Network Architecture Models
Network Architecture Models. Bernard Chen. Outlines. Introduction System Architecture Communication Network References. Distributed Computing.

Network Architecture Models
E N D
Presentation Transcript
Network Architecture Models Bernard Chen
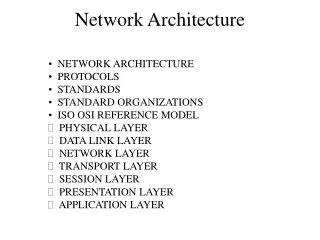
Outlines • Introduction • System Architecture • Communication Network • References
Distributed Computing • "Distributed" or "grid computing" in general is a special type of parallel computing which relies on complete computers (with onboard CPU, storage, power supply, network interface, etc.) connected to a network by a conventional network interface, such as Ethernet. This is in contrast to the traditional notion of a supercomputer, which has many CPUs connected by a local high-speed computer bus.
Distributed System Categories • Multiple computer systems collaborating to deliver a single application • Can be broadly applied to high-performance computing (HPC) whereby multiple computers, commonly called clusters, collaborate to solve a single problem • Multiple applications collaborating together as a system • Can be broadly applied to application integration whereby multiple discrete applications receive a copy of “some” data and process the data accordingly.
Distributed Service • Distributed Service depend on the system architecture and the underlying communication network. • In the upper level, system architecture is an abstract description of major components and their relation • In the lower level, network architecture specifies the communication facilities
Outlines • Introduction • System Architecture Client-Server Grid Peer-to-Peer Model • Communication Network • References
Architectures: Client-Server • Workstation-server model [Chow, 1997] • A work station may serve as a Stand-Alone computer or as a part of an overall network • Some workstations are Diskless Workstation, all file and boot services are supported by the network
Architectures: Client-Server • Processor-Pool model • Most workstations are idling at any instance in time. • Collects all processing power in Processor Pool Server • Users access a virtual single computer system with intelligent terminals
Integrates and coordinates resources and users that live within different control domains Built from multi-purpose protocols and interfaces that address such fundamental issues as authentication, authorization, resource discovery, and resource access. Allows its constituent resources to be used in a coordinated fashion to deliver various qualities of service, (e.g. response time, throughput, availability, and security) [Foster, 2002] Architectures: Grid
Architectures: Peer-to-Peer Model • In this model, end users share resources in a peer style, potentially acting as both CLIENT and SERVER • Advantages: 1. removes single point failure and associated performance bottlenecks 2. releases the network traffic overhead by providing service locally
P2P Categories • P2P were classified into three different categories: 1. Centralized P2P systems 2. Decentralized structured P2P systems (there is no central server and peers are structured according to some strict rules) 3. Decentralized unstructured P2P systems
“Blind Search” • The unstructured P2P system usually use a “blind search” method to find the requested data • “Blind Search” propagate a query to a number of peers randomly • Replication technique is often used to improve the performance of blind search • When data objects that are accessed more frequently are distribute more copies.
Some parameters • N: number of peers • TTL: number of max hops for search a query
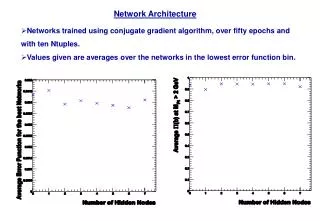
The probability that peer 2 and 3 receives messages from peer 1 is 50% If every peer issues a query with TTL=1, the average messages received by peer 1,2,4 are 5/6, 5/6, and 4/3 Random Walk Method
Potential Energy • Potential energy E: a peer’s capability of receiving query message (Feng et al, 2007) • Then a peer’s potential energy is closely related to the potential energy of its neighbors and the probability that it can receive messages from neighbors • Therefore, it is defined as:
Potential Energy • They assign the initial value as 1/n since each peer has the same probability to generate query • If TTL=1 =>
Outlines • Introduction • System Architecture • Communication Network Communication Network Wired Network Wireless Network • References
Communication Network • The existence of multiple computer systems in a distributed system implies the need to interconnect these computers • System components may be connected by point-to-point or multipoint communication channels
Communication Network • Point-to-point links are direct connections between pairs of computer nodes • Multiple links allow the connection of nodes into a cluster and are usually implemented by using common buses or interconnection networks (switches)
Wired Interfaces: Ethernet • Family of local-area network (LAN) products covered by the IEEE 802.3 standard that defines CSMA/CD protocol • Carrier sense—Each station continuously listens for traffic on the medium to determine when gaps between frame transmissions occur. • Multiple access—Stations may begin transmitting any time they detect that the network is quiet (there is no traffic). • Collision Detect – Execute a random backoff before retransmission.
Wired Interfaces: Ethernet • Three data rates are currently defined for operation over optical-fiber and twisted-pair cables: • 10 Mbps—10Base-T Ethernet • 100 Mbps—Fast Ethernet • 1000 Mbps—Gigabit Ethernet
Wired Interfaces: Ethernet • Local area networks can be connected to form a Metropolitan Area Network (MAN) or a Wide Area Network (WAN)
Wireless: 802.11 • Specification are wireless standards that specify an "over-the-air" interface between a wireless client and a base station or access point, as well as among wireless clients. • Data Rates up to 54 Mbps • Can operate in Infrastructure (base station) or peer-to-peer mode (ad-hoc). • Commonly used in MANETs
Outlines • Introduction • System Architecture • Communication Network • References
References • Chow, Randy, et. al.,Distributed Operating Systems & Algorithms, Addison Wesley, March 18, 1997 • Ge, Z.; Figueiredo, D.R.; Sharad Jaiswal; Kurose, J.; Towsley, D.; Modeling peer-peer file sharing systems, INFOCOM 2003. Twenty-Second Annual Joint Conference of the IEEE Computer and Communications Societies. IEEE Volume 3, 30 March-3 April 2003 Page(s):2188 - 2198 vol.3 • Kwang Koog Lee; Seong Hoon Kim; Yong Soon Choi, A Mesh Routing Protocol using Cluster Label in the ZigBee Network; Mobile Adhoc and Sensor Sysetems (MASS), 2006 IEEE International Conference on Oct. 2006 Page(s):801 - 806 • Foster, Ian, What is a Grid? A Three Point Checklist, Argonne National Laboratory & University of Chicago, July 20, 2002 • Enterprise Distributed Systems and Infiniband, Cisco 2006 • SCSI RDMA Protocol (SRP), Intel 2002
Thanks • Questions??