Exploiting Instruction Streams To Prevent Intrusion
190 likes | 432 Views
Exploiting Instruction Streams To Prevent Intrusion. Milena Milenkovic. Outline. Introduction Related Work Trusted Instruction Execution Framework The Framework Potential Conclusion. Introduction. Most of today’s computers connected to Internet,

Exploiting Instruction Streams To Prevent Intrusion
E N D
Presentation Transcript
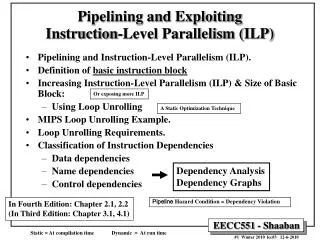
Exploiting Instruction StreamsTo Prevent Intrusion Milena Milenkovic
Outline • Introduction • Related Work • Trusted Instruction Execution Framework • The Framework Potential • Conclusion
Introduction • Most of today’s computers connected to Internet, • Even more in the future, including embedded devices • One of the major security problems: the execution of the unauthorized code • A lot of applications may be vulnerable • Attack examples: • buffer overflow (heap, stack) • format string attack • …
Introduction • Stack-smashing
Introduction • One solution: allow only execution of trusted instructions • Trusted instructions – with a valid signature • Previous research:limited number of instruction streams(dynamic basic blocks) • Use basic block signatures:run-time verification of the last basic block in an instruction stream • Signatures calculated during trusted installation
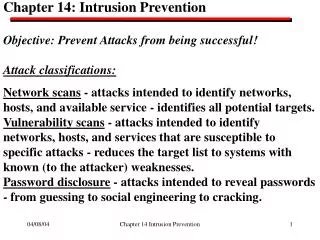
Related Work • Two categories: • Static source code analysis • Dynamic detection/prevention • Static code analysis: false alarms • Dynamic • Secure Program Execution Framework (SPEF) • Tag “spurious” data • Monitoring program “behavior” (system calls, performance monitoring registers) • Split stack for data/addresses, or secure stack • Compilers, compiler and library patches
Related Work • Most related – SPEF: a given program binary has numerous representations with the same functionality • During installation, each instruction block is transformed; verified in the run-time • compute transformation-invariant hash of the instruction block • encrypt the hash value with the secret key • use encrypted value to select a transformation (e.g., a particular instruction order in case of instruction scheduling) • 7.5%-17.1% increased execution time, Mediabench • Also related: tamper-proof techniques, but different granularity
Trusted Instruction Execution • Requirements: • prevent the execution of unauthorized code • the security features should not significantly increase the program execution time • This project: proposes a framework that satisfies requirements
Trusted Instruction Execution • Atomic code unit protected by its signature: a basic block • Verify all basic blocks? • It is enough to verify the signatureof the last basic block (LBB) in the instruction stream, when LBB generated a cache miss • Signatures on hard disk: encrypted
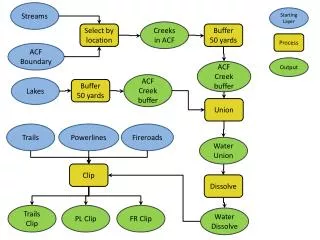
Code BBST_M Heap Stack Architecture for Trusted Computing BBST – Basic Block Signature Table BBST_M – Basic Block Signature Table (Memory) BBSVU – Basic Block Signature Verification Unit MMU L1D Datapath L1I FPUs IF BBST Control BBSVU
Signature Generation • MISR (Multiple input signature register) • Linear feedback coefficients – based on the processor secret key
Phases of the Security Mechanism • Compilation and program installation • Signature table (BBST_M) is generated, encrypted and appended to the program binary • Program loading in the memory • BBST_M is decrypted, loaded in the memory • Program execution • Signature of each last basic block with cache miss is verified • If no match, generate trap to OS – kill process
The Framework Potential • 32-bit MISR • I-cache: 4 ways, 128 sets, 64B line • BBST: 4 ways, 4B line, 128/256 sets • LRU replacement • Traces of SPEC CPU2000 benchmarks for Alpha architecture • F2B, M2B segments • 10 integer (CINT), 11 floating-point benchmarks (CFP)
The Framework Potential • Also measured; • the number of instruction cache misses • the number of BBST accesses • The number of BBST misses – very small • Trusted instruction overheadwill not significantly hurt performance
Conclusion • Proposed a framework for trusted instruction execution,evaluated potential • Promises to be faster than SPEF, with additional hardware resources and BBST appended to program binary • Future work: • asses different BBST organizations • preload BBST? • simulate execution time • evaluate an alternative implementation:signature embedded in the code