Cryptographic Voting Protocols: A Systems Perspective
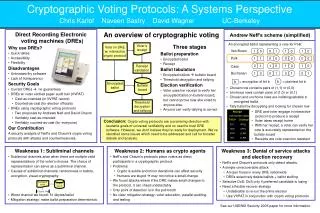
This paper presents a thorough analysis of cryptographic voting protocols, particularly focusing on Neff's and Chaum's revolutionary schemes. The authors, Chris Karlof, Naveen Sastry, and David Wagner, highlight significant vulnerabilities in the implementation of these protocols within holistic voting systems. The motivation lies in understanding the weaknesses and assessing new challenges for secure electronic voting. They cover topics like coercion resistance, subliminal channels, and human unreliability, providing countermeasures and discussing future work for enhancing secure voting systems.

Cryptographic Voting Protocols: A Systems Perspective
E N D
Presentation Transcript
Cryptographic Voting Protocols: A Systems Perspective By Chris Karlof, Naveen Sastry, and David Wagner University of California, Berkely Proceedings of the 14th Usenix Security Symposium held in Baltimore on July 31st-August 5th, 2005 Presenter: Rick Carback 11-16-05
Selection Criteria Motivation Results New and Significant Goals of Secure Voting Systems Neff’s Protocol Attacks and Mitigations Subliminal Channels Human Unreliability Denial of Service Secure Voting Protocol Implementation Future Work Conclusions Overview
Paper Selection Criteria • Chris Karloff and Naveen Sastry are both 5th year graduate students. • David Wagner • DIMACS Special Focus on Security Organizing committee member • ACM CCS 2004 Program committee member • USENIX Security 2006 Program committee member • IEEE Security & Privacy 2006 Program committee member
Motivation • Chose protocols by Neff and Chaum because they are revolutionary • Viewed Neff and Chaum protocols as part of a complete voting system • What are the weaknesses of these schemes in complete systems if implemented? • Can these ideas work in the real world?
New and Significant • Enumerates E-Voting goals • Analysis of Cryptographic Protocols in the larger systems context • Exposes weaknesses in implementation of cryptographic protocols • Provides countermeasures for these weaknesses • Identified new challenges and open problems in electronic voting systems.
Goals of Secure Voting Systems • Cast-as-Intended • Counted-as-Cast • Verifiability • One voter, One vote • Coercion Resistance • Privacy
Neff’s Scheme • Distributed Key Generation Protocol (Similar to Chaum's Scheme) • DRE constructs a VC, a matrix of BMPs. Each row represents one candidate. • BMPs are all (0, 0) or (1, 1) for the chosen candidate and (0, 1) or (1, 0) for the others.
Neff’s Scheme (cont.) • DRE picks a pledge bit for each BMP for the chosen candidate, voter can verify by picking a side for each one. • OVC is created with this information. • Voter checks that challenge is correct on bulletin board.
Subliminal channels • Arises when DRE is free to chose the random values that are used. • All randomized encryption schemes can contain subliminal channels. (Goldwasser, 1984) • Through special selection of a random number r, the DRE can encode the sizeof(r) bits. • Can hide a bit by repeatedly choosing a random number until you get what you want. • Expected work is O(2x) to encrypt x bits.
Random Subliminal Channel Attack • Neff's scheme makes extensive use of randomness. • Each BMP has one side of it revealing the random parameter used in that side of the pair. • If the DRE chooses the same random parameter for both sides it will always be revealed in the ballot. • The random parameter is guaranteed to be revealed, allowing a number of bits equal to the size of the parameter to be sent subliminally for each BMP.
Avoiding Random Subliminal Attacks • Change protocol so that it does not require randomness • Very tricky • Random tapes • Trusted Hardware
Semantic Subliminal Channels • Voters are unlikely to detect subtle changes (fonts, pixel, etc) • Can use simple policy, no computational complexity • Apparent only after decryption, not on the bulletin board
Mitigating Semantic Channels • Unambiguous formats for ballots and all ballots tested for conformance • Bad ballots cannot be posted on the bulletin board • But this may violate other policies!
Human Unreliability • Protocol security hinges on DRE not knowing how the voter will make future decisions • Interactions must happen in a particular order • Voter may not notice deviations in protocol • Voter must monitor DRE output • Most people don’t care • People often make mistakes • How does a voter prove the machine is wrong?
Human Unreliability (cont.) • Discarded Receipts • DRE Generates Invalid Signature • Voter cannot prove if the receipt was forged • Printing incorrect DRE Machine ID • Ignoring voter input • Valid receipt, but not what voter chose
Mitigating Human Unreliability • Parallel Testing • Voter Education • It should not be so hard to use a voting machine • Shredders for receipts • Verify Signature at voting station • Needs another set of trusted software/hardware • Preprinted Machine IDs
Denial of Service • Malicious DREs can delete, alter, or stuff ballots • Detectable, but still effective • Malicious Tallying/Bulleting Board software • Could delete keys, ballots, etc. • Could be selective • Target polling stations favoring undesired candidate
DoS Mitigation Strategies • Revote • Costly • Voter Verified Paper Audit Trail • Not secure
Implementing Secure Voting Systems • Bulletin Board • Required Properties? What Architecture? • BSN Assignment • User Friendly Interfaces • Tallying Software Specification
Future Work • Cryptographic protocols that prevent subliminal channels • Mix-net security models • Definition for security in the voting setting • Humans as protocol participants • Can we educate without discouraging participation and hurting trust?
Conclusions • Every attack discussed requires malicious software (DRE/bulletin board/tallying) • Is this better than what we currently have? • What about non-malicious problems? • Connectivity? • Hardware failure?
References • Votehere.com • “Cryptographic Voting Protocols: A Systems Perspective”, Chris Karlof, Naveen Sastry, David Wagner