Enhancing Digital Communication through Netiquette: A Summer Program Recap
On June 30, 2011, Cathy Kidder led a summer program at Beebe High School Library, emphasizing the importance of netiquette for students entering grades 7-12. A small group of 5 students (4 boys and 1 girl) engaged in discussions about netiquette rules, analyzed real-life internet scenarios, and shared insights about the importance of respectful online communication. The program aimed to foster understanding of digital etiquette while encouraging students to connect and participate actively. Feedback indicated a positive reception, with students appreciating the interactive approach.

Enhancing Digital Communication through Netiquette: A Summer Program Recap
E N D
Presentation Transcript
Netquitte or Not?Program ImplementationJune 30, 2011Cathy KidderLIBM 6371Summer 19 – 12 GradeBeebe High School Library
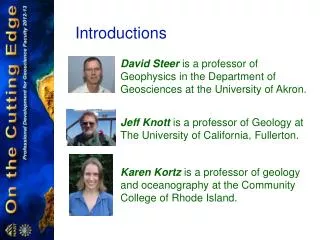
Introductions A total of 5 students attended the program. 4 boys and 1 girl. We spent a few minutes getting to know each other. I also introduced the program at this point.
Netiquette Information Handing out book marks with the netiquette rules so that we can use that for discussion purposes.
Discussion We discussed the netiquette rules and why they are important. I chose to sit with the students rather than stand in front of them because it was a small group and I felt like I would connect with them more if I was “on their level”.
Scenarios Different internet scenarios were given to the students. They analyzed them to see what netiquette rules had been broken. I visited with the students as they were reading to make sure they understood the situation and answer any questions they had.
Scenario 1 • Lester sends e-mail to the entire body inviting them to a BYOB party at his house while his parents are out of town. Lester receives a message from a system administrator calling him in for a meeting with school officials. He objects because he feels that his e-mail is his own private business. http://www.uni.illinois.edu/library/computerlit/scenarios.php
Scenario 2 • Jules has walked away from a lab computer without logging off. Trish sits down and, still logged in as Jules, sends inflammatory e-mail messages out to a number of students and posts similar messages on the class newsgroup http://www.uni.illinois.edu/library/computerlit/scenarios.php
Scenario 3 • Chester, Agatha, and Ridley are hanging out at the park one day and meet up with Chester’s friend Troy. Troy takes a bunch of pictures with his cell phone and uploads them to Facebook, adding suggestive captions to the photos. Agatha starts getting friend requests from guys she doesn’t know. She also gets a phone call from one of the families she babysits for, cancelling her upcoming job with them. http://www.uni.illinois.edu/library/computerlit/scenarios.php
Discussions The three different scenarios prior to this slide were read by the students and discussions were held about the scenario, which rule was broken and why.
Program Evaluation Adapted from Wilson Library Programs that Inspire I enjoyed the speaker’s presentation. Yes No I learned new and useful information about the topic. Yes No I could easily hear the speaker well. Yes No I could easily see the speaker and materials. Yes No I want to find out more information about this topic. Yes No I thought the program was too long. Yes No The best aspect of the program was: My suggestions for future programs:
Evaluation Results The results are an average of all the surveys completed by the students. I enjoyed the speaker’s presentation. Yes No I learned new and useful information about the topic. Yes No I could easily hear the speaker well. Yes No I could easily see the speaker and materials. Yes No I want to find out more information about this topic. Yes No I thought the program was too long. Yes No The best aspect of the program was: Looking at the scenarios and talking about them My suggestions for future programs: none
Thank You • Thank you note was sent to Mrs. Judy Alexander, Librarian at Beebe High School, for allowing me to use her library.
References Teacher Created Resources. Internet Literacy, Grades 6 – 8. 2010. Westminster, CA. http://www.uni.illinois.edu/library/computerlit/scenarios.php Accessed 6-30-11 Program Evaluation. Wilson Library Programs That Inspire. Found on Wiki for Designing Informational Programs blackboard.