Compliant Cryptologic Protocols
510 likes | 647 Views
This talk presented by Ed Dawson, Kapali Viswanathan, and Colin Boyd discusses the essential aspects of compliance in cryptographic systems. It covers the meaning of compliance, introduces key recovery systems (KRS), and explores applications like anonymous token systems and e-cash. The discussion delves into operational guarantees required by different user sets and the importance of trust among users. Through visualizations and models, the talk elucidates how compliance can be verified in various cryptographic applications, emphasizing confidentiality and integrity.

Compliant Cryptologic Protocols
E N D
Presentation Transcript
Compliant Cryptologic Protocols Ed Dawson, Kapali Viswanathan, Colin Boyd Information Security Institute Queensland University of Technology Brisbane, Australia.
Sections of this Talk • Introduction to compliance in cryptosystems • Generic goals • Players in the game • Applications • A view of cryptosystem • Visualisation of basic services • A model for representing cryptosystems
Sections of this Talk • Key-recovery systems (KRS) • Long-term key-recovery • Short-term key-recovery • Hybrid key-recovery • Anonymous token systems (ATS) • A description (definition) • An application (Sealed-bid e-auction) • Summary and Conclusion
Section 1 Introduction to Compliance in Cryptosystems
Introduction to Compliance Meaning: Compliance • the act or process of complying to a desire, demand, or proposal or to coercion • a disposition to yield to others • conformity in fulfilling official requirements What conformities (acts or events) can be cryptologically verified?
Investigating Compliances • What can cryptologic compliance mean? • There are at least two mutually mistrusting sets of users • The users in a set require operational guarantees for the users in the other set
Example: Key Recovery Systems • Three mistrusting sets of users • Communicating entities • require confidential communication with authentic entities • Wiretap authority • Requires to know what others communicate • The cryptanalyst • wants to know everything (P = NP?) Cryptanalyst Receiver Sender Wiretap Authority Mistrusting sets
Compliance: Key Recovery Systems • Communicating entitiesare confident that the cryptanalyst is unable to read the confidential messages (Cryptologic exercise) • The wiretap authorityis confident that it can read the confidential messages (a cryptologic exercise, if not for super-encryption and similar techniques) • Communicating entitiesare confident that the wiretap authorities will not read all the confidential messages without proper approval (Trust based: How trustworthy is the wiretap authority? – Not entirely a cryptologic exercise)
Bank Withdrawal Trustee Merchant User Spending Conditionally untraceable Example: E-Cash Systems • Four mistrusting sets of users • The bank: • only it can mint valid cash • valid cash can be spent only once • The user: • valid cash cannot be invalidated • will be anonymous while spending the cash • The merchant: • valid cash cannot be invalidated • will accept only valid cash • The trustee: • can trace transactions (thereby, identify the user)
Facts: E-Cash Systems • There is reduced or no anonymity for the user, if: • there is only one user (NUMBERS); or, • the user always withdraws from the same ATM and spends with the same merchant (SPACE); or, • the user always spends just after withdrawing the cash (TIME); or, • the user provides identification information to the merchant (DATA); • the machine that the user uses can be easily traced (DATA).
Compliance: E-Cash Systems • Only the bank can mint valid cash (cryptologic exercise) • Valid cash will be spent only once by the authorised user (must assume that the user does not reveal some long-term secret-key)
Compliance: E-Cash Systems • Withdrawal and spending transactions cannot be traced without the assistance of the trustee (cryptology prevents only data-level correlations --- number of regular users is important --- and does not prevent correlations in space/time/numbers) • The trustee will trace only as prescribed by some set of rules (behaviour of entities is not – and cannot be – a cryptologic concern)
Compliance: E-Cash Systems • The merchant and the bank will accept valid coins (the behaviour of any entity is not a cryptologic concern)
Some More Examples Other examples include: • Electronic auctions • Mistrusting sets: Auctioneer, bidder, sets of bidders, optional trustee • Electronic voting • Mistrusting sets: Voter, sets of voters, voter authenticator, vote authenticator, vote collector, vote teller, system observers Entity which counts votes
Section 2 Investigation and classification of basic services and compliance verification in cryptosystems
Basic Cryptologic Services • Is it possible to decide what is a cryptologic exercise and what is not? Yes • How? By enumerating what cryptology can do • What are the basic services? They areconfidentiality and integrity • Are they independent of each other? NO. But it may not be a flaw to treat separately
What is Compliance in Cryptosystems? • There is a need for some entities to verify the cryptologic behaviour of some other entities • What is a cryptologic behaviour ? Entities use keys to transferservices to certain messages • How can such transfer of service be verified? • If such a transfer of service can be verified, then such a verification is called compliance verification
Classifying Compliance • It is possible to classify various types of compliance verification by enumerating the modes of transfer of services • There are two modes of transfer of services • Restricted : the service is guaranteed until the occurrence of a probabilistic or deterministic event • Universal: the service is guaranteed forever (forever is the idealisation for the span of time that is determined by the security properties of the cryptographic algorithms and the key management systems)
A Classification of Compliance 2 (basic services) 2 (modes of service) = 4 ( categories of compliance verification) • CL0:Universal confidentiality and integrity (signature systems) • CL1: Universal integrityand restricted confidentiality (KRS, fair cash)
A Classification of Compliance • CL2:Restricted integrity and universal confidentiality (deniable encryption) • CL3:Restricted integrity and confidentiality (Oblivious Transfer?)
How to Enforce Compliance? • If an integrity transfer must be verified, how can such a verification be made mandatory? • EL0: On-line monitor (Clipper, Wallet with observers) • EL1: Off-line monitor (Binding ElGamal, E-cash [Chaum, Brands])
Section 3 Key Recovery Systems(Compliance and Confidential Communications)
Introduction to KRS • Confidential decryption keys must be available for the receiver and the escrow authority • Restricted Confidentiality: Confidential messages sent to the receiver is guaranteed against every adversary except the escrow agent • Universal Integrity: The proof that the secret message (keying information and others) sent to the receiver is the same as that sent to the escrow authority (Proof that a certain key is being used)
Types of KRS • Long-term key-recovery • Long-term confidentiality keys are accessible for the escrow agent • Private-key recovery • Short-term key-recovery • Short-term confidentiality keys are accessible for the escrow agent • Session-key recovery
Types of KRS • Hybrid key-recovery • Long-term confidentiality key is shared by the escrow agent and the receiver • Short-term confidentiality key is accessible for the escrow agent and the receiver • Example: hybrid key-recovery system
Private-key Recovery Systems • Let public-key, y = OWF (x) • Escrow component, EC = Escrow (x) • Know (x) Know (EC) The identity of the escrow authority and the identity of the user (owner of the public key [y]) are indistinguishable. The escrow authority can do everything that the user can do
Properties of Private-Key Recovery • Merits • Efficiency • Backward compatibility • Demerits • Risk to private keys (Security of escrow database) • Enforceability (users can change to a certified proxy-key) • Authentication and escrow functionalities are not separate (co-existence of escrowed PKI and signature?) • Granularity (Past-present-future problem) • Super-encryption
Session-key Recovery Systems • Let S be the session-key chosen by the sender • Escrow component, EC = Escrow (S) • Know (S) Know (EC) Knowing the session-key is equivalent to knowing the escrow component.
Properties of Session-Key Recovery • Merits • Granularity • Authentication and escrow functionalities are separate • Demerits • Enforceability (requires trusted device to make sure that keys are properly escrowed) • Session-keys are random and uncertified (creates communication and storage overhead) • Super-encryption
Hybrid Key-Recovery Systems • Kapali Viswanathan, Colin Boyd, Ed Dawson, Strong Binding for Software Key Escrow. In International Workshop on Security, IWSEC'99. IEEE Press, 1999. • Kapali Viswanathan, Colin Boyd, Ed Dawson, Hybrid Key Escrow. In Computers & Security, ISSN 0167-4048, Vol. 21, No. 1, 77-92. Elsevier Advanced Technology, 2002.
Valid Message Flow Valid Message Flow Invalid Message Flow (To be prevented) Message Dynamics: Hybrid Key-Recovery Systems Sender Receiver (Ideally, must not be able to recover the message from the invalid flow) Authority (Must have a secret that is essential for the valid communication to occur)
Message Dynamics With LEA Authority (Cryptologically prevents receipt of invalid communications) Receiver (Can receive valid and secure communications) Sender (Must enable key-recovery) LEA (Special User)
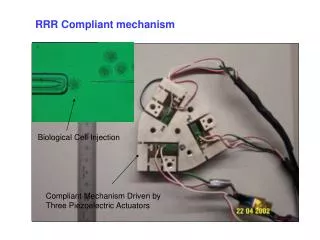
Hybrid Key-Recovery Systems • Public-key, y = OWF (x) • Private-key, x, is a universal secret • x = x1 * x2 • User’s share is x1 • Escrow component EC = Escrow (x2) • Similarly, LEA’s public key is y’ = OWF(x1’ * x2’) • LEA is a special user
Hybrid Key-Recovery Systems • Due to the public-key format and the protocol (Binding ElGamal) • The session key, S, can be accessed if • Know (x1) AND Know (x2); OR, • Know (x1’) AND Know(x2’) The user (x1) or the LEA (x1’) cannot access the session key (S) if the escrow authority (x2, x2’) does not assist them
Properties of Hybrid Key- Recovery • Merits • Solves several issues present in the previous types • When source traceability is achieved using appropriate signature techniques, it achieves all the properties of Clipper in a more secure fashion • Granularity • Session is random but integrity is assured • Enforceability level EL0 ( on-line monitor ) • Demerits • On-line authority ( efficiency and scalability points of views ) • Super-encryption
Section 4 Anonymous Token Systems(Compliance and Confidential Identity)
What is cryptologic anonymity? • Let a data, D, belong to a user, I • Suppose that the correlation between the data and the identity is to remain confidential • Confidentiality (Integrity ( I, D ) ) Cryptologic Anonymity: The correlation, (I, D), must remain a secret (confidentiality service ) and optionally it cannot be changed (integrity service)
Techniques for achieving cryptologic anonymity • ( I , Confidential ( D ) ) [This entity has something] • (Confidential ( I ) , D ) [Some entity has this thing] • ( Confidential ( I ) , Confidential ( D ) ) [Some entity has something] Integrity service can be independently provided to all of the above constructs
TIA SubmitToken IssueToken Trustee TAA Client UtiliseToken Conditionally untraceable (OPTIONAL) Anonymous Token Systems (ATS) • E-cash systems are essentially a PKI mechanism which provides certificates (tokens) with confidential identity • Token Issuing Authority (Bank) • Token Accepting Authority (Merchant)
Compliance Issues in ATS • Only authenticated participants can participate • Participants must remain anonymous (confidential identity) • Optional revocation of anonymity (conditional confidentiality service for the identity)
Applications that can use ATS • Electronic cash (I, D = Denomination) • Peer Review Protocol (I , D = PeerID) • Auction Protocol (I, D = Bid) • Electronic Voting Protocol (I, D = Vote)
Entities in Sealed-Bid Electronic-Auction Systems • Auctioneers • Valid participants • Non-repudiation of bid • Termination of bidding process • Bidders • Fairness of bidding process • Confidentiality of bid until the bid opening phase • Optional Trustee • If the bid is not opened after the bid opening phase, the bid must be recovered
Properties of Sealed-Bid Auction Systems • Confidentiality of Bid • Non-repudiation of Bid • Publicly verifiability [OPTIONAL] • Anonymity for losing bidders (or bids) [OPTIONAL] • Independence of auction rules [OPTIONAL]
A Sealed-Bid Auction System using ATS • Kapali Viswanathan, Colin Boyd, Ed Dawson, A Three Phased Schema for Sealed Bid Auction System Design. In Australasian Conference for Information Security and Privacy, ACISP'2000, 412-426. Lecture Notes in Computer Science, Springer-Verlag, 2000.
System Description • Every bidder, bi, is issued with a pseudonym, pi, using an ATS • The bidder authenticates using pi to gain access to an anonymous channel • The bidder anonymously commits (sealed-bid) to the bid value [ pi, commit ( bidi ) ] pi = Universal-Integrity ( Restricted-Confidentiality ( bi ) ) commit( bidi ) = Universal-Integrity-Confidentiality ( bidi )
System Description • After announcement of the closing of the auction bid-commitment closing period, the bidders • Authenticate using pseudonym, pi • Open the bid [pi, bidi] • After the announcement of the closing of the auction bid-commitment opening period, the winning bid is selected from the list of opened bids [ SET-OF ( bidi ) ] • Enforceability level: EL1 (off-line monitor)
Properties of the Proposed System • Merits • Independent of auction rules • User-controlled confidentiality for the bid • Modular design (ATS + Basic auction) • Public verification possible • Demerits • Requires anonymous communication channel • Does not solve the problems related to the timing of various phases (E.g. closing time of the bid registration phase)
Summary & Research Directions
Summary • Compliance is essential for secure e-commerce • Enforceability level determines the effectiveness with which the compliance verification rules can be enforced • Systems with on-line monitors ( hybrid key-recovery, Clipper ) have inherently more enforceability than do systems with off-line monitors ( Binding ElGamal, E-Cash without monitors )
Research Directions • What are the relations among various applications of protocols (auction, voting etc)? • How to achieve robust e-auction and e-voting systems? • Design a formal and simple syntax for the representation of confidentiality and integrity services