MalWare on mobile devices
CS239 – Fall 2010. MalWare on mobile devices. Stefano Emiliozzi , Simardeep Uppal. Introduction. Mobile devices, such as smart phone or PDA have became more and more widespread, and often essential in our everyday life.

MalWare on mobile devices
E N D
Presentation Transcript
CS239 – Fall 2010 MalWare on mobile devices Stefano Emiliozzi, SimardeepUppal
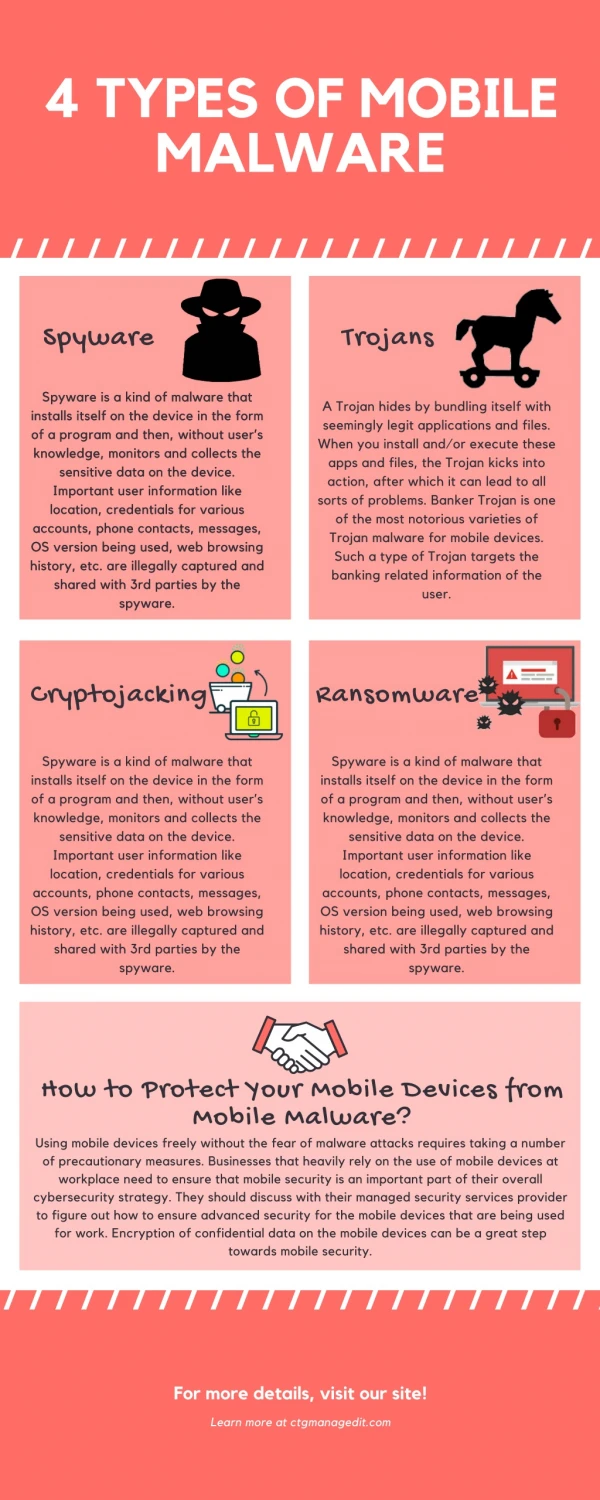
Introduction • Mobile devices, such as smart phone or PDA have became more and more widespread, and often essential in our everyday life. • Usually they contain lots of sensitive information, like a list of contacts, ingoing/outgoing call, text messages, and on latest model a calendar of our schedule, emails, our current position (if the phone has embedded GPS). • A phone today is as powerful as a desktop PC of 5 years ago. • Latest models feature a complete OS, but for many people they are just phones, so there is a under-estimation of the risk connected to phone security. • This makes phones an interesting target for malicious users. • Damages that a user can sustain are financial loss, privacy and confidentiality, slowdown of processing speed, battery life.
Malware Growth • On mobile devices there are a multitude of infection channels: • SMS, MMS • Infrared • Bluetooth • Email • Web • Malware for mobile is growing constantly:
Do we have to worry? • Why we are not hearing about malware outbreaks, then? • OS Market Share of PC vs Mobile Phones (September 2010) • This doesn’t mean we don’t have to worry!
Possible smart-phone attacks • Identity theft and spoofing • Smartphone System Compromise • DoS to base stations • DDoS to call centers and switches • Remote wiretapping • SMS spamming
DoSto base stations • Radio spectrum sharing schemes include TDMA, FDMA, or logical “channels” • Cover all Base Station timeslots by ‘spoofed’ requests • Few smartphone zombies can block 1 frequency band Smart-phone zombies
DDoS to call centers and switches • Why a problem only on smartphone? • Usage of APIs for calling phones through code • Spoofing the SIM easy: Smartphone Zombie
Defenses • Internet side protection • Base station performs shielding for users? • Possible Challenges? • Telecom side protection • Behavior is highly predictable • Abnormal behavior detection : Easy data mining • Reaction building blocks already exist • Reactions (Rate limiting, Call filtering, Blacklist) • Smart-phone side protection • Analyze Malware and Prevent it from Executing
Smart-phone hardening • Feature reduction • E.g., turn off Bluetooth when not active • OS hardening • E.g., always display callee number when making a phone call • Lighting up LCD display when dialing • Hardware hardening • SIM card to authenticate OS and applications
Analysing Malware • If we want to get protection which option do we have? • Signature Based Detection • Useful mostly for post-infection cleanup • Mobile devices have limited resources such as CPU, memory, and battery power • Mobile OSes have important differences in the way file permissions and modifications to the OS are handled. Need to consider different OS differently. Is this feasable? Is a better solution possible • Are there other options available around? • Behavioral Analysis • Even if powerful a phone is still used primarily as a phone. • Emails or text messages are sent after manual user interaction. • Wi-fi or Bluetooth connection are opened manually by users. • We can be pretty suspicious if any of these activities are done in background. • This kind of analysis doesn’t cover web navigation, though.
Mobile and Ubiquitous Malware • Main idea is to apply an anomaly detection model. • Instead of looking for malicious software, physically scanning mobile phone memory and comparing it to a signature database, we evaluate phone behavior, trying to identify anomalies. • Important concept of such model is the presence or absence of user interaction. • It is possible to infer user activity monitoring the frequencies of keystrokes on a keyboard or touches on a touch screen. • It is possible to have a threshold that tell us if a user is active or not: • GET UserInactivityTime • IF UserInactivityTime – 10s • RETURN User is inactive • ELSE • RETURN User is active
Ontology-based Malware Behavioral Analysis • We can apply very well known concepts in data mining and data analysis to build a model that will help us to understand the threat, and (possibly) to contrast it better. • Main idea here is to build an ontology, which can be seen as a hierarchy of concepts with attributes an relations, within a specific domain. • Analyzing behavior of 35 kinds of malware made it possible to categorize them, extracting features and finally build an ontology.
Behavioral Detection • Run-time behavior of an application is monitored and compared against malicious and/or normal behavior profiles • Possible to detect exploits in linked libraries • More generic to handle the than API signatures • More resilient to polymorphic worms and code obfuscation • Database of behavior profiles is much smaller than that needed for storing signature-based profiles • Suitable for resource limited handsets • Has potential for detecting new malware
Detecting Malicious Behavior • Behavior Signature: Manifestation of a specification of resource accesses and events generated by applications • It is not sufficient to monitor a single event of a process in isolation in order to classify an activity to be malicious • Temporal Pattern: The precedence order of the events and resource accesses, is the key to detect malicious intent • Eg Consider a simple file transfer by calling the Bluetooth OBEX system call in Symbian OS • (received file is of type .SIS) and (that file is executed later) and (installer process seeks to overwrite files in the system directory) • On their own, any such call will appear harmless
Representation of Malicious Behavior • Complex Behavior: specified using temporal logic instead of classical propositional logic • Specification language of TLCK(Temporal Logic of Causal Knowledge) is used to represent malicious behaviors within the context of a handset environment • A finite set of propositional variables interposed using TLCK • Each variable (when true) confirms the execution of either • A single or an aggregation of system calls • An event such as read/write access to a given file descriptor, directory structure or memory location
Operators used to define Malicious Behavior Logical Operators: Temporal Operators:
Essence of Behavior Classification Training Dataset Applications (Malwre + Legitimate) Set of Behavior Signatures Obtain Partial/ Full Signatures Remove Redundant Signatures Testing Dataset
Essence of Behavior Detection • Due to fewer signatures, the malware database is compact and can be place on a handset • Can potentially detect new malware and their variants • Behavioral detection results in high detection rates