Server edition can support up to 8 symmetrical processors and up to 8 GB of memory. These features enable it to function well in medium size networks running between 100 and 500 concurrent users.
The Windows 2000 Datacenter Server edition can handle up to 64 GB of RAM and 32 processors. This will enable it to support up to 1000 simultaneous users with heavy processing demands.
A network share is an existing shared resource (i.e., printer, drive, modem, or folder) located on a remote system.
Locating, accessing and retrieving information in Windows NT is virtually the same as with the Windows 9x operating systems.
The major Windows 2000 user interfaces are: My Computer Start menu Windows Explorer Internet Explorer My Network Places Windows 2000 dialog boxes (windows)
Instead of simply truncating the filename, inserting a tilde, and then assigning a number to the end of the filename, Windows NT performs a mathematical operation on the long name to generate a truly unique MS-DOS compatible filename.
However, when five or more names are generated that would result in duplicate short names, Windows NT changes its truncation method. Beginning with the sixth filename, the first two characters of the name are retained, the next four characters are generated through the mathematical algorithm, and, finally, a tilde with an ID number is attached to the end of the name.
Windows 2000 offers extended common dialog boxes for File/Open, File/Print, and File/Save options. These dialog boxes provide easy organization and navigation of the system’s hard drives, as well as providing navigation columns that grant quick access to frequently used folders, such as the My Documents and My Pictures folders.
The Search feature provides three distinct search options: 1 For Files and Folders 2 On the Internet 3 For People
TEST TIP Know which characters can legally be used in a Windows 2000 filename.
When fully installed, the Windows NT logical structure exists. It is a modular operating system that allows for advances in computing technology to be integrated into the system. The operating system exists in two basic layers referred to as Modes. These two levels are the Kernel Mode and the User Mode.
Basically, the operating system runs in the Kernel Mode while applications run in User Mode. The User Mode is a more restrictive operating mode where there is no direct access of hardware permitted.
APIs are routines, protocols, and tools built into the operating system that provide application designers with consistent building blocks to design their applications with. For the user, these building blocks lead to consistent interfaces being designed for all applications.
The Kernel Mode is the operating mode where the program has unlimited access to all memory, including those of system hardware, the User Mode applications, and other processes (such as I/O operations).
The Windows NT HAL is a library of hardware drivers that operate between the actual hardware and the rest of the system. These software routines act to make every architecture look the same to the operating system.
The Microkernel works closely with the HAL to keep the system’s microprocessor as busy as possible. It does this by scheduling threads for introduction to the microprocessor on a priority basis.
The Win32k Executive Services block provides all the basic operating system functions for the NT environment.
The Win32k Executive Services block is made up of a number of managers that include: I/O Manager Object Manager Security Reference Manager Process Manager Virtual Memory Manager Window Manager Graphic Device Interface Graphic Device Drivers
As its name indicates, the Windows NT I/O Manager manages all input and output functions for the operating system. Its major function involves controlling communications between file system drivers, hardware device drivers, and network drivers and the system.
Windows NT 4.0 objects include: Directory Objects File Objects Port Objects Process and Thread Objects Symbolic Link Objects Event Objects and Others
The other basic Windows NT layer is referred to as the User Mode. This mode is a collection of subsystems that interact with users and applications.
However, the Windows NT Registry is not compatible with the Windows 9x Registries.