Cryptographic Voting Systems (Ben Adida )
Cryptographic Voting Systems (Ben Adida ). Jimin Park Carleton University COMP 4109 Seminar 15 February 2011. “ If you think cryptography is the solution to your problem…. … then you don’t understand cryptography… …and you don’t understand your problem.” .

Cryptographic Voting Systems (Ben Adida )
E N D
Presentation Transcript
Cryptographic Voting Systems(Ben Adida) Jimin Park Carleton University COMP 4109 Seminar 15 February 2011
… then youdon’t understandcryptography……and you don’tunderstand yourproblem.”
Yet, cryptography solvesproblems that initiallyappear to be impossible.
There is apotential paradigm shift.A means ofelection verificationfar more powerfulthan other methods.
“But with cryptography, you’re just moving the black box. Few people really understand it or trust it.”Debra BowenCalifornia Sec. of State, 7/30/2008(paraphrased)
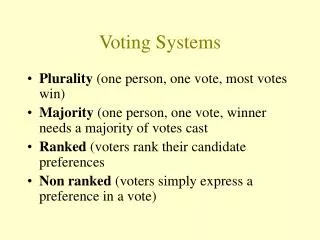
Problems with current voting systems • Rigged lever machine counters, lost ballot boxes or magically found, dead citizens’ votes.
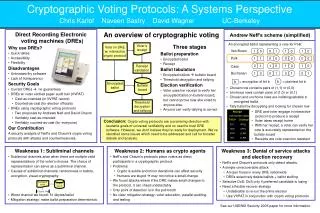
Why not fully computerize voting systems? • Bush vs. Gore (California, 2000) • Bush won by just 500 votes! • Known missing ballots, coercion • Computerization was taken seriously • Direct Recording Electronic (DRE) machines • Nothing but touch screen, automatic tallying • Problems with DRE, can we trust it? • Inherited risks of any computer systems (bugs, back door code, etc.) • Non-transparency Ref: [2] Avi Rubin
Dilemma: Verification vs. Secrecy • Analogy: ATM machines • Fully automated computerized system • Why do we trust them? • We can fully verify the transactions • Difference between ATM and Voting Systems • VS: information being verified must stay secret “Rely on mathematical proofs of the results – rather than of the machines.”
The Goal of Cryptographic Voting Systems • No: Chain-of-Custody approach (current) • Yes: End-to-End verification approach
Threshold Decryption • Need Public-key encryption system • Private keys used for decryption need to be distributed among the different parties • Shared-secret scheme E.g. ) A race of 3 candidates. Each given an equation of a plane (non-coplanar). Key resides at the point where all planes intersect. Ref: [3] Blakley, G. R.
What crypto system to use? • 3 desired properties of our crypto system • Public-Private key encryption-decryption • Voters encrypt • Candidates decrypt • Easily generated random keys • One vote encrypts to many different cipher-texts • Homomorphic • Cipher-texts (different votes) get aggregated to one cipher-text under certain operation (addition, multiplication, etc.) Ref: [4] Josh D. Cohen and Michael J. Fischer
Group Homomorphism Def: Given two groups (G, *) and (H, ·), group homomorphism from (G, *) to (H, ·) is a function h : G → H such that for all u and v in G it holds that h(u v) = h(u) · h(v) * In our case, the function h can be the encryption. encrypt(u v) = encrypt(u) · encrypt(v) *
El Gamal encryption: original Alice Bob (1) Bob computes + publishes: - p : large prime (p-1 has at least one large prime factor) - a : primitive element mod p - y : public key, y = a mod p x : private key, x = random(1, 2, …, p-1) (2) Alice encrypts : message m: 0 <= m <= p (c1, c2) = ( y , m · SK) mod p = ( a , m · (a ) ) mod p (3) Bob decrypts: (m · SK· SK ) mod p = (m · a · a ) mod p = m (voters) (candidates) x B B B Shared Key (SK) SK = (y ) = (y ) B B x A B x B A X X X A A B A -1 X X -X X A B A B Ref: [6] T. El Gamal
El Gamal example Alice Bob (1) Bob computes + publishes: - p : large prime (p-1 has at least one large prime factor) - a : primitive element mod p - y : public key, y = a mod p x : private key, x = random(1, 2, …, p-1) (2) Alice encrypts : message m: 0 <= m <= p-1 (c1, c2) = ( y , m · SK) mod p = ( a , m · (a ) ) mod p (3) Bob decrypts: (m · SK· SK ) mod p = (m · a · a ) mod p = m (voters) (candidates) p : 13 a : 2 11 y : 7 (2 mod 13) x B B B B x : 11 B B B m : 7 11 6 6 (c1, c2) = (2 , 7· (2 ) ) mod 13 = (12, 6) X X X A A B A 66 -66 -1 (7 · 2 · 2 ) mod 13 = 7 X X -X X A B A B Ref: [6] T. El Gamal
Comparison: RSA vs. El Gamal • Security • RSA: factoring large integers • El Gamal: discrete logarithms 3 ≡ 13 (mod 17) what is x? • Keys • RSA: expensive computation of finding p and q • El Gamal: computation of p and q is done once x
Homomorphic Tallying • Original El Gamal Enc(m1) · Enc(m2) = ( y , m · SK ) · ( y , m · SK ) mod p = ( y · y , (m · m ) · (SK · SK )) mod p = Enc( m · m ) 1 1 2 2 X X 2 1 2 1 2 1 X X 2 1 2 1 It would be more useful if we could do addition on the cipher texts rather than multiplication! • Exponential El Gamal Enc(m1) · Enc(m2) = ( y , a · SK ) · ( y , a · SK ) mod p = ( y · y , a · (SK · SK )) mod p = Enc(a ) m m 1 2 1 2 X X 1 2 (m + m ) 1 2 1 2 X X 1 2 (m + m ) 1 2
Let’s Vote! • Auditing the ballot - by zero-knowledge proof • Pick any two ballots to vote • “You” pick one of them and scratch to reveal random numbers -> private keys of the ballot • Take to election activist organization to scan 2D bar code and validate the ballot
Let’s Vote! (2) Vote (3) Remove candidate list (4) Shred random numbers, take home the receipt
Public Bulletin Board “The votes of the registered citizens were casted as intended and these votes are tallied properly, so we have counted as intended!”
Mixnets Ref: [7] David Chaum
Deployments • Numerous university student elections • MIT, Hardvard, etc. • UnversiteCatholique de Louvain: 25,000 voters • University of Ottawa: punchscan voting system • Takoma Park election, Maryland (Nov. 3. 2009) • Electing mayor, city councils, etc. • First binding governmental election
Ben’s Fear Computerization of voting is inevitable, without true verifiability, the situation is grim. Ben’s Hope Public auditing proofs will soon be as common as public-key crypto is now.
Quiz • What approach is current voting system taking? And what is this seminar’s proposed approach? • What is threshold decryption? • List the 3 desired properties crypto system should have for homomorphic tallying method? • What method is used to do ballot auditing? • In the voting process, the un-scratched random numbers are shredded in public view. What is the danger in revealing these numbers? What sort of benefit would a coercer have?
Reference [1] Ben Adida. Advances in Cryptographic Voting Systems. MIT. (2006). [2] Avi Rubin. An Election Day clouded by doubt, October 2004. http://avirubin.com/vote/op-ed.html. [3] Blakley, G. R. Safeguarding cryptographic keys. Proceedings of the National Computer Conference 48: 313-317, (1979). [4] Josh D. Cohen and Michael J. Fischer. A robust and verifiable cryptographically secureelection scheme. In FOCS, pages 372–382. IEEE Computer Society, 1985. [5] S. Poblig and M. Hellman, An improved algorithm for computing logarithms over GF(p) and its cryptographic significance, IEEE Transaction on Information Theory It-24:106-110, (1978). [6] T. El Gamal. A Public Key Cryptosystem and a Signature Scheme Based on Discrete Logarithms. IEEE Transactions on Information Theory 31, pg. 469-472. (1985) [7] David Chaum. Untraceable electronic mail, return addresses, and digital pseudonyms. Commun. ACM, 24(2):84–88, (1981).