Section 2.9 The Hill Cipher; Matrices
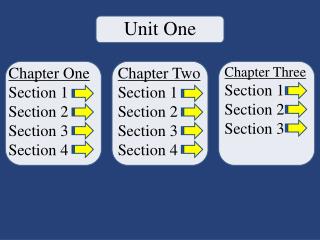
Section 2.9 The Hill Cipher; Matrices. The Hill cipher is a block or polygraphic cipher, where groups of plaintext are enciphered as units. The Hill cipher enciphers data using matrix multiplication. We will now introduce the concept of a matrix…. Introduction to Matrices.

Section 2.9 The Hill Cipher; Matrices
E N D
Presentation Transcript
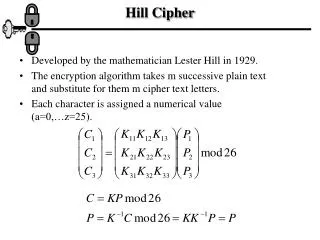
Section 2.9 The Hill Cipher; Matrices • The Hill cipher is a block or polygraphic cipher, where groups of plaintext are enciphered as units. • The Hill cipher enciphers data using matrix multiplication. • We will now introduce the concept of a matrix…
Introduction to Matrices • A matrix is a rectangular array of numbers made up of rows and columns. • The size of a matrix is given as m x n • m is the number of rows to the matrix. • n is the number of columns to the matrix. • To indicate an individual entry in a matrix A, we use aij where i = row and j = column. • The general form of a mxn matrix has the form indicated here. • A square m x n matrix is a matrix where m = n. That is the number of rows equals the number of columns…
Introduction to Matrices • Equality of Matrices • Two matrices A and B are equal if • They have the same size and • There corresponding entries are equal. • Special types of Matrices – Vectors • A row vector is a matrix with one row. • A column vector is a matrix with one column…
Introduction to Matrices • Matrix Addition and Subtraction • Two matrices can be added and subtracted only if they have the same size. • Example 1: A + B and A – B • Example 2: A + B and A – B • Scalar Multiplication of Matrices • When working with matrices, numbers are referred as scalars. To multiply a matrix by a scalar, we multiply each entry of the matrix by the given scalar. • Example 3: 3A • Example 4: 5A – 2B • Addition and Scalar Multiplication Properties of Matrices…
Introduction To Matrices • Matrix Multiplication • Multiplying two matrices requires how you multiply a row vector times a column vector. • Example 5: Compute AB • For the matrix product AB to exist, the number of columns of A must be equal to the number of rows of B. • If A has size m x n and B has size n x p, then the product AB has size m x p. • The number of row and column vectors that must be multiplied together is mp. • The ijth element of AB is the vector product of the ith row of A and the jth column of B. • Example 6: • Example 7: • Example 8: • In general, matrix multiplication is not commutative: AB ≠BA…
Introduction to Matrices • Multiplicative Properties of Matrices • Let A, B, and C be matrices whose sizes are multiplicatively compatible, c a scalar. • (AB)C = A(BC) matrix multiplication is associative • A(B + C) = AB + AC • (A + B)C = AC + BC • c(AB) = (cA)B = A(cB)…
Introduction to Matrices • Addition Identity Matrices • The additive identity has all entries of zero. It is called the zero matrix. • If A is mxn then the zero matix is mxn. • The zero matrix is called 0. • A + 0 = 0 + A = A • Multiplicative Identity Matrices • If A is mxn then the multiplicative matrix is nxn. • The multiplicative identity has 1s on the main diagonal (row number = column number) and 0s everywhere else. • Example 9: AI and IA…
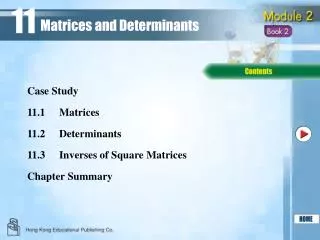
Introduction to Matrices • Determinants • The determinant of a matrix is a real number. • The determinant of a 2x2 matrix. • Example 10: Find the determinant • Example 11: Find the determinant • Note: the determinant of a 1x1 matrix is just the value of the entry. A =[3] then |A| = 3. • You can calculate the determinant of any nxnmatrix…
Introduction to Matrices • Matrix Inverses • The additive inverse of a matrix is obvious. You want A + B = 0, where B is the inverse. That is B = -A. • The more difficult to find, and not always exists, is the multiplicative inverse. • The matrix A must be nxn (a square matrix) • Notation of the inverse. • The inverse for the 2x2 matrix is fairly simple to find. • The B is the inverse of A the AB = BA = I. (I call it B here because this stupid program doesn’t allow exponents) • Example 12: Find inverse. • Note: For the matrix A, the inverse exists if det(A) ≠ 0. • Example 13: Find Inverse. • Example 14: Find Inverse…
Introduction to Matrices • Matrices with Modular Arithmetic • For a matrix A with entries aij we way that A MOD m is the matrix where the MOD operation is applied to each entry: aij MOD m. • Example 15: Compute matrix MOD 26. • Example 16: Find A + B and A – B MOD 5 • Example 17: 3A MOD 13 • Example 18: Product AB MOD 26…
Introduction to Matrices • Finding the inverse of a matrix in modular arithmetic. • Example 19: Find the inverse of a matrix • Example 20: Determine if inverse exists. • Example 21: Solve the system of equations…
The Hill System • The Hill Cipher was developed by Lester Hill of Hunter College. It requires the use of a matrix mod 26 that has an inverse. • The procedure requires breaking the code up into small segments. If the matrix is nxn, then each segment consists of n letters. • If A is the matrix and x is the n letter segment code, then the ciphertext is found by calculating Ax = y. Y is the ciphertext segment. • To decipher the text we use the inverse of the matrix A. If we call this inverse B, then By deciphers the code returning x. • Note: It is required that the plaintext message have n letters. If it does not have some multiple of n letters, we pad the message with extra characters until it does. • Example 22: Encrypt a Message. • Example 23: Decrypt a Message…
Cryptanalysis of the Hill System • Having just the ciphertext when trying to crypto-analyze a Hill cipher is more difficult then a monoalphabetic cipher. • The character frequencies are obscured (because we are encrypting each letter according to a sequence of letters). • When using a 2x2 matrix, we are in effect creating a 26^2 = 676 character alphabet. That is, there are 676 different two letter combinations. • If you in fact knew that the ciphertext was created using a 2x2 matrix, then a crypto-analyst could break the code with brute force, since there are 26^4 (each entry in the matrix can have 26 different numbers) = 456976 different matrices. • The way to make it more difficult is to increase the size of the key matrix…
Cryptanalysis of the Hill System • If the adversary has the ciphertext and a small amount of corresponding plaintext, then the Hill Cipher is more vulnerable…!