AMI
6. 7. 5. 1. 2. 3. 4. http://sourceforge.net/projects/acacia/ Contact :t.doherty@physics.gla.ac.uk. VOMS and Web Portals How the ATLAS Virtual Organisation Membership Service (VOMS) was integrated with the ATLAS Metadata Interface (AMI). AMI

AMI
E N D
Presentation Transcript
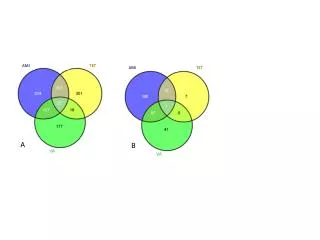
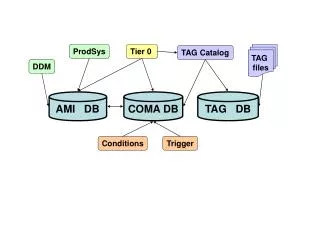
6 7 5 1 2 3 4 http://sourceforge.net/projects/acacia/Contact:t.doherty@physics.gla.ac.uk VOMS and Web Portals How the ATLAS Virtual Organisation Membership Service (VOMS) was integrated with the ATLAS Metadata Interface (AMI) . AMI • AMI is a framework, and one of its application fields is the dataset metadatastorage and access for ATLAS. • It provides a set of generic tools for managing database applications. • It has a three-tier architecture: • with a lower tier that supports a connection to any Relational Database Management System (RDBMS) using JDBC and SQL. • the middle tier assumes that the databases have an AMI compliant self-describing structure. • the client tier provides a generic web interface and a generic command line interface. VOMS From the authorisation point of view, a Grid is established by enforcing agreements between Grid applications and VOs There are two types of information to be recorded: - general information regarding the relationship of the user with his VO: groups he belongs to, roles he is allowed to cover and capabilities he should present to Grid applications for special processing needs; - information regarding what the user is allowed to do within a Grid application, owing to his membership of a particular VO. The first kind of information can be contained in a server managed by the ATLAS VO itself called the Virtual Organisation Membership Service (VOMS), while the second is probably best kept at the local sites, near the resources or application involved, in this case AMI. The problem The most crucial problem for the mechanism above is that browsers are not able to handle proxy certificates. Taking into consideration that a browser client is one of the major clients developed for AMI, this problem has to be resolved, as the lack of a proxy certificate would result in no VOMS attributes being assigned. The AMI-VOMS Solution 1) The grid user authenticates themselves to AMI using a grid certificate 2) AMI allows the user to launch a Java Web Start (JWS) application to create a VOMS proxy 3) The user chooses their x509 certificate, a proxy certificate is created and sent to the VOMS server 4) The VOMS server sends back a VOMS proxy certificate to the JWS application 5) Using Axis set up in Tomcat the VOMS proxy file is uploaded to the server via a secure web service attachment 6) A proxy delegation service is available on the server 7) The proxy certificate is cached on the server, allowing local authentication and authorisation, and permitting the server to act on the users behalf AMI's Local Role Mechanism With the AMI-VOMS delegation service solution in place there is minimal implementation needed to fully integrate VOMS with AMI. This is because AMI already had an authorisation mechanism which is illustrated above.