Agenda
720 likes | 1.05k Views
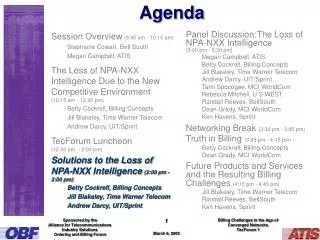
Agenda Introduction Positioning of PAN/LAN/WAN Wireless Local Area Network (WLAN) and 802.11 Personal Area Networks (PAN) and Bluetooth Future Wireless Technologies IBM Mobile Wireless Technology Penetration of Technology Opportunities for Connection WAN LAN PAN Technology Positioning

Agenda
E N D
Presentation Transcript
Agenda • Introduction • Positioning of PAN/LAN/WAN • Wireless Local Area Network (WLAN) and 802.11 • Personal Area Networks (PAN) and Bluetooth • Future Wireless Technologies • IBM Mobile Wireless Technology
WAN LAN PAN Technology Positioning Geography Nomenclature Wireless Technology Off-campus (Open areas) Cellular (Kilometers) 802.11b (10’s-100’s of meters) On-campus (Office, School, Airport, Hotel) Person Space (office, briefcase, person) Bluetooth (meters to 10’s of meters)
WLAN Augment Wired LANs 1. Wireless Local Area Networks (WLAN) 2. WLAN Components 3. IEEE 802.11 ? 4. Mixing Vendor Equipment 5. Wireless and wired LAN interoperability 6. WLAN Range 7. Access Points 8. Roaming 9. Using a WLAN to Interconnect two LANs 10. WLAN Scenarios 11. Security 12. Technology Comparisons Infrastructure LAN Access Point Peer-to-peer collaboration Ad hoc
Wireless Local Area Networks (WLAN) • Two or more computers connected wirelessly using standard network protocols • The current buzzword however generally refers to wireless LANs (WLAN). • Controlled by a standards committee (IEEE 802.11) • WLAN solutions for: • Business • Education • Applications where network wiring is impossible • Warehousing • Point-of-sale handheld equipment.
WLAN Topologies There are two kinds of wireless networks: 1) An ad-hoc, or peer-to-peer wireless networks • Each computer communicates directly with each other to: send files, share printers, work collaboratively • They may not be able to access wired LAN resources, unless one of the computers acts as a bridge to the wired LAN using special software. 2)Infrastructure wireless networks (access points, hardware or software) • Access point acts like a hub, providing connectivity for the wireless computers. It can connect (or "bridge") the wireless LAN to a wired LAN, allowing wireless computer access to LAN resources, such as file servers or the Internet.
Infrastructure Dedicated hardware access points (HAP) Wired Client Wired Network Wireless Clients Access Point Server Wireless Network
Infrastructure Software Access Points which run on a computer equipped with a wireless network interface card as used in an ad-hoc or peer-to-peer wireless network Wired Client Wireless Client Software Access Point Wired Network Wireless Network Server Wireless Client
IEEE 802.11 Wireless networking hardware requires the use of underlying technology that deals with radio frequencies as well as data transmission. The most widely used standard is 802.11 produced by the Institute of Electrical and Electronic Engineers (IEEE). This is a standard defining all aspects of Radio Frequency Wireless networking. 802.11 was ratified in 1997 at speeds of 1- 2 Mb/s The 802.11b extension runs at 1, 2, 5.5 and 11 Mb/s
IEEE 802.11 • 802.11a is a proposed spec running in the 5GHz IBM band with speeds of 54Mb/s scheduled for 2002 • But range is less (more like 10m) • The 802.15 Coexistence Task Group is addressing interoperability between low-power wireless devices (Bluetooth) and 802.11b. Completion is scheduled for 2001 • IBM is a member of 802.11 and 802.15
Mixing vendor equipment • Because most wireless networking hardware vendors support the 802.11 standard they can inter-operate. • Verification is recommended because there are two different modulation techniques: • Frequency Hopping Spread Spectrum (FHSS) • Direct Sequence Spread Spectrum (DSSS) • They are not interoperable. • When purchasing wireless networking hardware from separate vendors be sure to obtain guarantees from the vendors that the hardware will inter-operate and follows the standards.
Mixing vendor equipment • Within a short time all new wireless cards, like Ethernet cards, will become inexpensive, ubiquitous and totally interoperable. • The latest version of the standard (802.11b) defines 11mbps with support for the older standard of 1mbps and 2mbps speeds. This provides compatibility with different or older equipment. • Note that this new standard covers DS-type Networks, not FH types. • At this point mixing Access Points is not recommended, unless it has the Wi-Fi(Wireless Fidelity) logo from WECA (Wireless Ethernet Compatibility Association)
Wireless and Wired LAN Interoperability The Access Point acts as a “Bridge” between the wireless and wired networks Hardware access points are available with various types of network interfaces, such as Ethernet or Token Ring Software access point may also be used
WLAN Range Each access point has a finite range The distance varies depending upon the environment; indoor, outdoor, building construction. Operating at the limits of the range reduces performance. Typical indoor ranges are 20-50 meters, outdoor are 100-200 meters Longer ranges are possible; performance will degrade with distance. Using multiple Access Points will extend the range
Access Points Inexpensive access points have a recommended limit of 10 More expensive access points support up to 100 wireless connections. Using more computers than recommended will degrade performance and reliability Multiple access points can be connected to a wired LAN, or to a second WLAN. Functions vary by manufacturer
Roaming • A wireless computer can "roam" from one access point to another • Completely transparent to the user • Some access point configurations require security authentication when swapping access points, usually in the form of a password dialog box. • Access points are required to have overlapping wireless areas to achieve this.
Using a WLAN to interconnect two LANs • WLAN offers a cost-effective solution to users with difficult physical installations such as: • campuses • hospitals • businesses with more than one location in immediate proximity but separated by public thoroughfare. • This type of installation requires two access points. • Each access point acts as a bridge or router connecting its own LAN to the wireless connection. • The wireless connection allows the two access points to communicate with each other, and therefore interconnect the two LAN's.
WLAN Scenarios Mobile users, both on and off “campus” Where physical wiring is difficult or impossible Connecting small groups to a larger work environment. Wireless networking in these environments is a very cost effective alternative Temporary wireless LANs can easily be created for exhibitions, school or business projects, all without any trailing cabling.
Security • Potential security issues; physical access not required. • 802.11 wireless communications cannot be received nor decoded by simple scanners or short wave receivers. • However, eavesdropping is possible using special equipment. • 802.11 WLAN have a function called WEP (Wired Equivalent Privacy); a form of encryption. • Access Points can control access via unique MAC addresses. • Virtual Private Networking (VPN) techniques will work over wireless networks in the same way as traditional wired networks. This is the best approach.
WLAN Security: SSID Network access control can be implemented using an SSID associated with an AP or group of APs. The SSID provides a mechanism to "segment"a wireless network into multiple networks serviced by one or more APs. Each AP is programmed with an SSID corresponding to a specific wireless network. To access this network, client computers must be configured with the correct SSID. The SSID acts as a simple password
WLAN Security: MAC Filtering A client computer can be identified by the unique MAC address of its 802.11 network card. Each AP can be programmed with a list of MAC addresses associated with the client computers allowed to access the AP. If a client's MAC address is not included in this list, the client is not allowed to associate with the AP. MAC address filtering provides good security, but is best suited to small networks. Each AP must be manually programmed with a list of MAC addresses, and the list must be kept up-to-date.
WLAN Security: WEP WEP provides encrypted communication All clients and APs on a wireless network use the same key The key resides in the client computer and in each AP Support for WEP is standard WEP specifies the use of a 64-bit encryption key Implementations of non-Wi-Fi 128-bit key encryption exists The 802.11 standard does not specify a key management protocol, so all keys on a network must be managed manually
WLAN Security: VPN A VPN solution for wireless access is the most suitable alternative to WEP and MAC address filtering. VPN solutions are already widely deployed to provide remote workers with secure access to the network via the Internet. In this remote user application, the VPN provides a secure, dedicated path (or "tunnel") over an "untrusted" network-in this case, the Internet. Various tunneling protocols are used in conjunction with standard, centralized authentication solutions,such as Remote Authentication Dial-In User Service (RADIUS) servers.
WLAN Security: VPN VPN technology can also be used for secure wireless access; the "untrusted" network is the wireless network. The APs are configured for open access with no WEP encryption, but wireless access is isolated from the enterprise network by the VPN server and a VLAN between the APs and the VPN servers. The APs should still be configured with SSIDs for segmentation. Authentication and full encryption over the wireless network is provided through the VPN servers that also act as gateways. Unlike the WEP key and MAC address filtering approaches, the VPN-based solution is scalable to a very large number of users. Section End
Cell phone Modem Access Point Peripherals ThinkPad WorkPad Personal Area “Connectivity” Personal Area Networks (PAN) and Bluetooth 1. What is Bluetooth? 2. Characteristics? 3. Usage scenarios: Today/Tomorrow? 4. 802.11 vs. Bluetooth vs. IR 5. Security 6. IBM’s Contribution
What is Bluetooth.... Defacto standard for wireless Personal Connectivitytechnology Specification for small-form factor, low-cost, short range radio links between mobile PCs, mobile phones and other portable devices. The Bluetooth Special Interest Group (SIG) is an industry group consisting of leaders in the telecommunications and computing industries that are driving development of the technology and bringing it to market. IBM, Toshiba, Ericsson, Nokia, Intel - Motorola, Microsoft, Lucent and 3Com - plus 2000+ other companies
Bluetooth Market Potential W/W Bluetooth Enabled Equipment Forecast (Units in Millions) Source : Cahners In Stat July 2000
Characteristics Operates in the 2.4 GHz Industrial-Scientific-Medical (ISM) band at a data rate of 721Kb/s Uses Frequency Hopping(FH) spread spectrum, which divides the frequency band into a number of channels (2.402 - 2.480 GHz yielding 79 channels). 1600 hops/sec. During a connection, radio transceivers hop from one channel to another in a pseudo-random fashion, determined by the Master. Supports up to 8 devices in a piconet (1 master and up to 7 slaves sharing a channel). Up to 10 piconets can combine to form scatternets (scaling).
Piconets/Scatternets A collection of devices Connected via Bluetooth in an ad hoc fashion. Starts with two devices, and may grow to eight (including the master) Master sets the clock and hopping pattern. However, when establishing a piconet, one unit will act as a master and the other(s) as slave(s) for the duration of the piconet connection. A Scatternet is the linking of multiple co-located piconets through the sharing of common master or slave devices.
Characteristics Built-in security. Non line-of-sight transmission through walls and briefcases. Omni-directional. Supports both voice and data services; easy integration of Serial links and TCP/IP for networking Regulated by governments worldwide, even France ! Supports both one-to-one and one-to-many networking topologies Devices must be in a 10 meter radius for communications to occur.
Bluetooth Protocol Stack WAE vCard/vCal Lower Transport WAP Obex Upper Transport Middleware TCP/ UDP Adopted IP PPP Service Discovery TelephonyControl RFComm Audio LMP L2CAP HCI BaseBand Radio
Network Topologies One-to-one One-to-many (generally Serial mode) (generally TCP/IP mode)
Key Notebook Usage Models • Bluetooth Usage Models for Notebooks • Dial-Up Networking via cell phone • Syncing • File Transfer • Target Devices • Cellphone • Desktop • Handheld • Other Notebook Dial-up Networking Synchronization File Transfer
Key Handheld Usage Models • Bluetooth Usage Models for Handhelds • Dial-up Networking via Cell phone • Syncing • File Transfer (business cards) • Target Devices • Cell phone • Desktop • Notebook • Other handheld Dial-up Networking Synchronization File Transfer
Key Desktop Usage Models Bluetooth Usage Models for Desktop Syncing File Transfer Lan Access for devices Target Devices Handheld Notebook Synchronization File Transfer
Other Usage Scenarios Telephony Headset Infrastructure Data Access Points
Bluetooth Access to WAN A computer network that spans a relatively large geographical area. Typically, a WAN consists of two or more local-area networks (LANs). Computers connected to a WAN are often connected through PSTNs. They can also be connected through leased lines or satellites. The largest WAN in existence is the Internet.
Future Usage Scenarios Ease-of-Use Personal Area Networking Automotive Wake on Bluetooth Human Interface Devices Audio/Visual Walk-up Printing Hidden Computing Instant Postcard Multi-Piconet Cordless Computer Intercom FAX LAN Access Headset Multi-Point Dial-Up Networking File Transfer Synchronization Point to Point Today Tomorrow The Future
Future Usage Scenarios Standard Connectivity Today: Many Cable Connections • Serial • Parallel • Mouse • Keyboard • Floppy • Audio • IR • USB • Video • Docking • Power Adds weight and cost Decreases reliability
Future Usage Scenarios Standard Connectivity Today: Many Cable Connections • Serial • Parallel • Mouse • Keyboard • Floppy • Audio • IR • USB • Video • Docking • Power Tomorrow: Fewer Cables Bluetooth • USB • Video • Docking • Power Reduces weight and cost Increases reliability Adds weight and cost Decreases reliability
Future Usage Scenarios Personal Area Networking Spontaneous / ad-hoc networking Computer Supported Cooperative Work (CSCW) environments Workgroup collaboration Between many different devices PC, PDA, Printer, Mobile phone, Communicator, Digital Camera (Still & Video) Digital TV, MP3 Player etc… Slave-to-slave communication is through the master
Prototype work by Pervasive group Walk up “push” of adverts and services. Demo uses IBM Research Blue Drekar stack available from Alphaworks. Contact Yook Siong Chin.
Location Aware Services • NOT Location Based Services • eg - Where is nearest xyz ? • Pay for vending. • But AWARE of the user • anticipate needs • prepare and be ready to interact • only need to know that the user is present • or indeed no longer present • Bluetooth device eg Phone or PDA is ideal. • Carried with user • Individual
Total effect = real ease of use • Come into office • PC unlocks • Buddy status says user at desk • Phone calls go to desk phone • Go to lab • Office PC locks up • Buddy status says away from desk • Lab lights turn on • Phone calls go to lab • Go to lunch • lab lights go off • phone calls go to mobile • Go back to office • PC unlocks • Buddy status says user at desk • Phone calls go to desk phone • etc... Without pressing a single button !
Security Unique MAC address for every Bluetooth device Bluetooth has built-in encryption and authentication In addition a frequency-hopping scheme with 1600 hops/sec is employed. All of this, together with an automatic output power adaptation to reduce the range exactly to requirement, makes the system extremely difficult to eavesdrop
Security Implementations Security mode 1 (non-secure). • A device does not initiate any security procedures. • Security mode 2 (service-level enforcement security). • A device does not initiate security procedures before channel establishment at the service level. This mode allows different and flexible access policies for applications, and is used especially for running applications with different security requirements in parallel. • Security mode 3 (link-level enforced security). • A device allows only authenticated connections. • Bluetooth technology has three security attributes • Authorization • Authentication • Encryption.
Security Implementations • Authorization • Database of services which a device has authorization to use • Authentication • The user can choose to "auto" trust devices or "manually" trust devices. • Authentication is accomplished using a challenge-response scheme using symmetric link keys. • If the devices do not share a link key, one is created through a process called "pairing" and based on a shared secret association, like a PIN code. • If a device does not have a mechanism to enter a PIN, a restricted form link key, called a unit key, is generated based on the device's address and random number. • Encryption can only be activated after authentication. Encryption is based on a stream cipher easily implemented in hardware or software.
IBM's Contribution to the SIG IBM is one of the original 5 founding members. IBM authored the discovery protocol (discovery protocol is a method to explore and discovery Bluetooth devices and services within range) IBM contributed to the lower layer protocol that makes up the entire Bluetooth protocol stack (link level protocol) IBM contributed to the Bluetooth world-wide regulatory working bodies to harmonize the 2.4GHz frequency spectrum use for Bluetooth and other government agency requirements. IBM funds and contributes to many of the the organization’s events. IBM is leading the effort to standardize IEEE 802.15, which will embrace Bluetooth as a short range wireless standard. Section End