Exploit: Password Cracking
Exploit: Password Cracking. An Overview on Password Cracking. Password cracking is a term used to describe the penetration of a network, system, or resource with or without the use of tools to unlock a resource that has been secured with a password. Introduction.

Exploit: Password Cracking
E N D
Presentation Transcript
An Overview on Password Cracking Password cracking is a term used to describe the penetration of a network, system, or resource with or without the use of tools to unlock a resource that has been secured with a password
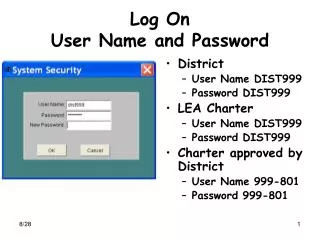
Introduction • System vulnerabilities with passwords • Strong passwords Vs Weak • Examples of vulnerabilities • Applications • FTP, HTTP, Telnet • Password Cracking Tools • Tools in Common • Brutus Password Cracker
Experiment on Password Cracking • Platform : Windows. • Setting up of machines with services • Target Machine (Server) • Client
Setting up of Machines DHCP/Switch Client FTP-Serv-U Brutus Ethereal. 192.168.1.3 (Word List) 192.168.1.2 (Word List) 192.168.0.172 (BruteForce) 192.168.0.125(BruteForce)
About Brutus Password Cracker: • Supported Applications • Telnet, FTP, HTTP • Methods used to engage with Remote machine • Word List • Combo • BruteForce
Engaging Remote Machine Using “Word List” The Method: - Creates many number of combinations of Possible System passwords from two separate files“users” and “word”. - Engages remote machine enter word after word, at high speed, until a match is found.
statler waldorf admin administrator Sample Entries for File “word” aaa abc123 academia academic Engaging Remote Machine using “Word List” Sample Entries for File “users”
Engaging Remote Server using “Combo” • The Method: • Similar to “Word List” • Uses “combo” file to generate combinations passwords for each users of the remote system. • Uncertain; Needs more guessing • Sample “combo” file Entries • admin:admin1 • admin:admin12 • admin:admin123
Engaging Remote Server using “BruteForce” The Method: - Guaranteed to some extent -Relies purely on power and repetition - Need very high processing speed - Produces many number of passwords for a particular user using permutations and combinations - May take months years to crack the password
Examples of Generated passwords: • aaa, aab, aac... aaA, aaB, aaC... aa0, aa1, aa2, aa3... aba, aca, ada.. • Each of the combinations of characters and symbols is fed through the appropriate cryptographic algorithm and compared to the stored password until a match is found.
Engaging Remote Machine Using “BruteForce” A sample display on initial settings just before engaging.
Engaging Remote Machine Using “BruteForce” A sample display on initial settings just before engaging.
Engaging Remote Machine Using “BruteForce” Sample display on cracked password