UPS
UPS. The Undetectable Packet Sniffer. Introducing the TVSG Dev Team. AutoNiN – Software, Team Lead Spyder~1 – Hardware Mystic – Integration JustaBill – Organization. Concept. Place a stealthed hostile packet sniffer on a victim network. Physical concealment

UPS
E N D
Presentation Transcript
UPS The Undetectable Packet Sniffer
Introducing the TVSG Dev Team • AutoNiN – Software, Team Lead • Spyder~1 – Hardware • Mystic – Integration • JustaBill – Organization
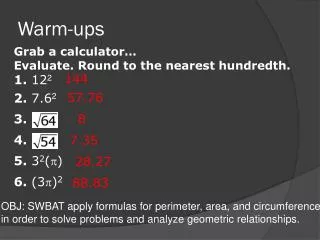
Concept Place a stealthed hostile packet sniffer on a victim network. Physical concealment is to hide in plain sight - posing as an Uninterruptible Power Supply (UPS). Network concealment involves clandestine exfiltration methods like Auto-IP Detection and encrypted UDP tunneling.
Caveat - Prototype • Unit presented today is a prototype (mk II) unit demonstrating basic concepts. Unit is really not "Undetectable" but should be difficult to detect, even in its nascent state. • Additional hardware and software features are being researched to further decrease detectibility and increase attack effectiveness.
Undetectable? • Not really… • Takes advantage of today’s overworked, under-resourced, over-managed and under-trained Information Technology staff • Completely blocked by proxies (but we’ll fix that soon enough!)
Overview • Introduction • Integration • Hardware • Software • Practical Demonstration • Questions & Answers
Integration • Overarching Goal – Stealth: • Tried to maintain 'Stock' look as much as possible.
Hardware Requirements • 486 or Higher CPU • 64Mb or More RAM • 1Gb or More Hard Drive • No moving parts • Small form factor • Integrated network • Most Important: Cheap!
System Components • UPS Chassis • Power Supply • Embedded Computer • Network Hub
Physical Components Embedded PC Power Supply 110v AC Chassis RJ-45’s Hub Ethernet 5v DC In Out
UPS Chassis • Tried several UPS Chassis before we found one that worked well
Power Supply • Needed to convert the 110v AC provided by the wall to 3.3v, 5v, and/or 12v DC needed by the other components in the system. Most UPS power supplies are trickle-charge systems that cannot produce enough power to run our covert system.
Variety of Embedded Systems • Older, Slower, Larger Systems are the Cheapest • Popular Embedded Manufacturers: • http://www.advantech.com • http://www.kontron.com • http://www.ampro.com • http://www.emj.com
Our Selected Mainboard: • Kontron's Coolmonster: • Pentium-166 with passive cooling heatsink • 128MB PC-100 SDRAM • 44-Pin IDE Channel for temporary CD-ROM Drive • 40-Pin IDE Channel for 2.5" 2GB Laptop Hard Drive • Single 10/100 Ethernet port • PS/2 Keyboard & Mouse ports, VGA Port • PISA Interface (bus expansion)
Network Hub Our embedded system had only 1 Ethernet port, so we could not bridge two interfaces together. For simplicity's sake, we ripped a 10/100 hub out of its case and placed it inside ours. Runs off 5v DC, just like the embedded PC.
Network Connections • Repeater hub connected to both wall and client RJ45 jacks. Embedded PC also connected to hub. • Good: Client can still access network even if UPS is booting or down • Bad: Can't do Proxy-ARP attacks, client sees all UPS traffic • Ugly: Either way, client gets Ethernet 'Link' from the UPS, which is odd
Software • OS is Redhat 7.2 patched & stripped • Custom Perl and Shell Scripts • Additional Malware added: • NetCat by Hobbit & Weld • dSniff by Dug Song • Nmap by Fyodor • thcrut by The Hacker’s Choice
Malware Installation - NetCat • Many thanks to Hobbit & Weld for this incredibly versatile tool. • Used for UPS <-> Listening Post Communications. • Default configuration sends it over UDP port 53 to exploit firewall rules that permit outbound DNS queries from desktop clients. http://freshmeat.net/projects/netcat/?topic_id=150
Issues - UDP/53 Tunneling • Modern IDS/IDP systems can detect UDP tunneling • Layer 7-Aware sniffers can detect that while the traffic is going over UDP/53, the payload is decidedly not DNS
Tunneling Alternatives • Simple Port 80/HTTP Tunneling • Mask UPS requests in HTTP URL's • LP replies in HTML WebPages • Advanced DNS Tunneling • Mask UPS requests in DNS requests • LP replies in DNS replies
Malware Installation - DSniff • Many thanks to Dug Song for his excellent suite of Sniff/Snarf/Spy tools. • Minor tweak in the makefile for the Berkeley DB path and we were set! http://www.monkey.org/~dugsong/dsniff/
What We Used - DSniff • macof - MAC address flooder - stuffs CAM table • dsniff - Cleartext authentication extractor • filesnarf - NFS interceptor • mailsnarf - Email interceptor • urlsnarf - URL interceptor • msgsnarf - Instant Messenger interceptor
Malware Installation - Nmap Thanks Fyodor, you rock! • Comes as an RPM with Redhat 7.2, no installation really necessary • Awesome portscanning/host locating tool, used to detect permitted connectivity outbound through victim firewall http://www.insecure.org/nmap/
Custom Scripts • A variety of Perl scripts were developed to handle UPS <-> Listening Post communications, command and control, including IP Address Mode, Active Scan Commands and Exfiltration Methods. http://www.tvsg.org/ups
Custom Scripts ups.pl - Master Control Script • Started as a service on UPS boot time and health checked by a cron job, this script is responsible for monitoring UPS-specific processes and initiating connections to the command queue server.
UPS Process Flow Load Config Configure Network Auto-Identify Network (if Configured) Confirm Network Confirm/Update System Settings Contact Listening Post Get Commands Process Commands
IP Modes 4 Different Methods of Configuring IP: 1. No IP Mode (Dumb Sniffer) 2. Fixed IP Mode (Good for Testing) 3. DHCP Mode (Not very Stealthy!) 4. Stealth IP Mode (Auto-find Subnet/Gateway)
Custom Scripts netsnarf.pl • Required for IP Mode 4 – automatic network discovery • Watches the network for ARP requests and replies for network information to determine local network topography • Uses The Hacker’s Choice “R U There” (thcrut) to ARP scan IP’s on the same layer 2 segment
Custom Scripts netcheck.pl • Uses nmap and host to probe Internet targets to verify external connectivity. • Nmap 3 popular websites (HTTP) • Unix ‘host’ command to 3 DNS Root Servers • Nmap to Listening Post on UDP/53
Custom Scripts Various Shell Scripts • Other scripts for UPS process management, task automation, and other cool stuff...
Command and Control Internet LP UDP/53 NAT/Firewall Corporate Network TCP/22 (SSH) TCP/80 Attacker UPS
Custom Scripts client.pl & server.pl • Remote command fetch system with DES encryption, randomly generated keys, and pre-shared key system. • Client connects at intervals controlled by the master control script to Server to check command queue for changes in configured behavior.
UPS Connectivity 2 Different Methods of Communicating: 1. UDP/53 (looks like DNS) beacon to config server 2. TCP/80 (looks like HTTP) reverse shell to LP
Demonstration • Our demonstration will place the UPS behind a NAT device along with a victim PC • We will place a Listening Post outside the NAT and command our unit to monitor the user • We will then exfiltrate the captured data to the LP
Victim Demonstration Lab Server External Network LP Server NAT/Firewall Attacker Internal Network UPS Username: Loser Password: password Username: Loser Password: password Email Data: Subject: Watch out for hackers!
How to Defeat? • Inspect all items entering the premises • Deny clients direct outward access (DNS, HTTP, ICMP, etc) • Require the use of internal servers for all services – HTTP, DNS, Mail, etc. • Use encrypted services like SSH, HTTPS, POP3S, SMTPS, or even IPSEC for internal as well as external traffic.
Questions? • Thanks for Attending…