Error Detection and Correction Techniques in Communication Systems
Explore popular error detecting schemes like Cyclic Redundancy Check (CRC) and Hamming codes, understanding CRC generation and performance analysis, detecting burst and single bit errors, implementing CRC in hardware, and delving into Reed-Solomon codes for burst error correction.

Error Detection and Correction Techniques in Communication Systems
E N D
Presentation Transcript
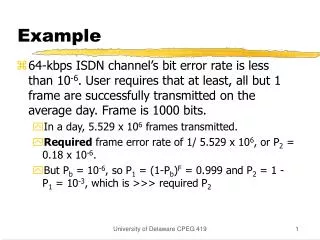
Example • 64-kbps ISDN channel’s bit error rate is less than 10-6. User requires that at least, all but 1 frame are successfully transmitted on the average day. Frame is 1000 bits. • In a day, 5.529 x 106 frames transmitted. • Required frame error rate of 1/ 5.529 x 106, or P2 = 0.18 x 10-6. • But Pb = 10-6, so P1 = (1-Pb)F = 0.999 and P2 = 1 - P1 = 10-3, which is >>> required P2 University of Delaware CPEG 419
Cyclic Redundancy Check • CRC is one of the most effective and common error detecting schemes. • Let M be m-bit message, G (r+1)-bit pattern. • Transmitter appends r 0’s to M, 2r*M. • Divide 2r*M by G and add the remainder from 2r*M forming T (m+r bits), which is transmitted. • Receiver computes T/G; if remainder, then error. University of Delaware CPEG 419
Cyclic Redundancy Check • CRC is one of the most effective and common error detecting schemes. • Represent frames as polynomials • M= 1010001101 -> x9+x7+x3+x2+x0 • Both source and destination use a generator polynomial G – r bits/r+1 degree polynomial • Idea: Transmit extended frame [M|V], such that the polynomial representation is exactly divisible by G. Thus, if G does not exactly divide the received frame, there is an error. University of Delaware CPEG 419
CRC • How to find V such that G exactly divides [M|V]? • Divide xrM by G. Set V = the remainder. • [M|V] = xrM + V • [M|V] = (xrM + V)/G = xrM/G + V/G = S + V/G + V/G = S + 2V/G. But in binary 2 is the same as zero. So [M|V] / G = S. University of Delaware CPEG 419
CRC Example • Frame M 1010001101 = x9+x7+x3+x2+x0. • Pattern G 110101. • Dividing (frame*25) by pattern results in 01110. • Thus T 101000110101110. • Receiver can detect errors unless received message Tr is divisible by G. University of Delaware CPEG 419
CRC Performance and Generators • Instead of [M|V] we receiver [M|V] + E (E is the error). • Burst errors – CRC detects bursts of length r or less. • a string of errors, with E = 0 …0 1 X X X X 1 0 … • E(x) = xi(xk-1 + … + 1) where the burst length is k. • If G is degree k or greater and G has a 0th degree term, then G will not divide E. e.g. Will CRC detect single bit errors? Suppose that you use 4 bits (as in Ethernet), and BER is 106 what is the frame error probability? University of Delaware CPEG 419
CRC Performance and Generators • Burst Errors Continued • If the burst has length r+1, then the errors will not be detected if the burst is the same as G. If an error of length r+1 occurs and all combinations of errors are equally likely, then the burst will match G with prob. ½r-1. (So prob is BERr+1 x½r-1) • In general, for longer bursts, the prob. is ½r University of Delaware CPEG 419
CRC • Lastly, if G contains x+1 as a factor, and E has an odd number of bit, then G will not divide E. • In IEEE 802 x32 + x26 + x23 + x22 + x16 + x12 + x11 + x10 + x8 + x7 + x5 + x4 + x2 + x + 1 • CRC can be implemented in hardware with registers. • Problem: errors can occur in some pattern, so the probabilities are not quite right. University of Delaware CPEG 419
Error Correcting Codes • Hamming distance between bit strings: • The number of bits where the string differ • XOR them and count the 1’s • 1 0 1 0 0 1 0 0 1 0 0 0 1 1 0 = 2 – the distance is two. University of Delaware CPEG 419
Error Correcting codes • Take an n bit string and encode it as n+k bits in such a way that each encoded n bit string is at least d distance from any other encoded n bit string. Then you can detect errors of length d. • Do the same thing, but make it so the distance between any encoded n bit string is 2d+1 bits. Then the an error of d bits or less can be corrected by assigning the string to its closest legal value. University of Delaware CPEG 419
Error Correcting Code Legal strings – these are the encoded versions of n bit strings. Illegal strings – no n bit string is encode to these University of Delaware CPEG 419
Error Correcting Code But this code 0 1 1 0 1 0 is received Suppose that this code is 0 1 0 1 0 Then you know an error occurred, and you figure that what was meant to be sent is the code 0 1 0 1 0 (the nearest legal neighbor). University of Delaware CPEG 419
Error Correcting Code But this code 0 1 1 0 1 1 is received Suppose that this code is 0 1 0 1 0 Then you know an error occurred. But you are sure which code was actually sent. University of Delaware CPEG 419
Error Correcting Codes • Linear block and Hamming codes are like the ones just described. • They can be encoded very fast. • Error detection is very fast. • Error correction requires a look-up table. • There are many many more types of error correcting codes. Reed-Solomon are good for burst errors and are used in CDs and cable modems. University of Delaware CPEG 419
Error Control • Mechanisms to detect and correct transmission errors. • Consider 2 types of errors: • Lost frame: frame is sent but never arrives. • Often the first few bytes of frame provide synchronization. If there is an error receiving these bytes, synchronization fails and the frame is not received. • Damaged frame: frame arrives but in error. • If the hardware checks the CRC (typical case), it will not pass the frame to the driver unless the CRC is correct. • Error control: combination of error detection, feedback (ACK or NACK) from receiver, and retransmission by source. • Coupled with flow control feedback. University of Delaware CPEG 419
ARQ • ARQ: automatic repeat request. • Works by creating a reliable data link from an unreliable one. • 3 versions: • Stop-and-wait ARQ. • Go-back-N ARQ. • Selective-reject ARQ. University of Delaware CPEG 419
Stop-and-Wait ARQ • Single outstanding frame at any time. • Simple but inefficient. • Use of timers to trigger retransmission of data or ACKs. • 2 types of errors: • Damaged or lost frame. • Damaged or lost ACK. • Sequence numbers alternate between 0 and 1. • Inefficient for connections with large bandwidth delay product. University of Delaware CPEG 419
Stop-and-Wait ARQ: Example Frame 0 Sender Receiver ACK1 Frame 1 ACK 0 Frame 0 Timeout Frame 0 ACK 1 Timeout Frame 0 B discards duplicate. ACK 1 University of Delaware CPEG 419
Bandwidth Delay Product Which has high/low bandwidth, delay, bandwidth delay product? University of Delaware CPEG 419
Go-Back-N ARQ • Variation of sliding window for error control. • Allows a window’s worth of frames to be in transit at any time. • RR: ack’s receipt of frame. • REJ: negative acknowledgment indicating the frame in error. • Destination discards frame in error plus subsequent frames. University of Delaware CPEG 419
Go-Back-N – single loss frame R rr? S 0 University of Delaware CPEG 419
Go-Back-N – many loss frames S R 0 rr? Either retransmit frame 8 Or send a small packet requesting an RR frame (P bit) Time out University of Delaware CPEG 419
S S R R 0 0 rr1 rr1 rr6 rr6 In this case, a single loss ACK is ok. In this case, a single loss ACK is not that bad. University of Delaware CPEG 419
Go-Back-N ARQ Issues • For k-bit sequence number, maximum window size is (2k-1). • If window size is too large, ACKs may be ambiguous: not clear if ACK is a duplicate ACK (errors occurred). • Example: 3-bit sequence number and 8 -frame window. • Source transmits f0, gets back rr1, then sends f1--f0, and gets back another rr1. ??? University of Delaware CPEG 419
Selective-Reject ARQ • Only frames transmitted are the ones that are NACK’ed (SREJ) or that timeout. • More efficient than Go-Back-N regarding amount of retransmissions. • But, receiver must buffer out-of-order frames. • More restriction on maximum window size; for k-bit sequence #’s, 2k-1 window. University of Delaware CPEG 419
Fragmentation • A packet is broken up into smaller pieces. Each fragment is sent as a frame. • Link layer has an upper bound on the size of frame. E.g., ethernet frames must be smaller than 1500 bytes. ATM must be smaller than 53 bytes, cable modem use 204 bytes. • P1 = (1-Pb)^F. So the smaller the F, the smaller P1. • But the smaller the F, the lower the throughput. The frame has overhead, e.g., the destination address, source address, etc. So a frame of 64 byte Ethernet frame will only contain 38 bytes of data. University of Delaware CPEG 419
Example Data Link Layer Protocol • High-Level Data Link Control (HDLC) • Widely-used (ISO standard). • Single frame format. • Synchronous transmission. University of Delaware CPEG 419
HDLC: Frame Format • Flag: frame delimiters (01111110). • Address field for multipoint links. • 16-bit or 32-bit CRC. • Refer to book (pages 214-221) for more details. flag address flag control data FCS 8 bits 8 ext. 8 or 16 8 variable 16 or 32 University of Delaware CPEG 419
Other DLL Protocols 2 • LLC: Logical Link Control. • Part of the 802 protocol family for LANs. • Link control functions divided between the MAC layer and the LLC layer. • LLC layer operates on top of MAC layer. Dst. MAC addr LLC ctl. Src. MAC addr Dst. LLC addr Src. LLC addr MAC control Data FCS University of Delaware CPEG 419
Other DLL Protocols 3 • SLIP: Serial Line IP • Dial-up protocol. • No error control. • Not standardized. • PPP: Point-to-Point Protocol • Internet standard for dial-up connections. • Provides framing similar to HDLC. University of Delaware CPEG 419
Multiplexing • Sharing a link/channel among multiple source-destination pairs. • Example: high-capacity long-distance trunks (fiber, microwave links) carry multiple connections at the same time. MUX DEMUX . . . . . . University of Delaware CPEG 419
Multiplexing Techniques • 3 basic types: • Frequency-Division Multiplexing (FDM). • Time-Division Multiplexing (TDM). • Statistical Time-Division Multiplexing (STDM). University of Delaware CPEG 419
FDM 1 • High bandwidth medium when compared to signals to be transmitted. • Widely used (e.g., TV, radio). • Various signals carried simultaneously where each one modulated onto different carrier frequency, or channel. • Channels separated by guard bands (unused) to prevent interference. University of Delaware CPEG 419
FDM 2 University of Delaware CPEG 419
TDM 1 • TDM or synchronous TDM. • High data rate medium when compared to signals to be transmitted. University of Delaware CPEG 419
TDM 2 • Time divided into time slots. • Frame consists of cycle of time slots. • In each frame, 1 or more slots assigned to a data source. U1 U2 ... UN 1 2 ... 1 2 ... N N Time frame University of Delaware CPEG 419
TDM 3 • No control info at this level. • Flow and error control? • To be provided on a per-channel basis. • Use DLL protocol such as HDLC. • Examples: SONET (Synchronous Optical Network) for optical fiber. • +’s: simple, fair. • -’s: inefficient. University of Delaware CPEG 419
Statistical TDM 1 • Or asynchronous TDM. • Dynamically allocates time slots on demand. • N input lines in statistical multiplexer, but only k slots on TDM frame, where k < n. • Multiplexer scans input lines collecting data until frame is filled. • Demultiplexer receives frame and distributes data accordingly. University of Delaware CPEG 419
STDM 2 • Data rate on mux’ed line < sum of data rates from all input lines. • Can support more devices than TDM using same link. • Problem: peak periods. • Solution: multiplexers have some buffering capacity to hold excess data. • Tradeoff data rate and buffer size (response time). University of Delaware CPEG 419