IP Spoofing and DDoS: Understanding the Problem and Proposed Solutions
320 likes | 338 Views
This article discusses the issue of IP spoofing and distributed denial of service attacks, along with proposed solutions. It explores the challenges, possible approaches, and detection methods.

IP Spoofing and DDoS: Understanding the Problem and Proposed Solutions
E N D
Presentation Transcript
Advanced Topics in Network Security: IP Spoofing and DDoSCS 236On-Line MS ProgramNetworks and Systems Security Peter Reiher
Outline • IP spoofing • The problem • Proposed solutions • Distributed denial of service • The problem • Proposed solutions
Destination address Source address The Problem of IP Spoofing IP header IP payload Now we’ll capture the desperate criminal! So has someone hacked Granny’s machine? Who sent you the fatal packet? No, someone spoofed Granny’s IP address! Now we’re getting somewhere!
183.11.46.194 183.11.46.194 What Really Happened 183.11.46.194 76.128.4.33 The dirty liar!
What Is IP Spoofing? • Existing Internet protocols and infrastructure allow forgery of some IP packet header fields • In particular, the source address field can often be forged • If packet causes trouble, can’t determine its true source • Particularly important for distributed denial of service attacks • But relevant for other situations
What Is Spoofing Used For? • If attacker forges source address, probably won’t see the response • So spoofing only useful when attacker doesn’t care about response • Usually denial of service attacks • This point is not universally true • If attacker can sniff the path . . .
IP Spoofing and Reflector Attacks • Some network sites accept remote requests and provide answers (or take actions) • E.g., DNS servers, broadcast addresses • Responses go to whoever’s in the source address of the request • If response is a lot bigger than the request, the attacker can cause more traffic at victim than attacker must send out
Types of Spoofing • General spoofing • Attacker chooses a random IP address for source address • Subnet spoofing • Attacker chooses an address from the subnet his real machine is on • With suitable sniffing, can see responses • Harder for some types of filtering
How Much of a Problem Is Spoofing? • The Spoofing Project suggests 16-20% of Internet is spoofable • Because of ingress filtering • Methodology based on limited number of volunteers running their code • Arguably the folks most likely to deploy ingress filtering • Even if they’re right, 20% is a lot
Combating Spoofing • Basic approaches: • Authenticate address • Prevent delivery of packets with spoofed addresses • Trace packets with spoofed addresses to their true source • Deduce bogosity from other packet header information • Deduce bogosity of entire data streams with shared IP addresses
Authenticate Address • Probably requires cryptography • Can be done with IPSec • Incurs cryptographic costs • Only feasible when crypto authentication is feasible • Could we afford to do this for all packets?
Pushing Authentication Out • Destination node can’t afford to check authentication • Since, usually, spoofing done at high volumes • Could we push authentication out into the network? • Enlist core routers to check authentication? • Sounds crazy • They’re already busy • But maybe they can do it only when needed? • Or maybe it can be built into fast hardware?
Challenges for In-Network Address Authentication • Large scale authentication problem • Key management, etc. • Crypto costs • Partial deployment • Costs of updates?
Packet Passports • A simplification of the approach • Destination sends secret stamps to sources it likes • Only packets with the right stamp get delivered • For their source address • Spoofers don’t know the stamp • So their packets get dropped • Maybe far out in the network
Issues for Stamping Approaches • Are stamps related to packet contents? • If not, can attackers “steal” a stamp? • How often do you change stamps? • How to you issue stamps to legitimate nodes? • Where do you put stamps? • How do you check them fast enough?
Detect Spoofed Addresses • Recognize that address is spoofed • Usually based on information about: • Network topology • Addresses • Simple version is ingress filtering • More sophisticated methods are possible
95.113.27.12 56.29.138.2 Ingress Filtering Example My network shouldn’t be creating packets with this source address 128.171.192.*
Spoofing Detection Approaches I A B J C H D G F E
Potential Problems With Approaches Requiring Infrastructure Support • Issues of speed and cost • Issues of trustworthiness • Issues of deployment • Why will it be deployed at all? • How will it work partially deployed?
SAVE • At each router, build table of proper “incoming” interface • For source addresses, which interface should packets arrive? • Kind of a generalization of ingress filtering • But how to get the information? • Leverage routing table
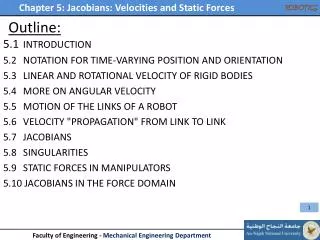
B A SAVE Protocol C RE 4 5 1 10 SAVE builds incoming table at each router through: Generating SAVE updates Processing and forwarding SAVE updates Final result is that all routers build proper tables 2 RC 6 E A RA 3 RD 11 FORWARDING INTERFACE RB ADDRESS D 7 8 C 2 B 3 INCOMING INTERFACE 9 ADDRESS D 3 A 7 3 E INCOMING TABLE FORWARDING TABLE B
SAVE Update Generation Each SAVE router is assigned a source address space (SAS) Range of IP addresses that use this router as an exit router for some set of destinations Independent of the underlying routing protocol A periodic SAVE update is generated for every entry in the forwarding table and sent to the next hop Forwarding table change invokes the generation oftriggered SAVE update for the changed entry
Did SAVE Work? • Yes, just fine • In full deployment . . . • In partial deployment, update splitting is extremely challenging • Since non-deployers won’t split your updates • Thus, of academic interest
Packet Tracing • Figure out where the packet really came from • Generally only feasible if there is a continuing stream of packets • Usually for DDoS • Challenges when there are multiple sources of spoofed addresses • For many purposes, the ultimate question is – so what?
Using Other Packet Header Info • Packets from a particular source IP address have stereotypical header info • E.g., for given destination, TTL probably is fairly steady • Look for implausible info in such fields • Could help against really random spoofing • Attacker can probably deduce many plausible values • There aren’t that many possible values
30 27 28 29 30 31 32 32 A 27 A 27 B 27 D 26 E 58 F 27 G 26 H 30 I 30 Using TTL To Detect Spoofing I A B J C H D G F E
Deducing Spoofing From Data Stream Information • Streams of packets are expected to have certain behaviors • Especially TCP • Observe streams for proper behavior • Maybe even fiddle with them a little to see what happens • Obvious example: • Drop some packets from TCP stream with suspect address • Do they get retransmitted?
How Can We Deduce Spoofing? AS Packets from 131.179.192.* have been coming in on one interface Now packets from those addresses show up on another Route change or spoofing? Drop a few and see what happens
What If It’s Good Traffic? AS ✔ ✔ TCP to the rescue! Receiver tells sender to retransmit “lost” packets Since all dropped packets retransmitted, they weren’t spoofed What about that other interface?
What If It’s Bad Traffic? AS TCP to the rescue! Receiver tells sender to retransmit “lost” packets But “sender” never heard of those packets! So it doesn’t retransmit So AS knows this interface is wrong
Clouseau • A system designed to do this • Allows router to independently detect spoofing • Doesn’t require crypto • No PKI! • Must deal with attempted deception • How could you deceive Clouseau? • How would Clouseau detect it?
Open Questions On Spoofing • Are there entirely different families of approaches? • How can you actually build tables for detection approaches? • Can detection approaches work in practical deployments? • Are crypto approaches actually feasible? • How do you evaluate proposed systems?