Computer Networking Error Control Coding
Computer Networking Error Control Coding. Dr Sandra I. Woolley. An Introduction to Error Control Coding. Data transmission and channel errors Introduction to error control Parity Hamming codes example of a simple linear block code Interleaving and product codes (+ demonstration).

Computer Networking Error Control Coding
E N D
Presentation Transcript
Computer NetworkingError Control Coding Dr Sandra I. Woolley
An Introduction to Error Control Coding • Data transmission and channel errors • Introduction to error control • Parity • Hamming codes • example of a simple linear block code • Interleaving and product codes • (+ demonstration). • IP checksums (Polynomial/Cyclic Redundancy Codes) • We will work through examples in class. http://www.thinkgeek.com/interests/exclusives/7a5c/images/1293/
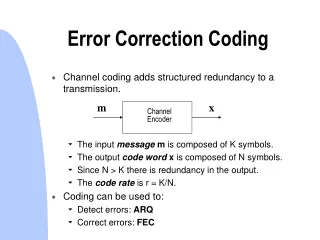
Introduction • Error control coding involves the addition of redundancy to enable error detection and/or correction. • There are two basic approaches to error control • Automatic retransmission request (ARQ) • Forward error correction (FEC) • More generally, when errors are detected data can be resent, concealed or corrected.
Data Transmission Channel errors Data ..01101010.. Compress Encrypt Error control Line code ..01110110.. Encode signal to suit communication channel characteristics Encrypt message for added security Remove redundancy for efficient communication Add systematic redundancy to protect data against channel errors
Designing Error Protection Systems • “Know your enemy” • Understand the channel burst length distribution and gap length distribution, i.e., how large and how frequent are the errors. • Trade-off the correction of data with the addition of redundancy • System cost/delay • Should errors be detected and corrected? • Detect and request retransmission? Detect and conceal? • How important is the data. • Is all data equally important? Should some data elements be protected more than others? • Is accepting bad data as good worse than rejecting good data as bad?
Channel Errors p2 1-p1-p2 p1 Bad Type 2 1-q2 Bad Type 1 Good 1-q1 • Errors can occur singly or in bursts. • Most channel errors can be approximated by simple state models. • The BER (Byte error rate) is a simple measure of channel quality. • In the Good state there are no errors. • Bad Type 1 and Bad Type 2 represent two types of error events; non-burst and burst. • p1 and p2 are the probabilities of starting the errored states. • q1 and q2 are the probabilities of ending the errored states. The modified Gilbert model q1 q2
Channel Errors p2 1-p1-p2 p1 Bad Type 2 1-q2 Bad Type 1 Good 1-q1 • Burst length distributions provide important information about channel error activity. q1 q2 increasing p1 Probability (log scale) decreasing q1 increasing p2 decreasing q2 error length (log scale)
The Simplest Error Detection – Parity Bit • Odd or even parity requires that the sum total of codewords be odd or even, respectively. • So for odd parity there will be an odd number of ones and for even parity there will be an even number of ones. • For example, if we have data bits 0011010 and we want even parity. We need to add a parity bit of 1 to have an even number on ones. So, if we append our parity bit to the end, we have a codeword of 00110101 (where 1 is our even parity bit). Examples from Wikipedia The parity bit is added to the front http://en.wikipedia.org/wiki/Parity_bit
The Hamming (7,4) Code • An example of an (n,k) linear block code. Each codeword contains n bits, k information bits and (n-k) check bits. • The Hamming (7,4) is a nice easy code but it is not very efficient (it has a 75% overhead!). It generates codewords with a ‘Hamming distance’ of 3, i.e., all codewords differ in 3 locations. It can correct one bit in error and detect two. • In the codeword [C]= k1 k2 k3 k4 c1 c2 c3, k1-k4 are information bits and c1-c3 are check bits (the ‘systematic redundancy’). “+” here denotes binary addition (it is the same as XOR). c1=k1+k2+k4 c2=k1+k3+k4 c3=k2+k3+k4 So the data [X] = [0 1 1 0] becomes the codeword [0 1 1 0 (0+1+0) (0+1+0) (1+1+0)] = [0 1 1 0 1 1 0]
The Hamming (7,4) Code If we insert an error at bit 2 [ x ](syndrome) [0 1 1 0 1 1 0] becomes [0 0 1 0 1 1 0] Note c1 and c3 are wrong - these intersect at k2 hence k2 is in error c1=k1+k2+k4 1 k1 k2 0 0 0 k4 1 0 1 c2=k1+k3+k4 k3 c3=k2+k3+k4
The Hamming (7,4) Code If we insert an error at bit 4 [ x ](syndrome) [0 1 1 0 1 1 0] becomes [0 1 1 1 1 1 0] Note c1,c2 and c3 are all wrong hence k4 is in error c1=k1+k2+k4 1 k1 k2 0 1 1 k4 1 0 1 c2=k1+k3+k4 k3 c3=k2+k3+k4
Bi-Directional/Product Codes • Imagine we have 4 x 4 data bitsk11-k14, k21-k24, k31-k34, k41-k44 • Arranging them horizontally we can add error protection in the vertical direction as well. k11 k12 k13 k14 c11 c12 c13 k21 k22 k23 k24 c21 c22 c23 k31 k32 k33 k34 c31 c32 c33 k41 k42 k43 k44 c41 c42 c43 d11 d12 d13 d14 f11 f12 f13 d21 d22 d23 d24 f21 f22 f23 d31 d32 d33 d34 f31 f32 f33
Bi-Directional/Product Codes • In the class we observe animated demonstrations of these codes at work using the product code demonstrator. • First we generate errors using the Modified Gilbert Error Model. The model requires just 4 probability values to describe the errors it generates. • Next the data was interleaved. • Then the data was iteratively corrected vertically and horizontally. • The demonstration shows how, with more sophisticated error control coding, we can significantly increase correction capacity making even severely corrupted data correctable. • The complex and time-consuming nature of this method makes it inappropriate for Internet protocols*. However, robust correction is desirable in storage systems and these methods can be found in the more sophisticated server room RAID-type** storage systems. *but important payload data could be protected in this way **RAID – Redundant Array of Inexpensive Disks
Interleaving Interleaving (systematically reordering) the protected data stream means that errors are distributed, i.e., more correctable. For example, consider the three (7,4) Hamming codewords below in transmission on a channel with a small burst of 3 errored bits (syndrome x xx). k1 k2 k3 k4 c1 c2 c3 k1 k2 k3 k4 c1 c2 c3k1 k2 k3 k4 c1 c2 c3 x xx These 3 bits all fall in one codeword, so would be uncorrectable. But with a three-way interleave:- k1 k1k1 k2 k2k2k3 k3k3k4 k4k4c1 c1c1c2 c2c2c3 c3c3 x xx Assuming the same syndrome of 3 bits in error, if we unscamble the bits (shown below) we can see now there is now just one bit in error in each codeword, and so our data is correctable. k1 k2 k3 k4 c1 c2 c3 k1 k2 k3 k4 c1 c2 c3k1 k2 k3 k4 c1 c2 c3 x xx
More Sophisticated Codes • Sophisticated interleaving strategies are used in most advanced digital recording systems. • CDs use product codes but with Reed-Solomon codes (not Hamming.) They also use interleaving. DVDs and Blu-ray discs also use Reed Solomon block codes. • Reed-Solomon (RS) codes work on groups (e.g., bytes) of inputs. For bytes n<28 (codewords are a maximum of 255 bytes). There is only a very small probability of ‘crypto-errors’, i.e., correcting good bytes by mistake. • RS block codes can correct (n-k)/2 bytes and detect (n-k) bytes. For example, RS(122,106) can correct (122-106)/2 = 8 bytes in error. • Other systems use layers of error correction. If a lower (simpler) layer detects errors, the next (more powerful) layer is inspected. If errors are still detected the final layer is interrogated. This method increases the speed of decoding by only computing check bytes when errors are suspected. DAT tape drives uses 3 layers of error control.
IP Checksum • The IP checksum is an IP header field. It is calculated using the contents of the header. • It was designed for ease of implementation in software (rather than its error-detection ability) because it has needed to be recalculated (IPv4) at every router. • Consider L 16-bit words making up the information bits (IP header). • Checksum,bL, is given by : bL=-x • So that adding the 16-bit words and the checksum (as below) gives 0. (Assessment does not require worked examples. For interest only, this is a tutorial example of how the checksum is calculated with 1’s complement arithmetic is http://www.netfor2.com/checksum.html )
Polynomial/Cyclic Redundancy Check (CRC) Codes b(x) = xn-ki(x) + r(x) n bits n-k bits k bits k information bits(ik-1, ik-2, .... i1,i0) create an information polynomial i(x), of degree k-1. i(x)=ik-1xk-1 + ik-2xk-2 + ... + i1x + i0 i(x) and a generator polynomial, g(x), are used to calculate a codeword polynomial, b(x). Checksum calculation : Divide xn-ki(x) by g(x) to obtain the remainder r(x). xn-ki(x)=g(x).q(x) + r(x) (q(x)= quotient and r(x)=remainder)
Binary Polynomial Division 4 3 quotient dividend = quotient x divisor +remainder 35 ) 1222 dividend 105 1222 = 34 x 35 + 32 divisor 2 17 140 remainder + x = q(x) quotient x3 + x2 x3 + x+ 1 ) x6 + x5 x6 + x4 + x3 dividend divisor x5 + x4 + x3 x5 + x3 + x2 x4 + x2 x4 + x2 + x = r(x) remainder x Division with Decimal Numbers 32 Polynomial Division Note: Degree of r(x) is less than degree of divisor
Generator polynomial: g(x)= x3 + x + 1 Information: (1,1,0,0) i(x) = x3 + x2 Encoding: x3i(x) = x6 + x5 Polynomial Example: k = 4, n–k = 3 x3 + x2 + x 1110 x3 + x+ 1 ) x6 + x5 1011 ) 1100000 x6 + x4 + x3 1011 1110 x5 + x4 + x3 1011 x5 + x3 + x2 1010 x4 + x2 1011 x4 + x2 + x x 010 • Transmitted codeword: • b(x) = x6 + x5 + x • b= (1,1,0,0,0,1,0)
CRC-8: CRC-16: CCITT-16: CCITT-32: Examples of Standard Generator Polynomials CRC = cyclic redundancy check ATM = x8 + x2 + x + 1 = x16 + x15 + x2 + 1 = (x + 1)(x15 + x + 1) IBM Bisync = x16 + x12 + x5 + 1 ISO HDLC, XMODEM, V.41, Bluetooth IEEE 802, DoD, V.42, MPEG-2 = x32 + x26 + x23 +x22 + x16 + x12 + x11 + x10 + x8 + x7 + x5 + x4 + x2 + x+ 1
Thank You Recommended private study exercise : read the error control coding section from Chapter 3 of the recommended text. Use the content of the slides to guide your revision. Methods not referred to in the slides will not be assessed.