Windows Malware Detection & Removal Guide
250 likes | 272 Views
Understand malware types, vulnerabilities, and removal methods to safeguard your PC. Learn about viruses, spyware, botnets, rootkits, and more. Keep your system secure using antivirus, firewalls, and best practices.

Windows Malware Detection & Removal Guide
E N D
Presentation Transcript
Windows Malware: Detection And Removal TechBytes Tim Ramsey
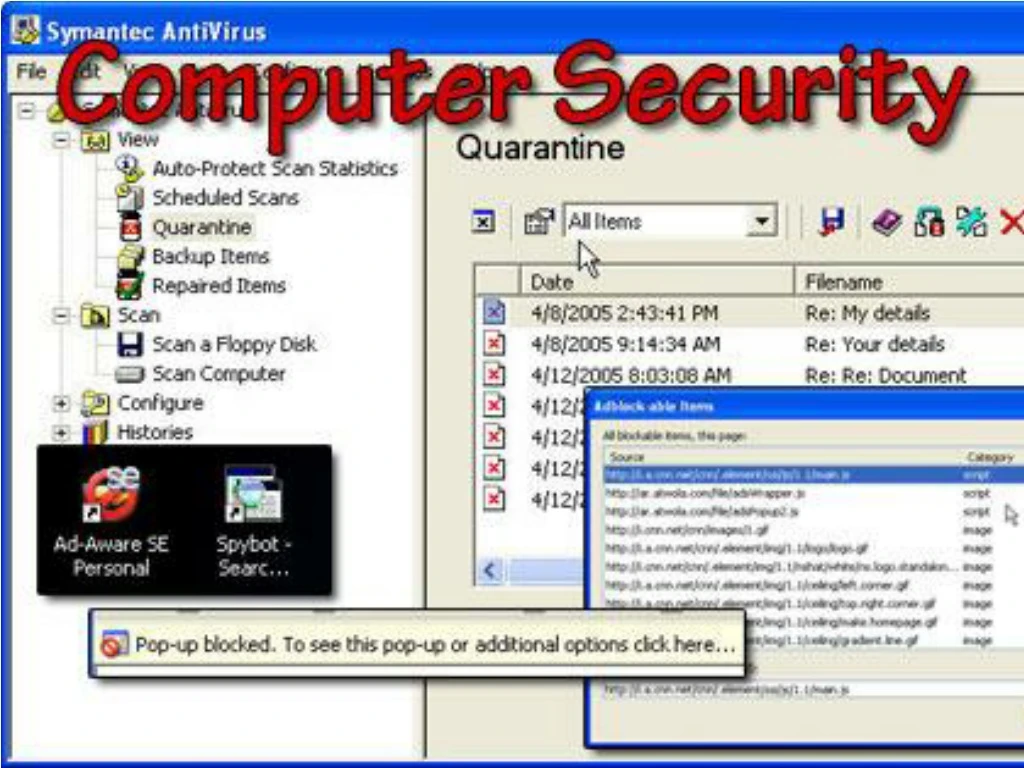
Computer Security! • What is “malware”? • How does malware get on my PC? • How do I get rid of malware? • Resources
What Is “Malware”? • “Malicious Software” • Includes: • Viruses, worms, Trojan horses • Spyware • Remote-control software • “Botnets” • Rootkits • The lines are getting blurry
Viruses, Worms, Trojan Horses • Viruses: modify executables and documents; we humans do the rest • Worms: self-replicating programs • Trojan Horses: still fooling us after all these years
Spyware • Installed with or without your knowledge and consent • Do you read the entire EULA? • I do (except the French part) • Tracks URLs visited, information entered into forms • Can even monitor secure (https://) pages
Spyware, Cont. • Keyboard loggers: capture passwords, PINs, account numbers • Organized crime loves this stuff
Remote–Control Software • Windows Remote Assistance • VNC, Radmin • Netbus, BackOrifice
Botnets • “The single greatest threat facing humanity” • Quickly becoming a top problem on campus • Hordes of infected “drone” hosts • Used for spam relay, DDOS, scanning, infection
Botnets, Cont. • Spreading via IM, email, compromise • Installs remote-control software • Connects to central server to announce presence and await commands • Allows “Botmaster” to control 100, 1000, 10000+ infected hosts with simple commands • Continually evolving
Botnets, Cont. 2 • Network connections are initiated by the drone hosts • Uses common protocols: HTTP, IRC, FTP • Starting to see stealth techniques employed to hide infection (rootkits), communications (SSL, steganography) • Tremendous incentives for Botmasters to grow, maintain, defend their horde • You don’t want this on your computer
How Does Malware Get On My PC? • Compromise • Security vulnerabilities • Browser vulnerabilities • Open file shares • Social Engineering • People click on the darndest things • Packaged with other software
How Do I Get Rid Of Malware? • Best: Don’t get infected • Antivirus • OS and application patches • Enable Windows Firewall • Healthy paranoia • Don’t run files that friends or strangers send to you! • Don’t install random software from the Web • Um, yeah. I still got infected. What now?
Malware Removal • Safest: “R/R” • Reformat / Reinstall are necessary if the infection contains a remote control component • No telling what has been installed, changed • SIRT policy • A botnet infection means R/R is mandatory • Otherwise, try to identify the infection
Identifying The Infection • Anti-Virus software scan • Anti-Spyware scan • Spybot Search & Destroy • Microsoft Windows AntiSpyware (Beta) • AdAware • Other, more specialized, tools
Removing The Infection • Are you sure you wouldn’t rather R/R? • If you’ve identified the infection, look for a removal tool • Symantec, McAfee, other AV vendors • Google search (but be careful) • When in doubt, reformat and reinstall
A Note About Reformat / Reinstall • Back up your data first • Practically every OS is vulnerable to network compromise during installation • Unplug the computer from the network • Install OS, service packs, patches from CD • Enable Windows Firewall • Install SAV from CD • Set administrator password • Then plug back in
Rootkits: Making Life Harder • Pre-packaged software to hide malware • Freely obtainable (rootkit.org) • There are even commercial packages! • Insert hooks into system, kernel • Trap program calls to list directory contents, running processes, registry entries • Filter out what the bad guys don’t want you to see
Detecting Rootkits • Look for the hooks • Look for known file names, processes • Look for what’s being hidden • Difficult to do, getting more difficult • Tools exist to do this, but most don’t detect everything • Hot topic of research for both sides
Removing Rootkits • Are you sure you wouldn’t rather R/R? • Removal tools exist for most rootkits • Deep magic, requiring wizardry and time
Resources • K-State provided antivirus software • http://antivirus.ksu.edu/nav/ • Spybot Search & Destroy • http://www.safer-networking.org/ • Microsoft Windows Antispyware (Beta) • http://www.microsoft.com/athome/security/spyware/software/
Resources, Cont. • Rootkit Detection • http://www.f-secure.com/blacklight/ • http://www.sysinternals.com/ntw2k/freeware/rootkitreveal.shtml • K-State configuration for XP Firewall • http://knowledgebase.itac.ksu.edu/art.asp?id=274 • SANS Top 20 • http://www.sans.org/top20/
Thanks For Coming! (I hope today wasn’t too taxing)