Detecting Image Region Duplication Using SIFT Features
400 likes | 689 Views
Detecting Image Region Duplication Using SIFT Features. Xunyu Pan and Siwei Lyu Computer Science Department University at Albany State University of New York. March 16, ICASSP 2010 Dallas, TX. An Example of Image Region Duplication.

Detecting Image Region Duplication Using SIFT Features
E N D
Presentation Transcript
Detecting Image Region Duplication Using SIFT Features Xunyu Pan and Siwei Lyu Computer Science Department University at Albany State University of New York March 16, ICASSP 2010 Dallas, TX
An Example of Image Region Duplication Forgeries appeared on the front page of The Los Angeles Times, The Financial Times, The Chicago Tribune and The New York Times
An Example of Image Region Duplication Original image Tampered image
Outline • Motivation • Related Works • Detection Method • Experimental Results • Discussion and Future Work
Motivation • Region duplication is a common manipulation used in image tampering • Most existing methods based on finding exact copies of pixel blocks • They are not effective for geometric and illumination adjustments over the regions • We propose a new method to detect such more complicated region duplication
Outline • Motivation • Related Works • Detection Method • Experimental Result • Discussion and future work
Related Works • Majority of previous works focus on detecting copy-move forgeryproblems • The methods used are based on comparing pixel blocks (exhaustive search) • Most methods reduce computation by using low dimensional representations of blocks • [Popescu and Farid,04]and [Luo, et al.,06] use PCA to reduce computation • [Fridrich, et al.,03] uses DCT to reduce computation • [Huang, et al.,08] uses invariant image features to detect copy-move region duplication
Simple copy-move Original Image Image tampered using copy-move
Outline • Motivation • Related Works • Detection Method • Experimental Results • Discussion and Future Work
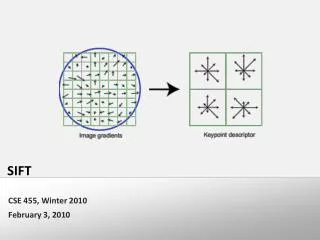
Major Steps of the Proposed Method • STEP 1: Scale Invariant Feature Transform (SIFT) keypoint detection • STEP2: SIFT keypoint matching and manipulation transform estimation • STEP3: Obtaining duplication map
SIFT Keypoint • SIFT (Scale Invariant Feature Transform) was originally proposed by [Lowe, 99] and further optimized in [Lowe, 04] • SIFT keypoints detected on a tampered image
Major Steps of the Proposed Method • STEP 1: Scale Invariant Feature Transform (SIFT) keypoint detection • STEP2: SIFT keypoint matching and manipulation transform estimation • STEP3: Obtaining duplication map
Keypoints Matching • Best-Bin-First (BBF) algorithm [Beis, 97] is used to match similar keypoints • Selection criteria: The best match f’ of keypoint f should be far more close (Euclidean distance) than all the other matches
Estimation of Manipulation Transform • Copy-move • Compute Euclidean distance for each keypoint correspondence • Shift vector is estimated by the distance with maximum frequency of occurrence Shift Vector:
Estimation of Manipulation Transform • Scaling • Compute ratio of Euclidean distance between corresponding keypoint pairs • The ratio with the maximum frequency is used as an estimation of the scale factor Scale Factor
Estimation of Manipulation Transform • Rotation • Keypoint represented by a local coordinate systems consists of three non-collinear keypoints • Transform is estimated based on the same set of coordinates in the coordinate system Local Coordinate System
Major Steps of the Proposed Method • STEP 1: Scale Invariant Feature Transform (SIFT) keypoint detection • STEP2: SIFT keypoint matching and manipulation transform estimation • STEP3: Obtaining duplication map
Obtaining Duplication Map • A perspective image is generated from the original image using the estimated parameters Tampered Image Perspective Image
Obtaining Duplication Map (cont.) • Both images are then segmented into overlapping 4 × 4 pixels contour blocks • A correlation map can be generated by computing the correlation coefficient between each pair of corresponding contour blocks in original and perspective image respectively
Obtaining Duplication Map (cont.) • Apply 7 × 7 Gaussian filter to smooth the correlation map • Binarize the correlation map using a preset threshold • Remove small isolated regions caused by noise using a pre-given area threshold • The final contour is connected using mathematical morphological operations [Suzuki, 85] • Erosion and Dilation
Outline • Motivation • Related Works • Detection Method • Experimental Results • Discussion and future Work
Qualitative Testing Results • We define two quantitative measure of performance based on the detection accuracy and false positives • Pixel detection accuracy (PDA) • Pixel false positive (PFP)
Copy-move Tampered image using copy-move PDA = 91.3%, PFP = 0.3%
Scaling Tampered image using scaling factor: 1.2 PDA = 93.4%, PFP = 1.2%
Rotation Tampered image using rotation: 60⁰ PDA = 81.4%, PFP = 1.9%
Qualitative Testing Results (cont.) Possible duplicated regions confirmed by inspection of photography experts Detected duplicated region using our method
Qualitative Testing Results (cont.) Forgeries generated with using the Smart Fill tool [Alien Skin Software LLC]
Quantitative Testing Results • An image database of tampered color images of 720 × 436 pixels which are originally captured by Nikon D100 digital camera • In each image, a random square region of size 64 × 64 pixels (1.3% of the original image) or 96 × 96 pixels was copied and pasted onto a random position in the same image
Robustness and Sensitivity on JPEG and Noise Average detection accuracies and false positives (both in percentage) on100 testing images.
Outline • Motivation • Related Works • Detection Method • Experimental Results • Discussion and Future work
Summary • In this work, we propose an efficient technique to detect region duplication in digital images based on the matching of SIFT features • Compared to previous methods, our method is effective to the detection of duplicated regions undergone geometric and illumination adjustments • Experimental results with several credible forgeries demonstrate the efficacy of our method
Discussion • Advantages • Reliably detect duplicated regions that are geometrically distorted • Robust to general image degradations caused by JPEG compression or additive noise • Efficient running time – analyzing images of normal size takes about 10 seconds on a computer of Intel 2.0GHz processor with 2 GB memory • Limitations • The specific manipulation transform must be known before the detection, which is usually impracticable • Detection performance reduces as the duplicated regions become smaller or homogeneous (e.g. sky) • Certain distortion of the duplicated region (e.g., extreme scaling or reflection) can affect the invariance of the SIFT features.
Future Work • Convert the algorithm into a plug-in for Photoshop, so that it can become part of the image forensic examiner’s toolkit • Detecting forged image created by duplicated regions from original image with statistical similarity (e.g., texture synthesis)