Enhancing Content Protection in P2P Networks: An Implementation Architecture
This paper discusses an innovative implementation architecture for content protection within peer-to-peer (P2P) networks. Addressing the critical issues of access control, security, and scalability, the authors propose an effective framework for monitoring user behavior and tracing piracy. By integrating content packing, right agents, and right certificates, this architecture enhances the security of digital media distribution. The presentation highlights the need for robust security measures while balancing centralized and distributed approaches to ensure the effective protection of digital content.

Enhancing Content Protection in P2P Networks: An Implementation Architecture
E N D
Presentation Transcript
The Implementation Architecture of Content Protection in P2P Network Authors: Cheng Yang, Jianbo Liu, Yichun Zhang, and Aina Sui Source: 2007 International Conference on Computational Intelligence and Security Workshops, pp. 455-458, 2007 Speaker: Shu-Fen Chiou (邱淑芬)
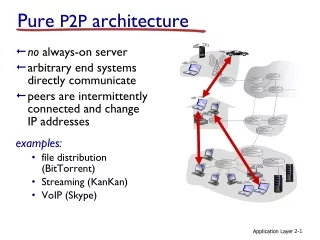
Introduction C 1. Request a.mp3 A B requester 4. Dowload E G D F a.mp3 responder
Introduction • Content protection • Access control • Security • Scalability • Behavior monitor and piracy tracing
PCP System Responder Requester
Comments • Think about contents usage times. • More security requirements should be considered. • Centralized and distributed.