A Step Back Reflections on P2P
A Step Back Reflections on P2P. Boris Capitanu Ellick Chan 10/12/2004. 2 P2P or Not 2 P2P?. Mema Roussopoulos Mary Baker David S. H. Rosenthal TJ Giuli Petros Maniatis Jeff Mogul. Ideal P2P properties. Self Organizing P2P routing Discovery Symmetric communication

A Step Back Reflections on P2P
E N D
Presentation Transcript
A Step BackReflections on P2P Boris Capitanu Ellick Chan 10/12/2004
2 P2P or Not 2 P2P? Mema Roussopoulos Mary Baker David S. H. Rosenthal TJ Giuli Petros Maniatis Jeff Mogul
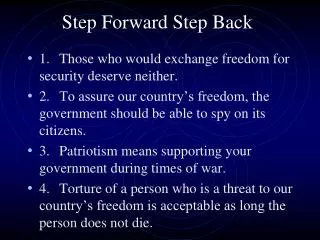
Ideal P2P properties • Self Organizing • P2P routing • Discovery • Symmetric communication • Peers are approximately equal • Decentralized control • No single point of failure
Constraints • Budget • Resource relevance to participants • Trust • Rate of system change • Criticality • Accountability • Fault tolerance
Candidate problems • Routing Problems • Internet Routing (RON) • Ad hoc Routing in Disaster Recovery • Metropolitan-area Cell Phone Forwarding • Backup • Internet Backup • Corporate Backup • Distributed Monitoring
Candidate problems • Data Sharing • File sharing • Censorship Resistance • Data Dissemination • Usenet • Non-critical Content Distribution • Critical Flash Crowds • Auditing • Digital Preservation • Distributed Time Stamping
P2P models Gnutella Usenet Images from http://www.cybergeography.org/atlas/more_topology.html
2 P2P or not P2P Budget Relevance Trust
Budget Low Effect High • Lowest possible cost per peer, rather than lowest global cost • Bit Torrent, Gnutella, Freenet, etc. • SETI@home • Dictates how many peers join • Decides if P2P is viable for problem • Worries less about performance criticality • Favors centralized approaches, P2P irrelevant • Clusters, High performance computing
Relevance Low Effect High • Personal data • Private data • Internet backup • Corporate backup • Web caching • Relevance of resources encourages peers to join • “When resource relevance is high, cooperation in a P2P solution evolves naturally” • File sharing • Freenet • Content distribution • Internet routing • Bit Torrent • Gnutella • Kazaa
Trust Low Effect High • Encryption • Anonymity • Freenet • Oceanstore • Ivy • Timestamping • MojoNation • Mutual trust • Risks • Gnutella • Napster • Overlays • File sharing • Usenet
Rate of Change Low Effect High • Tangler • Freenet • LOCKSS • Time stamping • Content distribution • Usenet • Flash crowds • Churn • Timeliness • Consistency • Internet routing • Online net monitoring
Criticality Low Effect High • Usenet • Content distribution • Offline net study • File sharing • Centralized control • Accountability • Fault tolerance • Ad hoc disaster recovery • Flash crowds • Internet monitoring • Routing
2 P2P or not P2P Budget Relevance Trust
Conclusion • Framework for analyzing P2P applications • Captures constraints and app requirements • Limited budget is motivating factor • Problems with low relevance are inappropriate for P2P
Critique • Strengths • Quantifies application requirements and suitable use cases • Generically describes suitability of classes of P2P apps • Weaknesses • Incomplete view of requirements • Fuzzy requirements not accounted for
Service Capacity of Peer to Peer Networks Xianying Yang Gustavo de Veciana
Service Capacity • # of peers available to serve a document • Throughput of P2P system • Average delay • Rate of dissemination • What factors govern the effectiveness of a system to scale?
Research problem • Analyze behavior of P2P systems • Describe and model capacity behavior • Transient regime • Steady state • Analyze conditions • Does system scale as modeled? • Are delays and throughput bounded?
Throughput • Transient • Steady state
Service capacity model • Steady state • Impact of peer join/departure • Performance • Factors • Peer selection • Data management • Multipart downloads • Size of parts • Admission and scheduling • Traffic
Analysis • 2 States • Transient (branching process model) • Steady state • Deterministic • Branching process • Markov chain
Deterministic Time 0 Rate 1 • N-1 users want a doc • N=2k • S bits per request • S(n-1) bits total • Time interval at s/b seconds • Exponential growth • Ability to serve large bursts • Average delays scales by lg(n) 0 Count 1
Deterministic Time 1 Rate 1 • N-1 users want a doc • N=2k • S bits per request • S(n-1) bits total • Time interval at s/b seconds • Exponential growth • Ability to serve large bursts • Average delays scales by lg(n) 0 Count 2 1
Deterministic Time 2 Rate 2 • N-1 users want a doc • N=2k • S bits per request • S(n-1) bits total • Time interval at s/b seconds • Exponential growth • Ability to serve large bursts • Average delays scales by lg(n) 0 Count 6 1 2 2
Deterministic Time 3 Rate 4 • N-1 users want a doc • N=2k • S bits per request • S(n-1) bits total • Time interval at s/b seconds • Exponential growth • Ability to serve large bursts • Average delays scales by lg(n) 0 Count 8 1 2 3 3 2 3 3
Multipart • M identical size chunks • Service completions at s/mb=m seconds • Optimization, peers favor others with no chunks • At time k, system is partitioned into k sets Ai,i=1…k. • |Ai|=2k-i • Ai corresponds to peers who have only received the ith chunk A4 A2 A3 A1 Time slot k
Multipart • M identical size chunks • Service completions at s/mb=m seconds • Optimization, peers favor others with no chunks • At time k, system is partitioned into k sets Ai,i=1…k. • |Ai|=2k-i • Ai corresponds to peers who have only received the ith chunk A4 A2 A3 Time slot k
Peer groups S A1 A2 A3 A4 t0 t1 t2 … tk
Multipart • Delay is in effect reduced by a factor of m • Large values of m better, but require more network overhead • Congestion, bandwidth bottleneck ignored in this model
Branching Process Model • Let Nd(t)=#peers serving document d at time t. • Ti is a random variable, transfer time • E[T]==1/ • Age dependent branching process model, v=2
Branching Process Model • are growth characteristics • If T is exponentially distributed, • If T is deterministic, ln2 • Exponential distribution increases growth exponent
is inversely proportional to v Large fanout decreases growth exponent Intuition: limit number of downloads at each peer Effect of v on Growth Theorem II
Peers exit system with probability 1-upon completion If v<1, system becomes extinct When peers exit, allowing multiple upload ensures document availability and system growth Peer Churn System increases slowly with increasing v
Effect of m • Allowing multipart downloads increases performance by factor m • Growth rate increased by factor m • Delay factor is reduced by 1/m • Assumes peers are not simultaneously sharing multiple parts of files
Summary Multipart Branching • Time interval for transfer • N=2k • Delays bounded by log n • Exponential growth Deterministic • Time interval m • Delays bounded by (m)log n • Space partitioned into sets • More chunks is faster • Network overhead is high • Time interval is a random variable • Delays bounded by log • Parameters determine operation • Accounts for congestion, churn
Markov Chain • Distant past irrelevant with knowledge of recent past • Sequence of random variables, X1…Xn • Transition matrix • Eigenvectors determine stable state conditions
Markov Chain Sunny Rainy P(Rainy|Sunny) Sunny Rainy P(Rainy|Rainy) P(Sunny|Rainy) P(Sunny|Sunny) Weather, day 0 Weather, day 1 Weather, day 2 Weather, day n
Markov Model • Poisson process r: • State • x=#of peers requesting • y= #peers hosting • Multipart files • Partial peers contribute at rate • Total rate: i Q S0 Si= (*1) Exponentially distributed Full service rate: Exit rate:
Performance Seeds/downloaders • Seeds/downloaders • is upload ratio of downloader to seed • System with high leverages capacity • Marginal change of system performance low when offered load is high
Bit Torrent • Multipart d/l • Chunk size 1 mb • Credit system • Updates every 5 min • 150-200 file insertions Service capacity Throughput Delay
Conclusions • Credit system, growth are diametric • Offered load linearly scales with number of peers • Large multi-part files spread better • Peer churn reduces throughput to constant • Delays decrease with offered load