Agenda
Seminar on Cloud Computing: Buzzword or Savior ??? Cloud Computing Challenges & Security Issues. Agenda. Cloud Computing Challenges Cloud Security Issues Cloud Security Incidents Statistical analysis of Cloud Sec breaches Cloud Security Controls. Cloud Computing Challenges.

Agenda
E N D
Presentation Transcript
Seminar on Cloud Computing: Buzzword or Savior???Cloud Computing Challenges & Security Issues
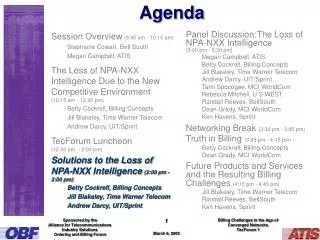
Agenda Cloud Computing Challenges Cloud Security Issues Cloud Security Incidents Statistical analysis of Cloud Sec breaches Cloud Security Controls
Cloud Computing Challenges • Despite many opportunities there has been backlash against Cloud computing: • Dependence on others and that could possibly limit flexibility and innovation: • Monopoly of Bigger Internet companies (google & IBM). • Return to the time of mainframe computing ?? • Security could prove to be a big issue: • Safety of out-sourced data • Uncertainty in the ownership of data.
Cloud Computing Challenges… • There are also issues relating to policy and access: • If your data is stored abroad whose policy do you adhere to? • What happens if the remote server goes down? • How will you then access files? • There have been cases of users being locked out of accounts and losing access to data.
Cloud Computing Challenges Security Privacy Interoperability Portability Service Delivery & Billing Abuse of Cloud Services Performance Usage Control CLOUD Reliability Bandwidth Cost Availability Lack of knowledge & Expertise Shared Technology Issues Insufficient due diligence
Toshiba -- July 12, 2011 Toshiba Database hacked and User accounts leaked by V0iD
Amazon – July 29, 2011 Amazon Cloud hosts nasty Banking Trojan
Microsoft – September 21, 2011 Microsoft Cloud evaporated by 1 busted file Service failed for hours
APPLE – December 22 ,2011 New Phishing attacks target iCloud, MobileMe users
Cloud Security Challenges Data Locality Privacy Trust Identity Management Virtualization Network Security Data Confidentiality Access Control Data Integrity Data Security Audit & Compliance
Incidents with un-reported causes Cloud breakdown due to unreported causes Number of Incidents
Cloud Security Threats • Abuse and Nefarious Use of Cloud Computing • Anyone with a valid credit card can register and abuse the relative anonymity to conduct their malicious activities with relative impunity. • Insecure Interfaces and APIs • The security and availability of general cloud services is dependent upon the security of SW interfaces and APIs. • Malicious Insiders • This threat is amplified for consumers of cloud services that are under a single management domain, combined with a lack of transparency. • Cloud related Malware • Attackers can use cloud-specific malware, such as bugs and Trojans, to either infiltrate or corrupt the network.
Cloud Security Threats-Cont.. • Account or Service Hijacking • Attack methods such as phishing, fraud, and exploitation of software vulnerabilities still achieve results. • Data Loss or Leakage • Due to the increase in number of interactions between risks and challenges which are unique to cloud because of the architectural or operational characteristics of the cloud environment. • Hardware Failure • Hardware, from switches to servers in data centers, may fail making cloud data inaccessible.
Cloud Security Threats – Cont.. • Inadequate Infrastructure Design and Planning • Providers cannot cater to sudden spikes in demand, • Insufficient provisioning of computing resources • Poor network design • Closure of Cloud service • Disputes with the cloud provider or non-profitability of the cloud service leading to data loss unless end-users are legally protected. • Natural Disaster • Based on the geographical location and the climate, data centers may be exposed to natural disasters which can affect the cloud services
Cloud Security Controls • Data Governance • Labeling & Handling • Retention Policy • Security Policy • Risk Assessment • Secure Disposal • Information Leakage • Compliance • Third Party Audits
Cloud Security Controls • Information Security • Baseline Requirements • User Access Policy • User Access Reviews • Segregation of Duties • Encryption & Encryption key management • Vulnerability / Patch Management • Policy Enforcement • User Access Restriction / Authorization • User Access Revocation • Incident Management
Cloud Security Controls • Security Architecture • User ID Credentials • Network Security • Data Security / Integrity • Audit Logging / Intrusion Detection • Application security • Remote user multi-factor authentication • Data Governance • Ownership / Stewardship • Handling / Labeling / Security Policy • Information Leakage