Ternary Embedding Technique
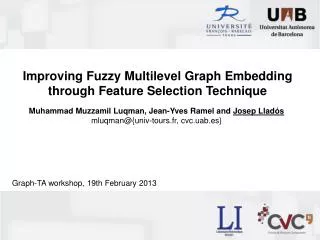
Ternary Embedding Technique. CHEN CHEN XIAOYU HUANG. Introduction of Steganography. A group of data hiding technique ,which hides data in undetectable way. Features extracted from modified images and original images have to be statistically undistinguishable

Ternary Embedding Technique
E N D
Presentation Transcript
Ternary Embedding Technique CHEN CHEN XIAOYU HUANG
Introduction of Steganography • A group of data hiding technique ,which hides data in undetectable way. • Features extracted from modified images and original images have to be statistically undistinguishable • Images, audio, video, text…..digital compressed images(JPEG)
Ternary Embedding Technique Popular steganographic: ME,MME(Binary computation) Improving existing steganogrphic data hiding methods by replacing the binary computation to ternary----ternary coefficients Higher information density Larger number of possible solutions Better solution with minimum distortion impact
JPEG was designed specifically to discard information that the human eye cannot easily see.
Partition image into 8x8 blocks, left-to-right, top-to-bottom • Compute Discrete Cosine Transform(DCT) of each block • Quantize coefficients according to psychovisual quantization tables • Order DCT coefficients in zigzag order • Perform runlength coding of bitstream of all coefficients of a block • Perform Huffman coding for symbols formed by bit patterns of a block
Discrete Cosine Transform(DCT) The first step reduces the dynamic range requirements in the DCT processing stage that followsV(i,j) is the dot of original image;F(0,0) is the Direct Current, other F(u,v) is Alternating Current
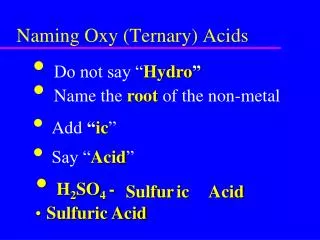
Quantisation • Quantisation is a process to transfer DCT coefficients to a smaller range. The purpose of quantisation is to reduce the non-zero coefficients’ amplitute and increase the number of zero coefficients(high frequency). • Quantisation is the main reason causes a picture’s quality drops.
Sq(u,v) is the result after quantisation • F(u,v)is the DCT coefficients • Q(u,v)is the quantisation table • Roundis the function to round up or down
Example Consider a 8x8 block using formula F(i,j)=V(i,j)-128, we get a block
Example • Using DCT, we get a result of • -415 is the Direct Current • Consider a quantisation table
Example • Using formula We get a result
Information Hiding in JPEG Coefficients • Information hiding into JPEG image adds more distortion beside the JPEG compression rounding errors: • Example: C’1=4.23, C’’1=4, r1=0.23
Information Hiding in JPEG Coefficients • A message M is to be embedded into C’, and the message embedded set is S. • We denote LSB(ci’’ ) as xi. If xi= mi, then si= ci. If xi≠ mi, then, • To minimize the absolute value of ri
Information Hiding in JPEG Coefficients • The distortion, di, is given by • Finally, the additional distortion eicaused by changing any single bit ci is given by • A goal in information hiding is to design embedding functions to minimizing the distortion
Modified Matrix Coding • The notation (t, n, k),where n = 2k − 1. denotes embedding kmessage bits into an nbit sized block by changing t bits of it. • Divides cover data C, into blocks of length n and message data M, into blocks of length k. • Matrix Coding: t=1 • Modified Matrix Coding: t>=1 • t≥1 is more efficient than t=1.
Matrix Coding-Example 1 • two bits x1, x2 • three modifiable bit places a1, a2, a3 • hanging one place at most. • In all four cases we do not change more than one bit
Matrix Coding • Parity check matrix (H): dependency between message bits and code word bits • Ex: k=3, n=2^k-1 = 7, H: 0 0 0 1 1 1 1 0 1 1 0 0 1 1 1 0 1 0 1 0 1 • X = H•CT p=binvec2dec(X⊕M) • Change pto embed message bits Cp = ¬Cp (1->0 and 0->1)
Example: • A cover block C = (1 0 0 1 0 0 0) • The message to be transmitted M=(1 1 0) Parity check matrix H= 0 0 0 1 1 1 1 0 1 1 0 0 1 1 1 0 1 0 1 0 1 We have X = H•CT = 1 0 1 • andp=binvec2dec(X⊕M) = 3 • Then we change the 3rd bit in the cover C, resulting in S = (1 0 1 1 0 0 0)
Modified Matrix Coding • For t = 2, we find pairs of numbers (β, γ) such that β ⊕ γ = p, there are (n−1)/2 such pairs which can be enumerated easily • For each of the pairs (βi, γi), the embedding error is given by one of four cases: • Find the pair (βi, γi) with the minimum ei
Modified Matrix Coding • Embedding error analysis • Embedding error Per changed coefficient
Modified Matrix Coding Modified matrix encoding (MME) always has several solutions and may choose the best one which causes the lowest distortion The number of possible solutions for MME NMME is computed as follows:
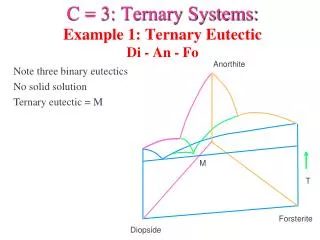
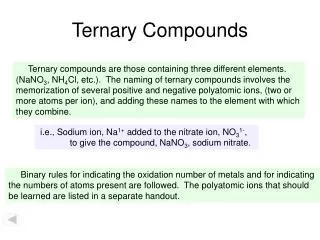
Ternary Data Hiding Technique • Improvement of MME. • converted to the ternary coefficients (i.e., 0,1,2)as follows: • Data hiding method uses vector v = (v1, v2, …, vn) (where n = 3m-1), Morg = H•vT; • for m = 2, the parity check matrix H: 0 0 1 1 1 2 2 2 1 2 0 1 2 0 1 2
Ternary Data Hiding Technique • modifying one coefficient (2 solutions): • C’(j+) = C(j+) + 1, index j+: • C’(j-) = C(j-) – 1, index j-: • modifying two coefficients (more solutions): • Required Morg, j+, j- • All two flip solutions: 4 groups • coefficients with indexes p1 and p2 modified according (+1,-1), (-1,+1), (+1,+1), (-1,-1)
Possible solutions • The number of all possible solutions for the proposed method NTE can be computed as follows: • More possible solutions than MME.
Distortion • Distortion can be computed as follows:
Encoder • For bitmap image I and binary message M: • Divide image into 8 by 8 blocks. Compute rounded DCT coefficients • Convert binary message M into ternary Mt. Find maximum m of • N is the number on non zero rounded DCT coefficients • Divide stream of computed ternary coefficients into blocks of n = 3m-1 coefficients. • Hide data to each block, rebuild a stego image.
Decoder: • For stego image Istegoprocess following: • Get the stream of modified DCT coefficients • Define stream of ternary coefficients. Divide stream of ternary coefficients to blocks of n = 3m-1 coefficients. • Recover the hidden message from each block using M = H•VT • Convert ternary hidden message to binary.
Experimental results • Tested by powerful steganalysis algorithm by T. Pevny and J. Fridrich [12]. • Simply, Ternary embedding is better.
References • Some Notes on Steganography, Ron Crandall, Friday, December 18, 1998 • F5—A Steganographic Algorithm, High Capacity Despite Better Steganalysis, Andreas Westfeld • Ternary Data Hiding Technique for JPEG steganography. Vasily Sachnev, Hyoung Joong Kim • Modified Matrix Encoding Technique for Minimal Distortion Steganography, Younhee Kim, Zoran Duric, and Dana Richards • Wikipedia