Formal Methods for Concurrent and Mobile Systems
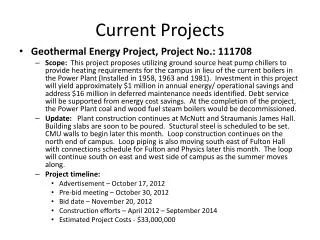
Explore formal methods for specification, verification, and implementation of concurrent and mobile systems, including the p-calculus and timed concurrent constraint language. Additionally, investigate security protocols and their properties using the spi-calculus. Lastly, study randomized algorithms for resource allocation in distributed systems.

Formal Methods for Concurrent and Mobile Systems
E N D
Presentation Transcript
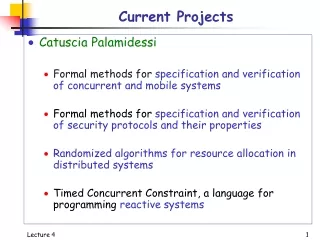
Current Projects • Catuscia Palamidessi • Formal methods for specification and verification of concurrent and mobile systems • Formal methods for specification and verification of security protocols and their properties • Randomized algorithms for resource allocation in distributed systems • Timed Concurrent Constraint, a language for programming reactive systems Lecture 4
1. Concurrent and mobile systems • Implementation of (a fragment of) the p-calculus, a small language for specification and verification of concurrent process which communicate via mobile links Lecture 4
1. Concurrency and mobile systems Example of link mobility U U Representation of systems whose Connection structure changes over time h U U h Lecture 4
2: Security protocols • Investigation of the spi-calculus, a small language to express and verify security protocols and their properties, like • Secrecy • messages, keys, etc. remain secret • Authentication • guarantees about the parties involved in the protocol • Non-repudiation • evidence of the involvement of the other party • Anonymity • protecting the identity of agents wrt particular events • Formal tools for automatic verification Lecture 4
Example: The dining cryptographers An example of achieving anonymity Crypt(0) notpays.0 pays.0 Master Crypt(1) Crypt(2) Lecture 4
The dining cryptographers • The Problem: • Three cryptographers share a meal • The meal is paid either by the organization (master) or by one of them. The master decides who pays • Each of the cryptographers is informed by the master whether or not he is paying • GOAL: • The cryptographers would like to know whether the meal is being paid by the master or by one of them, but without knowing who is paying (if it is one of them). Lecture 4
The dining cryptographers: Solution • Solution: Each cryptographer tosses a coin. Each coin is in between two cryptographers. • The result of each coin-tossing is visible to the adjacent cryptographers, and only to them. • Each cryptographer examines the two adjacent coins • If he is paying, he announces “agree” if the results are the same, and “disagree” otherwise. • If he is not paying, he says the opposite • Claim: if the number of “disagree” is even, then the master is paying. Otherwise, one of them is paying. In the latter case, the non paying cryptographers will not be able to deduce whom exactly is paying Lecture 4
The dining cryptographers: Solution Crypt(0) notpays.0 pays.0 Coin(0) Coin(1) look.2.0 Master out.1 Crypt(1) Crypt(2) Coin(2) Lecture 4
3: Randomized Resource allocation • Example:The Generalized dining philosophers • The problem:coordinate the activity of several processes (philosophers), who share common resources (forks), and need more than one resource to perform a certain activity (eat). We want to avoid deadlock and starvation • Generalizedmeans that a philosopher can need more than two forks and that a fork can be shared by more than two philosophers Lecture 4
Dining Philosophers: classic case Each fork is shared by exactly two philosophers Lecture 4
Dining Philosophers: deadlock Each philosopher is holding one fork Lecture 4
Dining Philosophers: generalized case Each fork can be shared by more than two philosophers Lecture 4