Cross-Forest Certificate Enrollment using Certificate Enrollment Web Services
160 likes | 721 Views
Cross-Forest Certificate Enrollment using Certificate Enrollment Web Services. By Kurt Hudson Senior Technical Writer Microsoft. Overview

Cross-Forest Certificate Enrollment using Certificate Enrollment Web Services
E N D
Presentation Transcript
Cross-Forest Certificate Enrollment using Certificate Enrollment Web Services By Kurt Hudson Senior Technical Writer Microsoft Overview This session will discuss services originally added into Windows Server® 2008 R2 and then improved upon in Windows Server® 2012 and Windows® 8 that allow for cross-forest certificate enrollment and renewal. You will learn how to deploy certificates between Active Directory Domain Services (AD DS) forests using Certificate Enrollment Web Services.
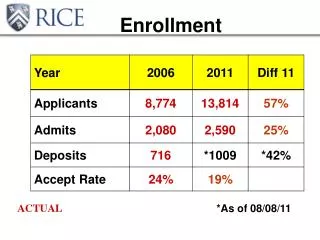
Example Configuration DNS name resolution between forests is required GPO URI CEP1 LDAP RPC/DCOM HTTPS Certificate HTTPS Certificate Templates with CES URI
Cross-Forest Requirements • HTTPS access between the forests • DNS name resolution between the forests • Certificate clients must trust root certification authority (CA). Part of typically setup in home forest, but not in foreign forest. • Enterprise CA • Appropriately configured and issued Certificate Templates • CES user account needs read permission to CA • CES user account need to be member of IIS_USRS • User credentials to obtain a certificate • Certificate could be manually transferred to other forest and used for authentication between forests • Certificate Enrollment Web Service, which also requires SSL cert • Certificate Enrollment Policy Web Service, which also requires SSL cert • URI of the Certificate Enrollment Policy Web Service application – distributed in Group Policy Object (GPO), added to local policy, or manually entered • If using renewal-only mode, then you need to run command Certutil -config "APP1.corp.contoso.com\IssuingCA-APP1" -setreg policy\EditFlags +EDITF_ENABLERENEWONBEHALFOF on CA
Key-based Renewal Additional Requirements • Windows Server 2012 • Certification authority • Certificate Enrollment Policy Web Service • Certificate Enrollment Web Service • Windows 8 or Windows Server 2012 certificate clients • Certificate Enrollment Policy Web Service configured for key-based renewal • Certificate templates issued that are configured to allow key-based renewal
Specific Certificate Template Requirements Key-Based Renewal
Certificate Enrollment Policy Web Service Installation • Install-AdcsEnrollmentPolicyWebService • -AuthenticationType<type> • -KeyBasedRenewal • -SSLCertThumbprint<thumbprint> • (dir -dnsname<dnscomputername>).Thumbprint • In key-based renewal mode, the policy server URIs will show only the key-based renewal enabled templates The Windows PowerShell cmdlet must be used when you want to deploy multiple enrollment policy virtual applications on the same server. AD CS Deployment Cmdlets in Windows PowerShell
Certificate Enrollment Web Service Installation • Install-AdcsEnrollmentWebService • -CAConfig“<config>" • -SSLCertThumbprint<thumbprint> • (dir-dnsname<dnscomputername>).Thumbprint • -AuthenticationType<type> (Username, Certificate, Kerberos) • -RenewalOnly(only for renewal only mode) • -AllowKeyBasedRenewal (only for key-based renewal) The Windows PowerShell cmdlet must be used when you want to deploy multiple enrollment policy virtual applications on the same server. AD CS Deployment Cmdlets in Windows PowerShell
Testing Key-Based Renewal From the certificate client run these command from Windows PowerShell: • Cd Cert:\LocalMachine\My • Dir| format-list • certutil -f –policyserver* -policycachedelete • certreq -machine -q -enroll -cert <thumbprint> renew • Dir| format-list • Is there a new thumbprint? If yes, success!
Registry Locations for Policy Servers on the Client • HKEY_LOCAL_MACHINE\SOFTWARE • \Policies\Microsoft\Crytography\PolicyServers for enrollment policies shown as Configured by your administrator • \Microsoft\Crytography\PolicyServers for enrollment policies listed as Configured by you
CA invalid or incorrect Add root CA to Trusted Roots Troubleshooting 1/6
Cannot see certificate templates from client Things to check Troubleshooting 2/6 • Template is issued • Connectivity • https • DNS can resolve URI • Certificate type: are you requesting the right type? • User • Service • Computer • Template Settings • Read permissions • Enroll permissions • Ensure that you are not trying key-based renewal URI expecting a template that is not configured for key-based renewal • Compatibility tab (more later)
Validate Server Error: This ID conflicts with an existing ID Resolution: Change Application Settings ID of one of the conflicting virtual applications Troubleshooting 3/6
Troubleshooting 4/6 • Issuing CA is running Windows Server 2012 • Issuing CA name has spaces • Problem: Creates a Certificate Enrollment Web Services URL with spaces instead of %20 (see error below) • Detailed workaround Implementing Certificate Enrollment Web Services in Windows Server® 2012 that uses an Issuing CA with spaces in the name
Troubleshooting 5/6 • The Compatibilities tab is supposed to make life easier for the administrator – it disables settings that don’t work for specified CAs or clients. • One issue is that when Windows Server 2012 CA is selected, then Windows 7 and Windows Server 2008 R2 clients don’t see the template. Resolution, set CA to Windows Server 2008 R2 in order to service those clients.
Troubleshooting 6/6 • When you make changes to your configuration • Restart IIS (iireset) • Certificate Enrollment Web Services server • Certificate Enrollment Policy Services server • Delete client policy enrollment server cache • Certutil -f -policyserver * -policycache delete • May have to clear registry locations on client • May have to update URIs in Group Policy • Ensure that your CRL is up-to-date certutil -crl
Additional Information Links • Certificate Enrollment Web Services in Active Directory Certificate Services • AskDS Blog: Certificate Enrollment Web Services • Test Lab Guide: Deploying an AD CS Two-Tier PKI Hierarchy • Test Lab Guide: Demonstrating Certificate Key-Based Renewal • Test Lab Guide Mini-Module: Cross-Forest Certificate Enrollment using Certificate Enrollment Web Services