Analyzing Anonymity Protocols
Analyzing Anonymity Protocols. Analyzing onion-routing security Anonymity Analysis of Onion Routing in the Universally Composable Framework in Provable Privacy Workshop 2012 A Probabilistic Analysis of Onion Routing in a Black-box Model in TISSEC (forthcoming)

Analyzing Anonymity Protocols
E N D
Presentation Transcript
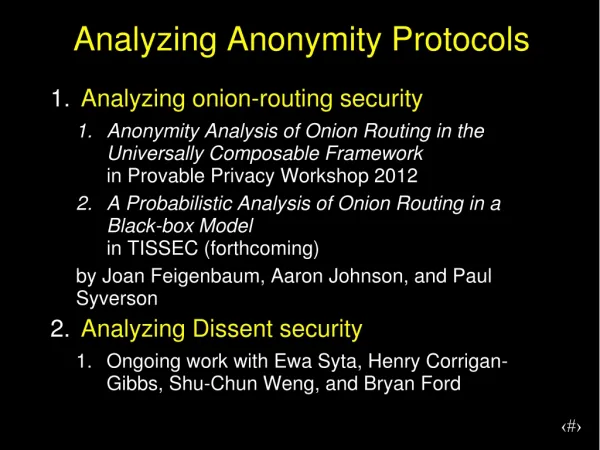
Analyzing Anonymity Protocols • Analyzing onion-routing security • Anonymity Analysis of Onion Routing in the Universally ComposableFrameworkin Provable Privacy Workshop 2012 • A Probabilistic Analysis of Onion Routing in a Black-box Modelin TISSEC (forthcoming) by Joan Feigenbaum, Aaron Johnson, and Paul Syverson • Analyzing Dissent security • Ongoing work with EwaSyta, Henry Corrigan-Gibbs, Shu-Chun Weng, and Bryan Ford
Analyzing Onion-Routing Security • Abstract (black-box) model of onion routing • Use Universally Composable (UC) framework • Focus on information leaked • Perform anonymity analysis on model
Onion-Routing Ideal Functionality Upon receiving destination d from user U u with probability b øwith probability 1-b x d with probability b øwith probability 1-b y Send (x,y) to the adversary. FOR
Black-box Model • Ideal functionality FOR • Environment assumptions • Each user gets a destination • Destination for user u chosen from distribution pu • Adversary compromises a fraction b of routers before execution
Anonymity Analysis of Black Box • Can lower bound expected anonymity with standard approximation: b2 + (1-b2)pud • Worst case for anonymity is when user acts exactly unlike or exactly like others • Worst-case anonymity is typically as if √b routers compromised: b + (1-b)pud • Anonymity in typical situations approaches lower bound
Other ideal functionality • Provably Secure and Practical Onion Routingby Backes, Kate, Goldberg, and MohammadiComputer Security Foundations Symposium 2012 • Functional primitive • Shown to UC-emulate FOR
Analyzing Dissent security • Fully rigorous definitions and proofs • Anonymity • Accountability • Integrity • Standard sequence-of-games anonymity proofs • Discovered flaws
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Discovered Shuffle Flaws 1 2 3 {I1}1:3 {I2}2:3 {I1}3 I2 m2 {I2}1:3 {I1}2:3 {I3}3 I3 m3 {I3}1:3 {I3}2:3 {I2}3 I1 m1
Discovered Shuffle Flaws 1 2 3 ? {I2}1:3 {I2}2:3 {I2}3 I2 ? {I2}1:3 {I2}2:3 {I3}3 I3 {I3}1:3 {I3}2:3 {I2}3 I2 Problem 1: Client duplication, no blamed
Discovered Shuffle Flaws 1 2 3 {I2}1:3 {I2}2:3 {I2}3 I2 {I2}1:3 {I2}2:3 {I3}3 I3 {I3}1:3 {I3}2:3 {I2}3 I2 Problem 1: Client duplication, no blamed Solution: Commit to messages first.
Discovered Shuffle Flaws 1 2 3 {I2}1:3 {I2}2:3 {I2}3 I2 {I2}1:3 {I2}2:3 {I3}3 I3 {I3}1:3 {I3}2:3 {I2}3 I2 Problem 1: Client duplication, no blamed Solution: Commit to messages first non-malleably.
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Discovered Shuffle Flaws 1 2 3 ? {I1}1:3 {I1}2:3 {I1}3 I1 ? {I1}1:3 {I1}2:3 {I1}3 I3 {I3}1:3 {I3}2:3 {I1}3 I1 Problem 3: Self-duplication, no blamed
Discovered Shuffle Flaws 1 2 3 {I1}1:3 {I1}2:3 {I1}3 I1 {I1}1:3 {I1}2:3 {I1}3 I3 {I3}1:3 {I3}2:3 {I1}3 I1 Problem 3: Self-duplication, no blamed Solution: Blame duplicate submitters.
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Discovered flaws • Adversary can unaccountably duplicate honest users’ plaintexts. • Commitments must be non-malleable. • Adversary can submit self-duplicates to cause failure with no blame. • Equivocation during broadcast can cause inconsistent final state. • Some validation checks missing
Modified Dissent • Users non-malleably commit to messages before submission. • Duplicate submission punished • Explicit reliable broadcasts added • Several validation checks added with blame • Honest members guaranteed to agree on who to blame
UC Framework • Express security primitive as an ideal functionality F • Construct a protocol Π that UC emulatesF • Running Π can replace using F in any protocol – security composes
Sequence of Games Anonymity Proof • Game 0: Original anonymity game • Game 1: Replace encrypted descriptors during shuffle with encrypted fixed messages • Game 2: Replace encrypted random seeds after shuffle with encrypted fixed messages • Game 3: Replace pseudorandom sequences with random sequences
Discovered Shuffle Flaws 1 2 3 {I1}1:3 {I2}2:3 {I2}3 I2 m2 {I2}1:3 {I2}2:3 {I3}3 I3 m3 {I3}1:3 {I3}2:3 {I2}3 I2 m2 Problem 0: Shuffle duplication attack
Discovered Shuffle Flaws 1 2 3 {I1}1:3 {I2}2:3 {I2}3 I2 {I2}1:3 {I2}2:3 {I3}3 I3 {I3}1:3 {I3}2:3 {I2}3 I2 Problem 0: Shuffle duplication attack Solution: Duplicates cause NO-GO. Blame lying shuffle.