Chapter 6
Chapter 6. Networking Protocols. Introduction. Topics Protocol Basics Protocol Characteristics Transmission Control Protocol/Internet Protocol Network Access Layer Protocols Internet Layer Protocols Transport Layer Protocols Application Layer Protocols. Protocol Basics.

Chapter 6
E N D
Presentation Transcript
Chapter 6 Networking Protocols
Introduction • Topics • Protocol Basics • Protocol Characteristics • Transmission Control Protocol/Internet Protocol • Network Access Layer Protocols • Internet Layer Protocols • Transport Layer Protocols • Application Layer Protocols
Protocol Basics • A protocol is a set of rules that determines how computers exchange information over a network medium • A wide variety of communication protocols exist, and many of them rely on others for operation • Groups of related protocols are often called stacksorprotocol stacks
Protocol Characteristics • Data packets can be sent over a medium using any one of a number of protocols • Protocols can be either standard or proprietary • Standard protocols • Support universal communication so equipment from different manufacturers can interact
Proprietary Protocols • Proprietary protocols are vendor specific and are usually protected by patents or other legal stipulations • Proprietary protocols include • XNS • NetBIOS • IPX/SPX • AppleTalk • DECNet
Xerox Network System (XNS) • XNS is a suite of protocols created by Xerox in the late 1970s for Ethernet networks • XNS is rarely used in new networks today
NetBios • The Network Basic Input/Output System (NetBIOS) interface was developed in 1983 for IBM • The intention was to allow applications on different computers to communicate within a local area network • NetBIOS was not designed for large networks
IPX/SPX • Novell introduced Internetwork Packet Exchange/Sequenced Packet Exchange (IPX/SPX) in the early 80s • This stack was based on the XNS network protocol family • IPX is the Network layer protocol • SPX is the Transport layer protocol
AppleTalk • AppleTalk is Macintosh’s networking protocol • It is designed to be a flexible, simple, and inexpensive network means for connecting computers, peripherals, and servers • Newer versions of Macintosh operating systems use TCP/IP and SMB as default protocols rather than AppleTalk • AppleTalk is a protocol and LocalTalk is a media type
DECnet • DECnetis a proprietary network protocol designed by Digital Equipment Corporation • Currently two versions of DECnet are in use: • DECnet Phase IV which is based on the Phase IV Digital Network Architecture (DNA) • DECnet/OSI also called DECnet Phase V is a layered model
Transmission Control Protocol/Internet Protocol • TCP/IP is considered the language of the Internet • It is the most widely used protocol today • It is a suite, or stack, of small, specialized protocols • Because of its routing ability, TCP/IP has become the standard for many LANs, as well as for the Internet
Transmission Control Protocol/Internet Protocol • In the early 1970s, the Department of Defense funded ARPA to design a new set of computer communication protocols that would allow multiple networks to be interconnected in a flexible and dynamic way • The protocol developed was originally called Network Control Protocol • This success led to the implementation of the two main Internet protocols • These are Transmission Control Protocol and Internet Protocol (TCP/IP)
Transmission Control Protocol/Internet Protocol • The TCP/IP suite maps the seven layers of the OSI model to a four-layer model • The TCP/IP model focuses more on interconnectivity than on functional layers
Transmission Control Protocol/Internet Protocol • The TCP/IP model is also called the Internet reference model • Layers • Network Access • Internet • Transport • Application
Network Access Layer Protocols • The Network Access layer is the lowest layer in the model • It Maps to Layers 1 (Physical) and 2 (Data Link) of the OSI model • It is responsible for the framing (DL) and physical delivery of datagrams
Network Access Layer Protocols • Access Layer Protocols deliver data to computers and devices on the network • These include Serial Line Interface Protocol (SLIP) and Point-to-Point Protocol (PPP) • These protocols support serial data transmission over a modem
Network Access Layer Protocols • Other Network Access protocols • the Address Resolution Protocol (ARP) • the Reverse Address Resolution Protocol (RARP) • Provide a means of mapping IP addresses to MAC addresses • These protocols provide a means for last hop message delivery
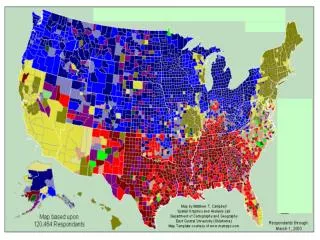
Internet Layer Protocols • The layer above the Network Access layer is called the Internet layer • It manages the routing of packets that are to be forwarded on to different networks • It relies on routable protocols for delivery
Internet Layer Protocols • The Internet Protocol (IP) is responsible addressing and routing of data packets • Routing tables created by routing protocols are used to forward messages from one network to another • It is a low overhead, best effort delivery protocol
The Internet Layer Protocols • IP • ICMP • ARP • RARP
IP Message Format • IP Packets or datagrams consist of a header, data (payload), and a trailer • The header contains routing information • Trailers contain a checksum value, which is used to determine if data was corrupted during transmission
Packet Delivery • IP compares the destination address in the packet header to router table addresses • If the address corresponds to a local network, the datagram is delivered to the appropriate computer • If the address corresponds to a remote network, the packet is passed to a router for delivery
Routing Controls • Time to Live (TTL) • prevents packets from circulating on the network forever • The TTL value is decremented by one each time the packet traverses a router (each hop) • Default value is usually 120 • Fragmentation – Routers may break oversize packets into fragments, then route the individual fragments, which are reassembled at the destination computer
Fragmentation • Each subnetwork has a maximum transmission unit (MTU), which is the largest packet it can transfer • A datagram received from one network may be too large to be transmitted as a single packet on another network • Fragmentation is the process of dividing a packet into smaller pieces
Internet Control Message Protocol • ICMP • Internet layer protocol • uses IP to send its messages • uses IP as if it was higher-level protocol • used as an aid for other protocols • used to test for connectivity and search for configuration errors in a network
ICMP Error Messages • Destination Unreachable – message returned to sender if a router cannot forward an IP datagram • Buffer Full – message returned until congestion due to full buffer has abated • Hops – an IP datagram has passed through its allotted number of routers • Ping – ICMP echo messages are returned to sender if destination exists and is reachable • Traceroute – ICMP timeouts used to discover path a packet takes as it traverses an internetwork
PING • Used to test connectivity • uses the ICMP echo function • A small packet containing an ICMPecho message is sent through the network to a particular IP address • The computer that sent the packet then waits for a return packet • If the connections are good and the target computer is up, an echo message is returned to the sender
Traceroute • Originally developed for the Unix operating system • used to track the path a packet takes from sender to destination • Calculates travel time for each hop • uses an ICMP echo request packet to determine the path
Transport Layer Protocols • The protocol layer above the Internet layer • provides a reliable communication service so that extended two-way conversations may take place • responsible for providing end-to-end data integrity
Transport Layer Protocols • Transmits data as a stream of characters • initiates and terminates the connections between sender and receiver • Two main protocols • Transmission Control Protocol (TCP) • User Datagram Protocol (UDP)
Transmission Control Protocol (TCP) • provides connection-oriented data transmission • supports multiple data streams • provides for flow and error control • uses sequence numbers and acknowledgements to guarantee delivery
TCP Connections • TCP communications are port to port • A socket is an IP address plus a port number • Well-defined port numbers have been assigned to common applications
Port Numbers • Used to communicate with upper layers by keeping track of conversations with different services (applications) • Well-Known port numbers define different application locations on the server that hosts the applications
User Datagram Protocol (UDP) • a connectionless protocol • Low overhead - does not provide either sequencing or acknowledgements • used a lot in telephony traffic and the Remote Procedure Call (RPC) • UDP does not provide the reliability that TCP provides
Application Layer Protocols • The top layer in the Internet reference model • Provides applications access to network services
ApplicationLayer Protocols • Telnet – remote client access to resources on a Telnet server • FTP – reliable file transport using TCP; requires authentication • TFTP – Unreliable file transport using UDP • NFS – allows file sharing on different platforms • SMTP – delivers mail to a server; use POP or IMAP to retrieve mail • LPD – for printer sharing • X Window – graphical interface for client/server applications • SNMP –Provides network management by polling capable devices • DNS –maps host names to IP addresses • DHCP – provides IP address configuration to workstations
File Transfer and Remote Access • File Transfer Protocol (FTP) which allows files to be uploaded and downloaded on port 21 • Telnet which uses terminal emulation for access to remote hosts using port 23 • Both FTP and Telnet use TCP as their Transport layer protocol
Mail and Internet • Simple Mail Transfer Protocol (SMTP) which supports basic message delivery services to mail servers on port 25 • HyperText Transfer Protocol (HTTP) which is a low-overhead Web browser service protocol that uses port 80
Management and News • Simple Network Management Protocol (SNMP) which uses UDP port 161 to collect information from network devices. • Network News Transfer Protocol (NNTP): handles distribution and posting of news articles using port 119
Address Assignment and Name Mapping • Dynamic Host Configuration Protocol (DHCP) allows for automatic IP addressing • Domain Name Service (DNS) uses UDP port 53 for resolving domain names to IP addresses