BUFFER OVERFLOW
BUFFER OVERFLOW. Tsega Gebreyonas Sunny Choi CS 265 November 18, 2003. Overview. The Basics Attacks exploiting buffer overflow Prevention and countermeasures Recent Case Studies Conclusion and Observations. Why Study Buffer Overflow?. Vulnerability since the 1970s

BUFFER OVERFLOW
E N D
Presentation Transcript
BUFFER OVERFLOW Tsega Gebreyonas Sunny Choi CS 265 November 18, 2003 Buffer overflow
Overview • The Basics • Attacks exploiting buffer overflow • Prevention and countermeasures • Recent Case Studies • Conclusion and Observations Buffer overflow
Why Study Buffer Overflow? • Vulnerability since the 1970s • “Computer vulnerability of the decade” 1 • Cause of at least half of all vulnerabilities found in Operating Systems • Code Red worm, 2001 • Blaster worm, 2003 Buffer overflow
Basics of Buffer Overflow • A “stuffing” of more data into a buffer than the allocated size. • Two types: • corrupt the execution stack by writing past the end of an array (aka. smashing the stack/ stack overflow) • corrupt the heap (heap overflow) Buffer overflow
How Does Buffer Overflow Happen? • Careless use of buffer without bounds check • No automatic bounds checking for buffer in C/C++ programming languages • Unsafe library function calls • Off-by-one errors • Old code used for new purposes • Formatting and logic errors Buffer overflow
Possible causes of buffer overflow • Un-terminated strings can produce overflow • Segmentation fault, crash Buffer overflow
Process Memory Organization Lower Memory addresses Text Data Heap Stack Higher Memory addresses Process Memory Regions Buffer overflow
Text Data • Text region • Fixed by the program • Includes code (instructions) • Read-only • Data region • Contains initialized and un-initialized data • Static variables are stored here. Heap Stack Buffer overflow
The Stack Contains: • local variables for functions • Return address and local stack pointer • Used to • Dynamically allocate the local variables used in functions. • Pass parameters to functions. • Return values from functions. Buffer overflow
Text Data • Stack pointer (SP) points to the top of the stack. • The bottom of the stack is at a fixed address. • Consists of logical stack frames that are pushed when calling a function and popped when returning. • Frame pointer (FP) points to a fixed location within a frame. Heap Stack Buffer overflow
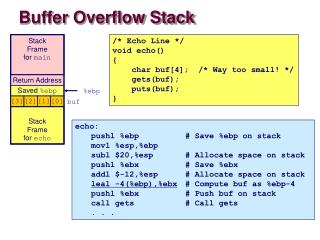
Example stack.c void function(int a, int b, int c) { char buffer1[5]; char buffer2[10]; } void main() { function(1,2,3); } Buffer overflow
Example cont.. (1) • After ‘gcc –S –o stack.s stack.c’ • See notes below • Call function is translated to pushl $3 pushl $2 pushl $1 call function Buffer overflow
Example cont.. (2) • Its pushes the 3 arguments backwards into the stack. • The instruction ‘call’ will push the EIP onto the stack. • Procedure prolog push %ebp mov %esp, %ebp sub $20, %esp Buffer overflow
Example cont.. (3) • pushes the FP onto the stack. • Copies the current SP onto EBP, make it the new FP. • Allocates space for the local variables by subtracting their size from SP. • Memory can only be addressed in multiples of the word size. • 5 byte buffer take 8 bytes (2 words). • 10 byte buffer take 12 bytes (3 words). • SP is subtracted by 20 Buffer overflow
buffer2 buffer1 SFP EBP ret a b c Stack Buffer overflow
Principle of Stack Overflows • When a program is run: • the next instruction address, ret, is stored on the stack. • modifying this value in the stack forces the EIP to get new value. So when the function returns, the program may execute the code (e.g. some shellcode) at this new address specified by overflowing the stack. Buffer overflow
Principle of Stack Overflows cont.. • How to find where the ret is, to overwrite? • methods of improving chances shellcode (or some code to execute) NOPs repeated return address buffer overflow with this – as long as ret is overflowed with any part of this string, shellcode will be executed Buffer overflow
Stack Overflow Example # include <stdio.h> void show_string(char * str2) { char buffer[5]; strcpy(buffer, str2); printf(“Your string is : %s\n”, buffer); } main () { char str [10]; gets(str1); show_string(str1); exist (0); } Buffer overflow
The Heap • Definition: contains memory that is dynamically allocated by the application • Buffer overflow can happen here • Although more difficult to achieve than stack overflows Buffer overflow
User Exploits of Heap Overflow • Overwrite: - filenames - passwords - … Manipulate: - pointers - function pointers Buffer overflow
Principle of Heap Overflows • Requires some preconditions to be met in the source code of the vulnerable binary: • a buffer must be declared (or defined) first. • a pointer must be declared. Example: ... static char buf[BUFSIZE]; static char *ptr_to_something; ... Buffer overflow
/root/.rhosts sometmpfile.tmp POINTER POINTER BUFFER BUFFER before overflow after overflow Buffer overflow
Heap Overflow Example #define BUFSIZE 16 #define OVERSIZE 8 int main() { u_long diff; char *buf1 = (char *)malloc(BUFSIZE), char *buf2 = (char *)malloc(BUFSIZE); diff = (u_long)buf2 - (u_long)buf1; printf("buf1 = %p, buf2 = %p, diff = 0x%x bytes\n", buf1, buf2, diff); memset(buf2, 'A', BUFSIZE-1), buf2[BUFSIZE-1] = '\0'; printf("before overflow: buf2 = %s\n", buf2); memset(buf1, 'B', (u_int)(diff + OVERSIZE)); printf("after overflow: buf2 = %s\n", buf2); return 0; } Buffer overflow
Heap Overflow Example Results [root /w00w00/heap/examples/basic]# ./heap1 buf1 = 0x804e000, buf2 = 0x804eff0, diff = 0xff0 bytes before overflow: buf2 = AAAAAAAAAAAAAAA after overflow: buf2 = BBBBBBBBAAAAAAA Buffer overflow
Why Not “Fix” Buffer Overflow? • 1000s of lines of legacy code running as root • To change and check cases is expensive • Trade off : security Vs “time to market” • Attitude : “If works …” no one cares • Traditional approach: get it to work first, then fix it. • Security is not easy to verify unless someone find issue how do you figure what will be fault in the future • Lifecycle of buffer overflow: • Vulnerability exploited • Patch that program-specific attack Buffer overflow
Buffer Overflow Countermeasures • Write secure code (Golden Rule) • Terminate strings and pass size of buffers to functions (e.g. use strncopy instead of strcopy etc) • Careful Use of C/C++ Library Functions • Don’t trust inputs (validate all inputs) • Stack execute invalidate • Dynamic run-time checks Buffer overflow
Countermeasures cont.. • Programming Languages • Automatically resize arrays (e.g. Perl, Java) • Detect and prevent buffer overflows. (e.g. Ada95, Java) • Use “C” only when speed/low level access is critical (almost all OSs are written in C nowadays) • Use advanced compiler tools such StackShield and StackGuard • Same principle for heap overflows Whenever a function is called, a "canary" value is pushed on the stack. This value ‘protects’ the return address. buffer1 SFP canary ret Some un-guessable value a StackGuard Buffer overflow
Case Studies • Code Red (I/II) • Blaster • infected more than one million hosts over its first 24 hours of life, according to one estimate Buffer overflow
Code Red I/II, 2001 - Effects • July 19th: spread to 250,000 computers in only 9 hours • Between the two worms, about 800,000 machines infected • an estimated $2.5 billion in damages • defaced web sites • a failed attempt at a denial-of-service attack on www.whitehouse.gov. Buffer overflow
How Did Code Red Work? • Exploited a buffer overflow vulnerability in Microsoft Internet Information Servers • attempts to connect to TCP port 80 on a randomly chosen host • the attacking host sends a HTTP GET request to the victim, attempting to exploit the buffer overflow in the Indexing Service • If the exploit is successful, the worm begins executing on the victim host. • The Code Red II worm exploited the very same vulnerability, except it installed a back door designed to make your entire hard drive available to attackers over the Internet. Buffer overflow
Blaster, 2003 • exploited a vulnerability in Microsoft's DCOM RPC interface • Execution: • Infect with worm • Add the executable to the registry so that it runs at windows startup • Generates IP address and tries to infect another computer with that IP address -60% random • Send data on TCP port 135 to exploit DCOM RPC vulnerability • Impact: • execute arbitrary code with Local System privileges • denial-of-service condition. Buffer overflow
Microsoft Manhunt • November 5, 2003, Microsoft: • announces $250,000 reward in a worldwide manhunt for the creator of Blaster. • Earmarks $4.5 million for bounties in future attacks. Buffer overflow
Conclusions • Buffer overflows exist and will continue to pose a real threat • Tools can help (not solution) • Best protection: • be a defensive and educated programmer; write robust code in the first place Buffer overflow
References • Aleph One, "Smashing The Stack For Fun And Profit," Phrack, Vol 7, Issue 49, File 14 of 16 • Howard M., LeBlanc D.,Writing Secure code, second edition, Microsoft Corporation, 2003 • Mark G. Graff, Kenneth R. Van Wyk, Secure Coding, O'Reilly & Associates, July 2003 • Matt Conover, and WSD, "w00w00 on Heap Overflows", January 1999, www.w00w00.org/ files/ articles/heaptut.txt • Paul Festa, “Study says "buffer overflow" is most common security bug,” CNET News, November 23, 1999, http://news.com.com/2100-1001-233483.html?legacy=cnet • Pierre-Alain Fayolle, “A Buffer Overflow Study Attacks and Defenses,” 2002, http://g0tr00t.mson.org/docs/nix/bof.html • Sandeep Grover, “Buffer Overflow Attacks and Their Countermeasures,” Linux Journal, March 2003 Buffer overflow