Security Standards under Review for esMD
260 likes | 408 Views
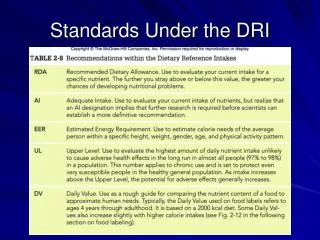
Security Standards under Review for esMD. Transaction Timeline. CAQH CORE Metadata. CAQH CORE/ XD* Metadata. X12 58 Signature. WS-Security. WS-Security. X12 58 Signature. DSG Signature. XD* Metadata. Encryption (transport level). DSG Signature. Content packaged into payload.

Security Standards under Review for esMD
E N D
Presentation Transcript
Transaction Timeline CAQH CORE Metadata CAQH CORE/ XD* Metadata X12 58 Signature WS-Security WS-Security X12 58 Signature DSG Signature XD* Metadata Encryption (transport level) DSG Signature Content packaged into payload Message created Message Sent Message Received Process Header Process Payload Process Content Store Content Electronic Content Created Content Stored as a document Internal Systems Internal Systems Gateway Internet Gateway An esMD transaction begins with the creation of some type of electronic content (e.g. X12 274, 277, or 275 message or an HPD Plus DSML, CDA, or PDF document). As the content is packaged into a message and sent, security elements are added at points along the timeline dependent on the standard(s) selected and the purpose of the security element. This process is reversed on the receiving end.
IHE DSG Transaction Structure The Document Digital Signature (DSG) content profile specifies the use of XML Advanced Electronic Signatures (XAdES) for documents that are shared between organizations. Process Flow for Phase 1 Sending Medical Documentation
Extensions to Metadata Transaction Structure This approach would extend existing metadata to support the exchange of the required security information. For esMD, this would require extensions to CAQH CORE and XD* metadata. We would need to work with the relevant organizations to seek inclusion of these changes in future specifications. Process Flow for UC1 Registration
X12 58 Transaction Structure This standard defines the data formats for authentication, encryption, and assurances in order to provide integrity, confidentiality, and verification and non-repudiation of origin for two levels of exchange of EDI formatted data defined by ASC X12. Process Flow for UC1 Registration
WS-Security Transaction Structure This specification extends SOAP Messages to provide three main security capabilities: the ability to send security tokens as part of a message, message integrity, and message confidentiality. Process Flow for UC1 Registration
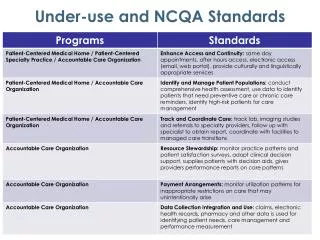
Phase 1: Requirements for Sending Electronic Medical Documentation
Use Case 1: Transaction Process Flow Delegation of Rights Artifact Signature of Registration Request Public Certificate of Registration Requestor Delegation of Rights Artifact Registration Request Message Signature of Assertion Registration Request Public Certificate of Assertor Assertion of Rights
Use Case 2: Transaction Process Flow eMDR Message Signature of eMDR Public Certificate of Payer/Payer Contractor eMDR
Phase 1: Transaction Process Flow Signed Medical Document Bundle Signature of Document Bundle eMDR Response Message Public Certificate of Document Bundle Owner Signature of eMDR Response Medical Document Bundle Public Certificate of eMDR Consumer Document Bundle Attachment eMDR Response
Appendix: Security Dataset Requirements for both Registering to Receive eMDRs & Sending eMDRs
Signature Artifact The Signature Artifact (paired with the Public Digital Certificate of the Sender) will enable the message receiver to authenticate the sender, verify message integrity, and prove non-repudiation. Public Digital Certificate of Sender – x.509 certificate issued by a Certificate Authority Signature Artifact – Encrypted hash of the message* * The exact details of the Signature Artifact are being developed in the esMD Author of Record Initiative.
Signature Artifact Example Private Key of Dr. Smith Registration Request Provider Name: Dr. Smith NPI: 987654 Service: Receive eMDRs checksum function Hash: 987654 signing algorithm Metadata Encrypted Hash: H8K9QTP Public Digital Certificate of Dr. Smith 2. Payer verifies the Request came from Dr. Smith and has not been tampered with Registration Request Provider Name: Dr. Smith NPI: 987654 Service: Receive eMDRs checksum function Hash: 987654 Verify Integrity signing algorithm Hash: 987654 Metadata Encrypted Hash: H8K9QTP Public Digital Certificate of Dr. Smith Public Key of Dr. Smith 1. Dr. Smith attaches signature artifact to Request to Register to Receive eMDRs Verify Identity
Delegation of Rights Artifact The Delegation of Rights Artifact (paired with the Public Digital Certificate of Subject) enables the Subject to delegate a right to the Sender of a Request such that the Receiver can cryptographically confirm that delegation of rights has occurred. Public Digital Certificate of Subject – x.509 certificate issued by a Certificate Authority Delegation of Rights Artifact – Encrypted hash of an assertion of rights* * The exact details of the Delegation of Rights Artifact are being developed in the esMD Author of Record Initiative.
Delegation of Rights Example (1/2) Private Key of Dr. Smith Assertion of Rights Dr. Bob Smith gives Medical Data, Inc. the right to register his NPI to receive eMDRs. Expiration Date: 1/1/2013 checksum function Hash: 123456 signing algorithm Metadata Encrypted Hash: U37G90P 2. Medical Data, Inc. include their Signature Artifact, Dr. Smith’s Delegation of Rights Artifact, and both Public Digital Certificates in their Request to Register Dr. Smith to Receive eMDRs Registration Request Provider Name: Dr. Bob Smith NPI: 987654 Service: Receive eMDRs Metadata Encrypted Hash: H8K9QTP Public Digital Certificate of Medical Data, Inc. Delegation of Rights Artifact Public Digital Certificate of Dr. Smith 1. Dr. Smith delegates the right to register his NPI to receive eMDRs to Medical Data, Inc.
Delegation of Rights Example (2/2) 3. Payer verifies Medical Data, Inc. has the right to register Dr. Smith to receive eMDRs Registration Request Provider Name: Dr. Bob Smith NPI: 987654 Service: Receive eMDRs Metadata Encrypted Hash: H8K9QTP Public Digital Certificate of Medical Data, Inc. Delegation of Rights Artifact Public Digital Certificate of Dr. Smith Assertion of Rights Dr. Bob Smith gives Medical Data, Inc. the right to register his NPI to receive eMDRs. Expiration Date: 1/1/2013 checksum function Hash: 123456 Metadata Encrypted Hash: U37G90P Hash: 123456 signing algorithm Verify Right Public Key of Dr. Smith