Cyber Crimes
240 likes | 1.33k Views
Cyber Crimes. Chunlian QU. What’s Cyber Crimes?. Cyber crime, also called computer crime, is any illegal behavior directed by means of electronic operations that targets the security of computer systems and the data processed . Types of Attacks. Military and Intelligence Attacks

Cyber Crimes
E N D
Presentation Transcript
Cyber Crimes Chunlian QU
What’s Cyber Crimes? • Cyber crime, also called computer crime, is any illegal behavior directed by means of electronic operations that targets the security of computer systems and the data processed .
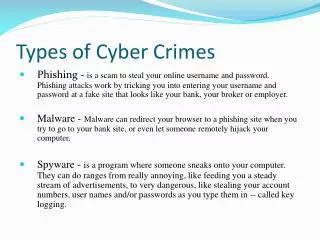
Types of Attacks • Military and Intelligence Attacks • Business Attacks • Financial Attacks • Terrorist Attacks • Grudge Attacks • “Fun” Attacks
Types of Offenders • Cracker: motivation is to access a system or data • Criminals: motivation is financial gain. • Vandals: motivation is to damage the system or data files.
Types of Security • Physical security • Personnel security • Communications security • Operations security
Types of Cyber Crimes- Breaches of physical security • Dumpster diving (trashing) • Wiretapping • Eavesdropping on Emanations • Denial or Degradation of Service • Prevention method: - Locks and keys. - Natural disasters - Environmental threats
Types of Cyber Crimes- Breaches of Personnel security • Masquerading • Social engineering • Harassment • Software piracy • Prevention method: - Background checks and careful monitoring on the job
Types of Cyber Crimes- Breaches of communications and data security (Data attacks) • Unauthorized Copying of Data • Traffic analysis • Covert channels
Types of Cyber Crimes- Breaches of communications and data security (Software attacks) • Trap doors (back doors) • Session hijacking • Tunneling • Timing Attacks • Trojan horses • Viruses and Worms
Types of Cyber Crimes- Breaches of communications and data security (Software attacks) • Salamis • Logic bombs • Prevention methods: - Access control - Cryptographic methods - Physical protection and shielding of network cabling - Firewall technology
Types of Cyber Crimes- Breaches of operations security • Data diddling (false data entry) • IP spoofing • Password Sniffing • Scanning • Excess Privileges • Prevention: The only way it can be effective is if it is integrated into an organization’s physical, personnel, and communications security programs.
Steps taken after the breach • The first step is to assess the situation. - What is the severity level of the intrusion? - Who will be involved in the investigation? - Who is responsible for determining future actions?
Steps taken after the breach • The second step is to repair damage and prevent recurrence. • Under a serious breach, asking - Government agencies. - Private companies.
Report Cyber Crimes • Cyber crimes the NCCS (The FBI’s National Computer Crimes Squad) investigates include: - Intrusions of the Public Switched Network (the telephone company). - Major computer network intrusions. - Network integrity violations. - Privacy violations - Industrial espionage. - Pirated computer software. - Other crimes where the computer is a major factor in committing the criminal offense.
Methods of investigations • The important first step is determining if a criminal still has control of any relevant computer. • As a general rule, an investigator should not let the attacker know that they are being disconnected or tracked due to unauthorized access.
Suggestions because of laws • Firms should secure their networked information. • Government should assure that their laws apply to cyber crimes. • Firms, governments, and civil society should work cooperatively to strengthen legal frameworks for cyber security.