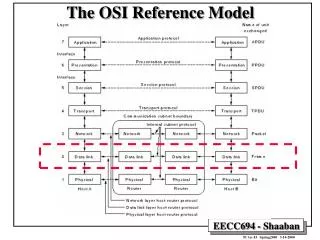
The OSI Reference Model
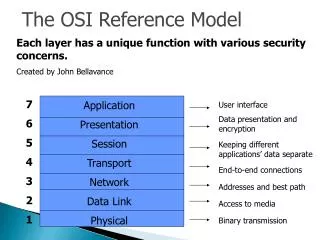
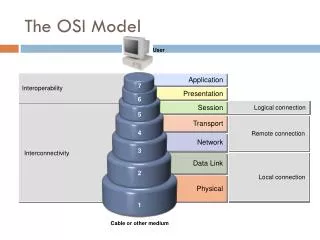
The OSI Reference Model. Key concepts: Layers Communications between two adjacent layers Encapsulation Multiplexing and demultiplexing Tunneling. Source: http://bzupages.net/f8/osi-model-7-a-110/. Source: http://www.petri.co.il/osi_concepts.htm.

The OSI Reference Model
E N D
Presentation Transcript
The OSI Reference Model Key concepts: Layers Communications between two adjacent layers Encapsulation Multiplexing and demultiplexing Tunneling
Source: http://bzupages.net/f8/osi-model-7-a-110/ Network Security
Source: http://www.petri.co.il/osi_concepts.htm Network Security
Source: http://www.novell.com/info/primer/prim05.html Network Security
Multiplexing and Demultiplexing • Multiplexing: Multiple types of data streams are delivered on a shared channel. • Can occur at any layer • Example: Application packets of different types (e.g., HTTP, SMTP, etc.) are encapsulated into TCP packets at the transport layer. - Another example: TCP and UDP packets are multiplexed into IP packets. Network Security
Multiplexing and Demultiplexing • Demultiplexing: The reverse operation of multiplexing. Different types of data streams delivered on a shared channel are split into the original types of packets. • Two operations: • Given a packet, check the type of the payload. • Remove the header and send the payload to the appropriate protocol one level above. Network Security
Source: http://en.wikipedia.org/wiki/TCP_IP Network Security
Encapsulation vs Tunneling • Encapsulation: A packet is encapsulated into the payload of a lower layer packet; a new header is added at the lower layer. • Source: http://en.wikipedia.org/wiki/TCP_IP Network Security
Encapsulation vs Tunneling • Tunneling: A packet (the payload protocol) is encapsulated into another protocol at the same or higher layer (the delivery protocol). • Example: A IP packet is encapsulated into a IPsec packet. • Tunneling can be used to circumvent a firewall policy (http://en.wikipedia.org/wiki/Tunneling_protocol) • Example: HTTP can be used to tunnel a protocol that would otherwise be blocked by the firewall. Network Security