Application performance management
Application performance management. The Next Generation. What is Application Performance Management?. Visibility – who is doing what, when? Prioritization – protect what’s mission-critical, restrict what’s not Acceleration – local caching of bandwidth-heavy content

Application performance management
E N D
Presentation Transcript
Application performance management The Next Generation
What is Application Performance Management? Visibility – who is doing what, when? Prioritization – protect what’s mission-critical, restrict what’s not Acceleration – local caching of bandwidth-heavy content Security – protect internal assets from external threats
…Legacy Solutions Have Not Internet
Next-Generation Requirements Identify (more) Applications Encrypted P2P Anonymous Proxies Integrate with AD and/or LDAP Keep pace with changes in technology Ease of use – administration & reporting One administrator, many boxes Different tropes (?) for different folks Plays well with others
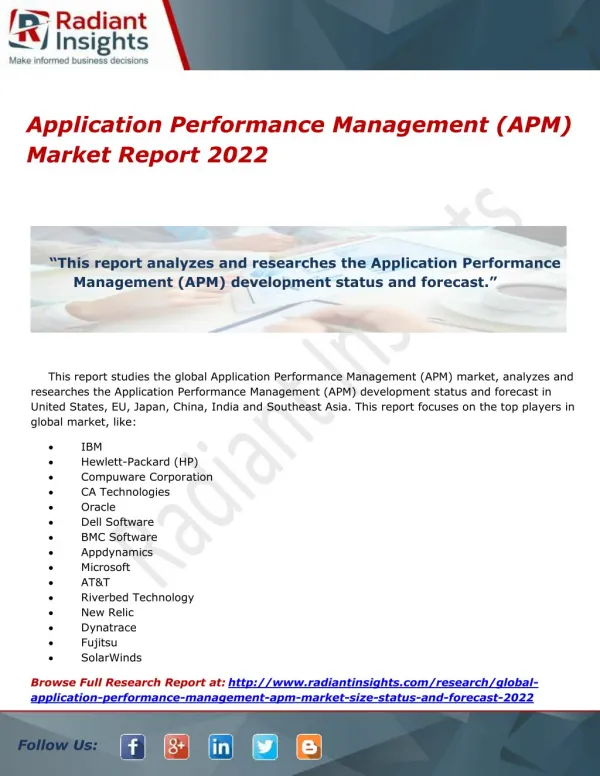
Next-Gen At the Edge Set firewall policies based on application, regardless of port, protocol, SSL encryption, or other evasive tactic. Palo Alto Networks currently offers over 1,000 layer-7 signatures, as well as IPS and URL Filtering capabilities.
Next-Gen In the Data Path Exinda’s shaping solution offers over 2,500 application signatures, a heuristics engine to catch encrypted P2P traffic, and significantly lower Total Cost of Ownership than legacy shapers.
The Next-Generation Data Path Internet
THANK YOU. Dave Inman VistaOne Corporation Dave.Inman@vistaone.com @v1DInman