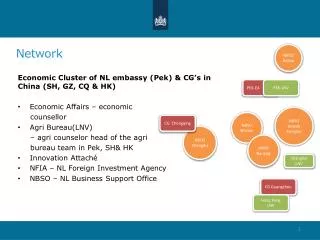
Network
Network. Minggu ke – 9 Magister Teknik Elektro Universitas Udayana. What is a Network? Allows Computers to Communicate Share Files, Printers and Other Peripherals Connect to a Centralized Server. Network Communications and Protocols

Network
E N D
Presentation Transcript
Network Minggu ke – 9 Magister Teknik Elektro Universitas Udayana
What is a Network? • Allows Computers to Communicate • Share Files, Printers and Other Peripherals • Connect to a Centralized Server
Network Communications and Protocols • Protocol - The definition of a language that allows computers and networks to communicate • OSI Model • Breaks network protocols down into seven different layers. • Computer Protocols • Languages Computers use to communicate across networks • Network Protocols • Languages Networks use to communicate
Network Communications and ProtocolsComputer Protocols • NetBEUI (NetBIOS Extended User Interface) • Microsoft Windows • File and Printer Sharing • Easiest to Setup • Works Best on Small Networks • Less Than 25 Computers • Large Networks Require WINS Server • Alternative is NetBIOS over TCP/IP • IPX/SPX and NWLink (NetWare) • Allows Windows computers to communicate with Novell based networks • Available as of Windows 95 and NT 4.0
TCP/IP • Most widely used protocol today • Protocol used across the Internet hence IP • Packet based • IP Based Networks • IP Addresses • Subnet Masks • Gateway • DHCP (Dynamic Host Configuration Protocol )Server • DNS Server
Public IP Addresses • Given out in “Blocks” • Computers with Public IP addresses can be directly accessed from the Internet • Poses Potential Security Risk
Private IP Addresses • Can not directly connect to the Internet • Translated to public IP address prior to sending data on the Internet • Free for anyone to use
TCP/IP : IP Addresses • Dynamic vs. Static • Subnet Mask • Gateway • DNS Server
SubnettingA Network with two levels of hierarchy (not subnetted)
Cross Platform Communications • Linux / Unix / Mac OS X • Samba – Allows these operating systems to use the NetBIOS Protocol to communicate with Windows operating systems • Windows • Services for Unix (SFU) – Allows Windows operating systems to use the NFS protocol to communicate with Linux / Unix operating systems
OSI Model • Breaks network protocols down into seven different layers. • Protocol functions • Segmentation and reassembly • Encapsulation Addressing • Connection control Multiplexing • Ordered delivery Transmission services • Flow control • Error control • synchronization • Computer Protocols • Languages Computers use to communicate across networks • Network Protocols • Languages Networks use to communicate
Users-oriented Users of transport service End-to-end connection oriented Network service Point-to-point link oriented Perspective on the OSI architecture
Network Protocol • Token Ring • Backbone for large ring topologies • Uses special packet called a Token • Computer holding token allowed to communicate on network • Ethernet • • Designed for LAN technologies • Bus topology; Fast Ethernet: 100 Mbps; Gigabits Ethernet: 1000 Mbps • • Listens to network before transmission • • Uses random wait times to resolve collisions • • Not limited to Ring Topology
Ethernet implementations 10Base5: Thick Ethernet or Thicknet
10Base2: Thin Ethernet or Cheapernet It uses bus topology with an internal transceiver or p2p connection via an external transceiver. If the station uses an internal transceiver, there is no need for an AUI cable If the station lacks a transceiver, then an external transceiver can be used in conjunction with the AUI
Segments Max. 5 segments, each segment max 185 m. Only 3 segments for connecting stations to medium; 2 segments for remote repeaters The max.no. stations 96, 32 stations/segment
10Base-T: Twisted-Pair Ethernet Physically is star topology, logically is bus topology The stations are connected to a hub with either an internal or external transceiver Internal transceiver: no need AUI cable External transceiver: AUI cable for connecting the transceiver – interface Medium & connectors: twisted-pair cable and RJ-45 connectors
10Base-FL: Fiber Link Ethernet Star topology, External transceiver: fiber-optic MAU AUI Cable: to connect the station – external transceiver Spec. 10Base-FL: Duplexity: Full-duplex Physical topology: star Medium: Fiber 62.5/125 m Max. length: 2000 m Medium and connectors
VLAN (Virtual Local Area Network) A subnetwork or a segment of a local area network configured by software, not by physical wiring
VPN (Virtual Private Network) A network that is private, but virtual It is private because it guarantees privacy inside the organization. It is virtual because it does not use real private WANs; the network is physically public, but virtually private
Gigabit Ethernet Architecture Standard Media Access Control (MAC) full duplex and/or half duplex Gigabit Media Independent Interface (GMII) (optional) 1000 Base – X PHY 8B/10B auto-negotiation Unshielded twisted pair IEEE 802.3ab 1000 Base T PCS 1000 Base T PMA transceiver 1000 Base-LX Fiber optic transceiver 1000 Base-SX Fiber optic transceiver 1000 Base-CX Copper transceiver Single Mode or Multimode Fiber Shieled Copper Cable Multimode Fiber IEEE 802.3z Source - IEEE
Gigabit Ethernet Technology Figure 4-23.Gigabit Ethernet cabling. • 1000 BASE SX fiber - short wavelength • 1000 BASE LX fiber - long wavelength • 1000 BASE CX copper - shielded twisted pair • 1000 BASE T copper - unshielded twisted pair • Based on Fiber Channel physical signaling technology.
Network Hardware • NIC – Network Interface Card • Cabling • Cat 5 • Cat 5e • Cat 6 • Fiber Optic • Hub or Repeater • Repeats information out to all ports • Creates unnecessary network traffic • Least sophisticated of all network equipment • Switch • Analyzes packets and routes directly to destination port • More efficient than hub
Network Hardware • Router • More sophisticated than Switch • Knows what type of traffic • Can be used as first line of defense when securing a network • Firewall • Not only knows type of traffic, but analyzes traffic for potential vulnerabilities. • Rule based analysis