Semantic Trust Management System: Integrating Reputation-based Decisions
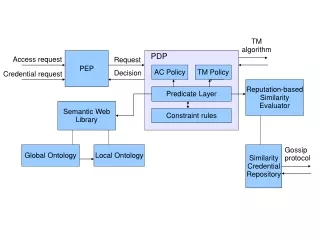
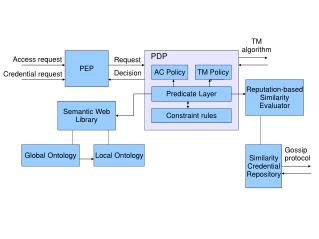
This project integrates trust management algorithms, credential repository, similarity evaluation, and gossip protocols to enhance reputation-based decision-making. By integrating components and extending the PDP, the system assesses similarity, exchanges credentials among peers, and makes decisions based on reputation. The interface includes Java/Prolog and interfaces with XACML/SAML for secure communication.

Semantic Trust Management System: Integrating Reputation-based Decisions
E N D
Presentation Transcript
TM algorithm PEP PDP Access request Request AC Policy TM Policy Decision Credential request Reputation-based Similarity Evaluator Predicate Layer Semantic Web Library Constraint rules Global Ontology Local Ontology Similarity Credential Repository Gossip protocol
What is done • PDP • SWI-Prolog (http://www.swi-prolog.org/) • Credential repository • PostgreSQL (http://www.postgresql.org/) • Request Format • XACML + SAML Profile (http://www.oasis-open.org/committees/tc_home.php?wg_abbrev=xacml)
Project 1b&2b Project 2a XACML Project 1a SWI Prolog SWI Prolog TM algorithm PEP PDP Access request Request AC Policy TM Policy Credential request Decision Reputation-based Similarity Evaluator Predicate Layer Semantic Web Library Constraint rules Project 3a Global Ontology Local Ontology Similarity Credential Repository Gossip protocol Project 3b PostgreSQL
Project 1a (2 persons) • PEP and interface with PDP • Component that waits for requests (also from other computers) and forwards the requests to the PDP • Interface between this component and PDP • Translate XML requests into Prolog queries • Return decision made by the PDP to the PEP • Requirements • Format of request (XACML-based) to PEP • Ac: Subj, obj, action, list of creds. • Cred: Subj, Attr, list of creds. • Interface Java/Prolog • e.g., JPL (http://www.swi-prolog.org/packages/jpl/java_api/index.html)
Project 2a (2 persons) • TM Algorithms • Chain Discovery (RT algorithms) • Simulations in Distributed Systems • Requirements • Java interface between Prolog engines • No requirements on the msg exchange format at this stage of the project Reference Ninghui Li, William H. Winsborough, and John C. Mitchell. Distributed Credential Chain Discovery in Trust Management. Journal of Computer Security, volume 11, number 1, pp. 35-86, February 2003.
Project 1b&2b (4 persons) • Integrate 1a and 2a • Integrate the TM Algorithm into the PEP-PDP • Request of remote credentials specified as XACML/SAML requests • Credential Issuing • XACML/SAML
Project 3a (3 persons) • Extend the PDP with a component for reputation-based decisions • Component for assessing the similarity between two concepts • Retrieve similarity credentials from the repository • Implement similarity metrics • Interface between PDP and this component
Project 3b (3 persons) • Design a protocol for the exchange of similarity credentials among peers. • Gossip protocols • Reference • A. Demers, D. Greene, C. Hauser, W. Irish, J. Larson, S. Shenker, H. Stuygis, D. Swinehart, D. Terry, “Epidemic algorithms for replicated database maintenance”, Proc. ACM Symp. on Principles of Distributed Computing, 1987. • S. Hedetniemi, S. Hedetniemi, A. Liestman, “A survey of gossiping and broadcasting in communication networks”, Networks 18(1988).