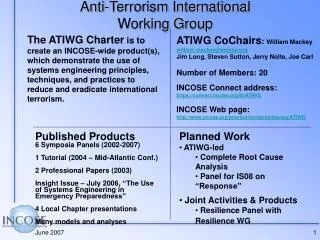
Anti-Terrorism Level II
Anti-Terrorism Level II. Cyber “Terrorism” The Future of Modern Terrorism? . References. Rand Corporation Operation Cyber Sweep DOJ U.S. Attorneys Office of Legal Education. OVERVIEW. Definitions The Cyber Terrorist Defined Goals and Objectives of a Cyber Terrorist

Anti-Terrorism Level II
E N D
Presentation Transcript
Anti-TerrorismLevel II Cyber “Terrorism” The Future of Modern Terrorism?
References • Rand Corporation • Operation Cyber Sweep DOJ • U.S. Attorneys Office of Legal Education
OVERVIEW • Definitions • The Cyber Terrorist Defined • Goals and Objectives of a Cyber Terrorist • Cyber Terrorism Tactics and Techniques • Noted Incidents and Attacks • Cyber Terrorist potential Objectives “Scenarios” • Prevention and Detection
Cyber Terrorism Definitions • COMPUTER TAMPERINGunauthorized modifications of computer programs or the way in which a computer or computer network operates • COMPUTER TRESPASSdirected generally towards computer hackers lack of authorization to access a computer or computer system • COMPUTER FRAUD use of a computer to perpetuate the fraud CYBERSTALKING use of e-mail or electronic means of communicating language threatening to inflict harm to persons or property, or for the purpose of extorting money or property
The Cyber Profiles • Hackers • Crackers • Cyber Terrorists
Hackers • “Hackers”: Computer Hacking is Defined as the Display of Exceptional Computer Talent. • Who Does Not Engage in Criminal Conduct for Profit or Gain • Separate Society • Those who have the ability to enter computer systems without consent from the owner (Computer Trespassing)
Crackers • “Crackers”(Cyber Extortionist): Computer Cracking is Defined as a Person Who, Without Authorization, Uses Computer Skills To: • Access, Move, Alter, Delete, or Destroy Automated Data or Information • Breaks codes for personal profit or gain
Crackers • Crackers are Most Commonly Associated with Terrorism • Mostly Due to the Blackmail Schemes Against the Banking Industry (Extortion of money) • These Assaults Normally Go Unreported
Cyber Extortionist Gangs/Crackers • Four Operational “High End” Cyber Extortionist Gangs • One American Based, One Russian Based, and two Others Unknown.
Cyber Extortionist • Ability of Cyber Extortionists: • Cyber Extortionist demands are met within hours and money is wired to foreign bank accounts. • Cyber Extortionists then remove the money within minutes of arrival without a trace.
The Cyber Terrorist • Is defined as one who assaults an electronic communications network with intent to coerce or intimidate a government. • They can act very similar to and within terrorist organizations
Goals of the Cyber Terrorists • Access: Starting point, weak passwords with internet and e-mail use (Social Engineering) • Control: The goal of remote administration • Mining (Information Sharing): Process that supports the knowledge of acquisition Uses FOUR Modes: Transmission, Connection, Aggregation, Retrieval
Cyber Terrorism Tactics • Sent Mail (sending Malicious Codes) • Packet Sniffing (Gather Network Traffic) • Man in the Middle Technique (one computer system believes its talking to another when in reality it is talking one of the three profiles) • Key Logging (Gather Keyboard Keystrokes) • Viruses • Onel A Deguzmann
Cyber terrorism Tactics • Security Administration Tools for Analyzing Networks • Mining (Information Sharing) • Emergency Destruction - High Energy Radio Frequency Guns - Electro Magnetic Pulse Bombs - Thermite
Pentagon Computers Attacked • Military Satellite System “Software” • In Late “April 98” The Computer Security Expert John Vranesevich was Contacted. • Vranesevich was involved in tracking down Israeli hacker “The Analyzer” who broke into the Pentagon in February
Pentagon Computers Attacked • The Software Stole Coordinates to the Military Global Positioning System, Used To Target Missiles, and Accurately Pinpoint Unit Locations. • Vranesevich Interviewed Them Via the Internet Relay Chat and E-Mail and Posted Pictures of the Stolen Software In Action On His Web Site.
Pentagon Computers Attacked • The Defense Department Confirmed the Software Was Genuine. • The Group Stated During The Interviews • “I think international terrorist groups would be interested in the data we could gain access to.” • “Governments would buy it for intelligence purposes.” • “The information is very dangerous in the wrong hands”
Pentagon Computers Attacked • Vranesevich Said Members Of The Group Range From 19 to 28, Older Than The Average. • The Group Claims 15 Members--Eight In The United States, Five In Britain And Two In Russia.
Noted Incidents And Attacks Kevin Poulsen Handle: Dark Dante Claim to fame: In 1990 Poulsen took over all telephone lines going into Los Angeles area radio station KIIS-FM, assuring that he would be the 102nd caller. Poulsen won a Porsche 944 S2 for his efforts. First encountered a computer: When his parents bought him a TRS-80 (better known as a "Trash-80"). Unusual tools: A set of locksmith tools he used to break into phone company trailers. He was caught after a friend commemorated the break-ins with snapshots of Poulsen picking locks.
Noted Incidents And Attacks Kevin Poulsen Little-known fact: Admitted breaking into computers to get the names of undercover businesses operated by the FBI. Current status: Thanks to an episode of Unsolved Mysteries, Kevin Poulsen was arrested and spent three years in prison. He was then forbidden to touch a computer for another three years. Poulsen is now a self-proclaimed "reformed and penitent" journalist, and serves as editorial director for Security Focus.
Noted Incidents And Attacks • Rome Laboratory, New York • Disguised As a User Of Rome Labs Launched Attacks Against NASA, Wright Patterson AFB, Defense Contractors, and Other Organizations • This Was All Unknown To Rome Labs for at Least Three Days. • One British Hacker Was Caught, the Other Unidentified Hacker Escaped.
Other Incidents Of Note • A “PLO” Virus Developed at Hebrew University, in Israel. • Japan Groups have Attacked the Computerized Control Systems for Commuter Trains, Paralyzing Major Cities • The Italian Red Brigade’s Manifesto Specified the Destruction of Computer Systems and Installations “Striking The Heart Of The State”
Other Incidents Of Note • Sinn Fein Supporters Working Out of the University Of Texas, Austin, TX, Posted Sensitive Details About British Army Intelligence Installations, Military Bases, and Police Stations In Northern Ireland On the Internet.
Potential Objectives (Scenarios) • The Key Attribute(s) of the Cyber Terrorist Attacks Through the Computer, Is Minimal Risk and Achievement of Desired Objective(s)/Goals • How Can This Be Accomplished?
Potential Objectives (Scenarios) • Remotely Through the Computer Access Food Processing Control Systems of a Cereal Manufacturer, Changing the Levels of Iron Supplements, Sickening and Killing the Children of a Nation. (Recently seen in California with baby food) • (Key Attribute(s)): No Risk to the Cyber Terrorist and Fulfillment of an Objective!
Potential Objectives (Scenarios) • Place a Number of Computerized Bombs In a City, All Transmitting Encrypted Patterns, that are Received by the Others. If One Stops Transmitting or is Compromised They Go Off Simultaneously.
Potential Objectives (Scenarios) • Disrupt the Banking Industry, International Financial Transactions, and Stock Exchanges. • (Key Attribute(s)): Loss of Confidence in the Government Economic System, Destabilization of a Government From Within.
Potential Objectives (Scenarios) • Launch Attacks Against the Air Traffic Control Systems to Include the In-Flight Deck Sensors and Cause Two Large Aircraft to Collide this Could Also Be Conducted Against a Railway System. Exchanges. • (Key Attribute(s)): No Risk of Manpower or Equipment.
Potential Objectives (Scenarios) • Remotely Alter the Formulas of Medication at Pharmaceutical Manufacturers, With Unfathomable Potential For Loss of Life. • (Key Attribute(s)): No Risk of Manpower or Equipment.
Potential Objectives (Scenarios) • Remotely Change the Pressure in Gas Lines, Causing a Valve Failure; a Block of a Sleepy Suburb Detonates and Burns. In an Alternate Scenario an Electrical Grid Becomes Vulnerable. • (Key Attribute(s)): No Risk of Manpower or Equipment.
Prevention/Detection • Safe Computing Practices • Do Not Share Resources Across a Network Without Using Password Controls • Never Execute a Program Received Through Unknown Sources • Routinely Verify All Software is Current • Use a Virus Scanner • Use a firewall (www.zonelabs.com)
Prevention/Detection • Detection: • Symantec Norton Anti-Virus • Army’s Land Information Warfare Activity • Symantec’s Ant-Virus products and Latest Signature File - http://powhatan.iiie.disa.mil/symantec.htm • http://www.cert.mil (access from any computer, however, downloads must be done from a .mil domain)
Prevention/Detection • Reporting • At a Minimum, the Site’s Information Systems Security Manager (each site does not have), the Responsible Computer Incident Response Team, and a Law Enforcement Agent Should be Contacted
SUMMARY • Definitions • The Cyber Terrorist Defined • Goals and Objectives of a Cyber Terrorist • Cyber Terrorism Tactics and Techniques • Noted Incidents and Attacks • Cyber Terrorist potential Objectives “Scenarios” • Prevention and Detection