Anonymity
190 likes | 353 Views
Attacker can see evidence of a sent message, but the sender appears no more likely to be the originator than any other potential sender in the system

Anonymity
E N D
Presentation Transcript
Types of Anonymity • Pseudonymity • Susceptible to subpoenas • Sender • Receiver / observer can’t identify sender • Receiver • Observer can’t identify receiver • Sender-receiver • Observer can’t identify that communication has been sent
Uses of Anonymity Positive • Free speech for political claims as well as non-political comments • engage in whistle-blowing • conduct commercial transactions • freedom from detection, retribution, and embarrassment • New York Times Co. vs. Sullivan, 1964 "an author's decision to remain anonymous...is an aspect of the freedom of speech protected by the First Amendment"
Uses of Anonymity Negative • Spam • DoS - • Illegal activity – anonymous bribery, copyright infringement, harassment, financial scams, disclosure of trade secrets
Assumptions • Weak attacker • Eavesdrops on first and last hop • Can introduce messages here • Strong attacker • Eavesdrops on all links • Can introduce messages anywhere • Attacker has finite time, computing power • Multiple users
Types of Attackers • Local eavesdropper • Observes inbound and outbound messages on user’s computer • Administrator • Operator or group of operators of anonymizing systems attempting to foil their own system • Remote attack • Observation at the remote end by eavesdropper or attack by the remote host
Attacks • Timing Attack, Volume Attack • Watches shape of traffic instead of content • Flooding Attack • With batch size n, attacker sends n-1 messages • Usage Pattern Attack • Consistent usage patterns leads to predictability
Levels of Anonymity Absolute Privacy Beyond Suspicion Probable Innocence Possible Innocence Exposed Provably Exposed • Beyond Suspicion • Attacker can see evidence of a sent message, but the sender appears no more likely to be the originator than any other potential sender in the system • Probable Innocence • The sender is more likely the originator than any other potential sender, but there is equal likelihood the sender is not the originator • Possible Innocence • The sender appears more likely to be the originator than to not be the originator, but there’s still a non-trivial probability that the originator is someone else
Capabilities • Latency, Bandwidth, Anonymity • Pick 2 • Human element • Repetitive usage patterns make attacks easier • Pizza effect
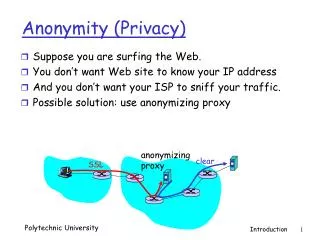
Proxy Anonymizers • Use trusted centralized servers • Anonymous remailers - Helsingius • Anonymizer.com • Hides IP address - NAT • Users not anonymous to proxy server • Susceptible to traffic analysis
Mixes • Source routing chosen by user • Shuffles order of packets • Mix cascade consists of several mixes under separate operators • Encrypted for each mix in the path • Processes packets in batches • Used to counter traffic analysis
Ai = Next Hop Address Ci = Message encrypted with public key of Mix i Mixes S = Destination Host address M = Original message 4. Mix 1 Mix 2 1. 3. 2. Mix 4 Mix 3 1. A1, C1(A3, C3(A2, C2(S, M, r2), r3), r1) 3. A2, C2(S, M, r2) 2. A3, C3(A2, C2(S, M, r2), r3) 4. S, M
Mixes • Fine for non real-time (email) • Not sufficient for VoIP, video, web • Mix waits to accumulate inputs to process as a batch (especially slow for low traffic)
Enhancements • Messages all the same length • Buffers messages until several can be sent at once • Dummy messages inserted • Between mixes • Between mixes and user • Balance end to end throughput with anonymity • Duration to wait for mixes to accumulate traffic • Percentage of dummy traffic
P5 • Decentralized • Harder to attack • Allows choice of tradeoff between anonymity / throughput • Encrypted with public key of each node in route • Nodes change packet order • Fixed message size • Users have broadcast map and route map • Noise packets counter statistical traffic analysis
User A User B Hash of User’s public key provides choice of groups. User A can send an anonymous message to User B via group */0, 1/1, 111/3, etc 01/2 is a subset of */0 – more efficient but less anonymous User A can route messages between 00/2 and 01/2 Broadcast hierarchy independent of network topology
P5 • Within a channel, P5 functions as a mix cascade • Between channels, P5 provides greater anonymity per bandwidth • For 8192 users, 1.5 Mbps provides 200Kbps with 40% loss • Resistant to Timing/Volume and DoS attacks • Susceptible to Flood Attack (Mob Attack) • User’s channel is flooded, prompting him to reveal more of his mask to gain efficiency, thereby reducing his anonymity
Conclusion • Costly to be anonymous (Use Anonymous VPN Service) • Tradeoff with throughput • Can not be completely anonymous anyway • No protection from monitoring usage patterns • Aside from this, practical anonymity can be achieved