Agenda
Agenda. Quick introduction Three sins Password compromise Weak passwords Password verifiers Questions?. Everybody hates passwords. Users. ERROR: Password must be at least 10 characters and contain uppercase, lowercase, numbers and special characters (!”#€%&[]) . Everybody hates passwords.

Agenda
E N D
Presentation Transcript
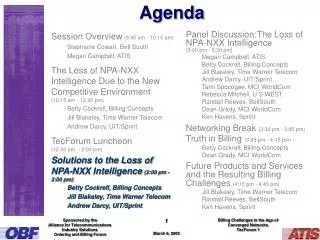
Agenda • Quick introduction • Three sins • Password compromise • Weak passwords • Password verifiers • Questions?
Everybody hates passwords Users ERROR: Password must be at least 10 characters and contain uppercase, lowercase, numbers and special characters (!”#€%&[])
Everybody hates passwords Security experts
Password compromise • Passwords • Authentification method Confidentiality • Portable Can shift hands • The single most important flaw of passwords
Tricked! Phishing Social engineering
How to protect yourself against passwords compromise • Watch out for phishing/social engineering • Educate your users to check the URL! • Educate your users to never reveal their credentials • Watch out for sniffing • Use SSL communication • Educate your users to say no to chocolate • Don’t rely on passwords for critical systems • Use several layers of authentication
Don’t use weak passwords! SSH server 768 bit Size: 8 alphanumeric Network traffic RSA Password ITU Factorising 768 bit key: operations = 2000 years for one computer Source: Bruce Schneier 2010 Password = superman
What is a weak password • Work RelatedNames • Pop Culture • Artist/Band • Movies • Brands • Dictionary Words • Personal Information • Family • Pet • Interests and hobbies
Other types of weak passwords • Password iteration • Summer2012 • fall2012 • Not requiring password changes • Default password • Routers • Servers • Embedded software
Bigger is Better? Password: A7hGvH76#!0$JK_hgAf56Rg+9(/rF2387Hg>N combinations VIOLATES!!! • PsychologicalAcceptability • Users willmake it easy for • themselves and find a ”loop-hole”
Don’t store cleartext passwords! • Oops, the bad guy got access to my database • SQL Injection could make passwords public • Disgruntled employees could steal all passwords • Passwords are often reused across systems • Password often carry sensitive information • Password = SistersNameAndBirthdate • Or actual secrets...
Don’t store cleartext passwords! Password = iCheated69Times Password = IShotJFK!
Instead store password verifiers! • Use a key derivation function • Ex. a cryptographic hash • Problems?
Example: Salted hash • Creation of a password DB Plaintext Password Random Salt Hashing (Plaintext Password + Salt) DB Password Hash
Example: Salted hash • Verification of a password DB Plaintext Password Stored Salt Hashing (Plaintext Password + Salt) Password Hash = ? DB Stored Hash