Achieving Qualities
Achieving Qualities. Võ Đình Hiếu. Contents. Architecture tactics Availability tactics Security tactics Modifiability tactics. Architectural Tactics . A system design is a collection of decisions Some ensure achievement of the system functionality

Achieving Qualities
E N D
Presentation Transcript
Achieving Qualities VõĐìnhHiếu
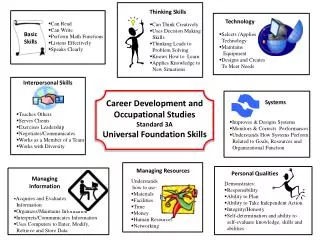
Contents • Architecture tactics • Availability tactics • Security tactics • Modifiability tactics
Architectural Tactics • A system design is a collection of decisions • Some ensure achievement of the system functionality • Others help control the quality attribute responses • A tactic is a design decision that influences the control of a quality attribute response. • A collection of tactics is called an architectural strategy.
Architectural Tactics Tactics to Control Response Stimulus Response
Goal of Availability Tactics Tactics to Control Availability Fault Fault Masked or Repair Made
Availability Tactics • Fault detection • Fault recovery • Fault prevention
Fault Detection Tactics • Ping/echo – one component issues a ping and expects to receive back an echo within a predefined time. • Heartbeat – one component emits a heartbeat periodically and another component listens for it. • Exceptions – one method for recognizing faults is to encounter an exception raised when a fault is discovered.
Fault Recovery Tactics • Voting – Processes running on redundant processors each take equivalent input and compute an output value that is sent to a voter that makes a decision on what to do. • Active redundancy (hot restart) – All redundant components respond to events in parallel and the response from only one component is used (usually the first to respond).
Fault Recovery Tactics • Passive redundancy (warm restart/dual redundancy/triple redundancy) – One component (the primary) responds to events and informs the other components (the standbys) of state updates they must make. When a fault occurs the system must first make sure that the backup state is sufficiently fresh before resuming services. • Spare – A standby spare computing platform is configured to replace many different failed components. It must be rebooted to the proper software configuration and have its state initialized when a failure occurs.
Fault Prevention Tactics • Removal from service – The removal of a component from service to undergo activities to prevent failures. • Transactions – The bundling of several sequential steps in which the entire bundle can be undone at once. • Process monitor – Monitoring for a fault in a process and deleting the nonperforming process and creating a new instance of it.
Summary of Availability Tactics Availability Fault Detection Recovery- Preparation and Repair Recovery- Reintroduction Prevention Fault Removal from Service Trans- actions Process Monitor Fault Masked Or Repair Made Ping/Echo Heartbeat Exception Voting Active Redundancy Passive Redundancy Spare Shadow State Resyn- chroniztion Rollback
Security Tactics • Three categories of security tactics • Resisting attacks • Detecting attacks • Recovering from attacks
Goal of Security Tactics Tactics to Control Security Attack System Detects, Resists, or Recovers from Attacks
Resisting Attacks • Authenticate users – ensuring that a user or remote computer is actually who it purports to be (e.g., via passwords). • Authorize users – ensuring that an authenticated user has the rights to access and modify either data or services (e.g., via access control by user or user class within the system). • Maintain data confidentiality – data should be protected from unauthorized access (e.g., via encryption of persistent data or use of VPN or SSL for a Web-based link).
Resisting Attacks • Maintain integrity – data should be delivered as intended (e.g., via use of redundant encoded information like checksums or hash results). • Limit exposure – allocate services to hosts so that limited services are available on each host. • Limit access – restrict access based on message source or destination port if possible (e.g., via firewalls)
Detecting Attacks • The detection of an attack is usually done through an intrusion detection system. • These systems compare network traffic patterns to a database of patterns.
Recovering from Attacks • Tactics concerned with restoring state: these overlap with availability tactics • Concerned with attacker identification (for either preventive or punitive purposes)
Summary of Security Tactics Security Resisting Attacks Detecting Attacks Recovering from an Attack Intrusion Detection Authenticate Users Authorize Users Maintain Data Confidentiality Maintain Integrity Limit Exposure Limit Access Attack System Detects, Resists, or Recovers from Attacks Restoration Identification See Availability Audit Trail
Modifiability Tactics 3 groups • Localize modification • Prevent ripple effect • Defer binding time
Localize modification • Maintain semantic coherence • Anticipate expected changes • Generalize the module • Limit possible options
Prevent ripple effect • Hide information • Maintain existing interfaces • Restrict communication paths • Use an intermediary
Defer binding time • Runtime registration • Configuration files • Adherence to defined protocols