Exploring Entropy, Secrecy, and Unforgeability in Cryptography
This comprehensive guide delves into entropy, secrecy, and unforgeability in cryptography, covering concepts such as perfect secrecy, computational secrecy, pseudoentropy, and more. Learn about the applications and security properties involved in commitment schemes.

Exploring Entropy, Secrecy, and Unforgeability in Cryptography
E N D
Presentation Transcript
Omer ReingoldWeizmann Institute Salil VadhanHarvard University Iftach Haitner Microsoft Research Hoeteck WeeQueens College, CUNY Inaccessible Entropy TexPoint fonts used in EMF. Read the TexPoint manual before you delete this box.: AAAA
outline • Entropy • Secrecy & Pseudoentropy • Unforgeability & Inaccessible Entropy • Applications
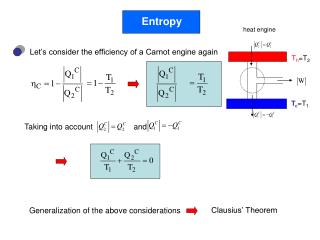
Entropy Def: The Shannon entropyof r.v. X is H(X) = ExÃX[log(1/Pr[X=x)] • H(X) = “Bits of randomness in X (on avg)” • 0 · H(X) · log|Supp(X)| X uniform onSupp(X) X concentratedon single point
Conditional Entropy H(X|Y) = EyÃY[H(X|Y=y)] • Chain Rule: H(X,Y) = H(Y) + H(X|Y) • H(X)-H(Y) · H(X|Y) · H(X) • H(X|Y) = 0 iff 9 f X=f(Y).
Worst-Case Entropy Measures • Min-Entropy: H1(X) = minx log(1/Pr[X=x]) • Max-Entropy: H0(X) = log |Supp(X)| H1(X) · H(X) · H0(X)
outline • Entropy • Secrecy & Pseudoentropy • Unforgeability & Inaccessible Entropy • Applications
Perfect Secrecy & Entropy Def [Sh49]: Encryption scheme (Enc,Dec) has perfect secrecy if 8 m,m’ 2 {0,1}nEncK(m) & EncK(m’) are identically distributed for a random key K. Thm [Sh49]: Perfect secrecy ) |K| ¸ n
Perfect Secrecy ) |K|¸ n Proof: • Perfect secrecy) (M,EncK(M)) ´ (Un,EncK(M)) for M,Unà {0,1}n) H(M|EncK(M)) = n • Decryptability) H(M|EncK(M),K) = 0) H(M|EncK(M)) · H(K).
Computational Secrecy Def [GM82]: Encryption scheme (Enc,Dec) has computational secrecy if 8 m,m’ 2 {0,1}nEncK(m) & EncK(m’) are computationally indistinguishable. ) can have |K| ¿ n.
Where Shannon’s Proof Breaks • Computational secrecy) (M,EncK(M)) ´c (Un,EncK(M)) for M,Unà {0,1}n)“Hpseudo(M|EncK(M))” = n • Decryptability) H(M|EncK(M)) · H(K). Key point: can have Hpseudo(X) À H(X)e.g. X = G(Uk) for PRG G : {0,1}k! {0,1}n
Pseudoentropy Def [HILL90]: X has pseudoentropy ¸ k iff there exists a random variable Y s.t. • Y ´c X • H(Y) ¸ k
Application of Pseudoentropy Thm [HILL90]:9 OWF )9 PRG Proof outline: OWF hardcore bit [GL89]+hashing X with pseudoentropy ¸ H(X)+1/poly(n) repetitions X with pseudo-min-entropy ¸ H0(X)+poly(n) hashing PRG
outline • Entropy • Secrecy & Pseudoentropy • Unforgeability & Inaccessible Entropy • Applications
Unforgeability • Crypto is not just about secrecy. • Unforgeability: security properties saying that it has hard for an adversary to generate “valid” messages. • Unforgeability of MACs, Digital Signatures • Collision-resistance of hash functions • Binding of commitment schemes
Ex: Collision-resistant Hashing F = { f : {0,1}n! {0,1}n-k} • Shrinking: H(X|Y,F) ¸ k • Collision Resistance: From A’s perspective, X is determined by Y,F ) “accessible” entropy 0 A B F XÃ {0,1}n F ÃF Y Y=F(X) X
Ex: Collision-resistant Hashing F = { f : {0,1}n! {0,1}n-k} Collision Resistance:9 function ¼s.t. X = ¼(F,Y,S1) except w/negligible prob. A* B F F ÃF Y toss coins S1 toss coins S2 X
Ex: Collision-resistant Hashing F = { f : {0,1}n! {0,1}n-k} Collision Resistance:9 function ¼s.t. X 2 {¼(F,Y,S1)} [ f-1(Y)c A* B F F ÃF Y toss coins S1 toss coins S2 X
Measuring Accessible Entropy Goal: A useful entropy measure to capture possibility that Hacc(X) ¿ H(X) 1st attempt: X has accessible entropy at most k if there is a random variable Y s.t. • Y ´c X • H(Y) · k Not useful! every X is indistinguishable from some Y of entropy polylog(n).
Inaccessible Entropy Idea: Protocol (A,B) has inaccessible entropy if H(A’s messages from B’s point of view) > H(A*’s messages from A*’s point of view) Real Entropy Accessible Entropy
Real Entropy A B1 B Def: The real entropy of (A,B) is i H(Ai | B1,A1,…,Bi) A1 B2 A2 Bm Am
Accessible Entropy A* B1 B • Tosses coins Si • Sends message Ai • Privately outputs justification Wi(e.g. consistent coins of honest A) A1 coins S1 W1 B2 A2 coins S2 W2 Bm Am coins Sm Wm What A* does at each round
Accessible Entropy A* B1 B Def: (A,B) has accessible entropy at most k if for every PPT A* i H(Ai|B1,S1,B2,S2,…,Si-1,Bi) · k • Remarks • Needs adjustmentin case A*outputs invalidjustification. • Unbounded A* can achieve real entropy. A1 coins S1 W1 B2 Assume never A2 coins S2 W2 Bm Am coins Sm Wm
Ex: Collision-resistant Hashing F = { f : {0,1}n! {0,1}n-k} Real Entropy = H(Y|F)+H(X|Y,F) = H(X|F) = n A B F XÃ {0,1}n F ÃF Y Y=F(X) X
Ex: Collision-resistant Hashing F = { f : {0,1}n! {0,1}n-k} Accessible Entropy = H(Y|F)+H(X|F,S1) · (n-k) + neg(n) A* B F F ÃF Y toss coins S1 toss coins S2 X
outline • Entropy • Secrecy & Pseudoentropy • Unforgeability & Inaccessible Entropy • Applications
Commitment Schemes COMMIT STAGE S R m
Commitment Schemes REVEAL STAGE S R m
Commitment Schemes S R COMMIT STAGE m2{0,1}n REVEAL STAGE (m,K) accept/reject
Security of Commitments COMMIT(m) & COMMIT(m’) indistinguishableeven to cheating R* • Hiding • Statistical • Computational • Binding • Statistical • Computational S R COMMIT STAGE m2{0,1}n Even cheating S*cannot reveal(m,K), (m’,K’) with mm’ REVEAL STAGE (m,K) accept/reject
Statistical Security? • Hiding • Statistical • Computational • Binding • Statistical • Computational S R COMMIT STAGE m2{0,1}t REVEAL STAGE (m,K) accept/reject Impossible!
Statistical Binding • Hiding • Statistical • Computational • Binding • Statistical • Computational S R COMMIT STAGE m2{0,1}n REVEAL STAGE (m,K) accept/reject Thm [HILL90,Naor91]: One-way functions ) Statistically Binding Commitments
Statistical Hiding • Hiding • Statistical • Computational • Binding • Statistical • Computational S R COMMIT STAGE m2{0,1}n REVEAL STAGE (m,K) accept/reject Too Complicated! Thm [HNORV07]: One-way functions ) Statistically Hiding Commitments
Our Results I • Much simpler proof that OWF) Statistically Hiding Commitmentsvia accessible entropy. • Conceptually parallels [HILL90,Naor91] construction of PRGs & Statistically Binding Commitments from OWF. • “Nonuniform” version achieves optimal round complexity, O(n/log n) [HHRS07]
Our Results II Thm: Assume one-way functions exist. Then: NP has constant-round parallelizable ZK proofs with “black-box simulation” m constant-round statistically hiding commitments exist. ( * due to [GK96,G01], novelty is )
Statistically Hiding Commitments& Inaccessible Entropy Statistical Hiding: H(M|C) = n - neg(n) S R COMMIT STAGE MÃ{0,1}n C REVEAL STAGE M K
Statistically Hiding Commitments& Inaccessible Entropy Statistical Hiding: H(M|C) = n - neg(n) Comp’l Binding: For every PPT S* H(M|C,S1) = neg(n) S* R COMMIT STAGE coins S1 C REVEAL STAGE coins S2 M K
OWF ) Statistically Hiding Commitments: Our Proof OWF interactive hashing [NOVY92,HR07] (A,B) with real entropy ¸ accessible entropy+log n repetitions (A,B) with real min-entropy ¸ accessible entropy+poly(n) (interactive) hashing [DHRS07]+UOWHFs [NY89,Rom90] “m-phase” commitment cut & choose statistically hiding commitment
Cf. OWF ) Statistically Binding Commitment [HILL90,Nao91] OWF hardcore bit [GL89]+hashing X with pseudoentropy ¸ H(X)+1/poly(n) repetitions X with pseudo-min-entropy ¸ H0(X)+poly(n) hashing PRG expand output & translate Statistically binding commitment
OWF ) Statistically Hiding Commitments: Our Proof OWF interactive hashing [NOVY92,HR07] (A,B) with real entropy ¸ accessible entropy+log n repetitions (A,B) with real min-entropy ¸ accessible entropy+poly(n) (interactive) hashing [DHRS07]+UOWHFs [NY89,Rom90] “m-phase” commitment cut & choose statistically hiding commitment
OWF ) Inaccessible Entropy f : {0,1}n! {0,1}m OWF • Real Entropy = n • Can show: Accessible Entropy · n-log n A B B1 Chooselinearly indep. B1,…,Bmà {0,1}m Xà {0,1}n h B1,Yi Y=f(X) Bm h Bm,Yi X
Claim: Accessible Entropy · n-log n For simplicity, assume |f-1(y)| = 2k8 y2 Im(f) f : {0,1}n! {0,1}m OWF. A* B B1 h B1,Yi entropy · t = n-k-2log n Bt h Bt,Yi Bm Claim: entropy = neg(n) h Bm,Yi X entropy · k
Claim: Accessible Entropy · n-log n For simplicity, assume |f-1(y)| = 2k8 y2 Im(f). t=n-k-2log n f : {0,1}n! {0,1}m OWF. A* B B1 h B1,Yi Bt h Bt,Yi Claim:9 at most oneconsistent Y s.t. A* canproduce a preimage(except w/neg prob,)
Claim: Accessible Entropy · n-log n For simplicity, assume |f-1(y)| = 2k8 y2 Im(f). t=n-k-2log n f : {0,1}n! {0,1}m OWF. A* B B1 h B1,Yi poly(n) Bt Im(f) h Bt,Yi Claim:9 at most oneconsistent Y s.t. A* canproduce a preimage(except w/neg prob,) Interactive Hashing Thms [NOVY92,HR07]: A* can “control” at most 1 consistent value
Claim: Accessible Entropy · n-log n For simplicity, assume |f-1(y)| = 2k8 y2 Im(f) f : {0,1}n! {0,1}m OWF. A* B B1 Analysis holdswhenever |f-1(Y)| ¼ 2k h B1,Yi entropy · t = n-k-2log n Bt Choice of k contributesentropy · log n h Bt,Yi Bm entropy = neg(n) h Bm,Yi X entropy · k
Conclusion Complexity-based cryptography is possible because of gaps between real & computational entropy. Secrecypseudoentropy > real entropy Unforgeabilityaccessible entropy < real entropy What else can we do with inaccessible entropy?
Research Directions • Remove “parallelizable” condition from ZK result. • Use inaccessible entropy for new understanding/constructions of MACS and digital signatures. • Formally unify statistical hiding & statistical binding.