About your assignment
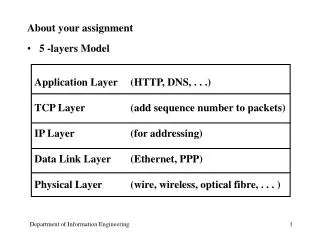
About your assignment 5 -layers Model Application Layer (HTTP, DNS, . . .) TCP Layer (add sequence number to packets) IP Layer (for addressing) Data Link Layer (Ethernet, PPP) Physical Layer (wire, wireless, optical fibre, . . . ) Hacking Common security problems virus

About your assignment
E N D
Presentation Transcript
About your assignment • 5 -layers Model Application Layer (HTTP, DNS, . . .) TCP Layer (add sequence number to packets) IP Layer (for addressing) Data Link Layer (Ethernet, PPP) Physical Layer (wire, wireless, optical fibre, . . . )
Hacking • Common security problems • virus • malicious computer program that makes copies of itself and attaches those copies to other programs • Trojan horse • a program that appears to have one ubiquitous function, but actually has a hidden malicious function
Hacking • Dictionary attack • try all possible words in a dictionary and compare with the encrypted password in the server • need to get the password file first password mary Password file One-way encrypting function xo12u50zag dictionary
Denial of Service Attack • Sends fake IP packets to the web server • server sends an reply to the client, waiting for the HTTP message to arrive • but the source address is faked, so the server has to wait forever • a server can only support a limited number of concurrent requests, if all these requests are faked, then the server cannot do any useful work
Denial of Service Attack • How to prevent it? • charge the packets ! • check the IP address at the source
Denial of Service Attack • Details of the attack • client > initial packet with a sequence no to server • server> return its own sequence no to client • client> OK, I got your sequence number • client> the request • server> return the requested file • client> disconnect • server> disconnect
Christmas 1994 • 25th December, 1994, 14:09:32 . . . • Security expert Tsutomu Shimomura was on a skiing trip • meanwhile his computer in was break-in by a hacker • 15th February, 1995 • By tracing the traffic log, Kevin Mitnick, the most wanted computer outlaw, was caught • Paperbacks and movie about the story • Takedown by Shimomura and John Markoff • The Fugitive Game by Jonathan Littman • Takedown (movie) by Miramax
IP spoofing • Security hole in remote login (rlogin) • authentication based on IP address • password is not required • IP spoofing attack • host A: attacker host B: the machine to be attacked host C: the machine impersonated by the attacker, C is trusted by B • A sends the 1st packet to host B using the false IP source address (host C) • B checks the IP, verifies it, find nothing wrong, so let the hacker login without checking the password
B (machine under attacked) 1st 2nd C (friend of B) A (hacker) 3-way handshakes • Problem: 3-way handshakes • 1st segment: A --------------> B • 2nd segment: A <-- ------------ B • 3rd segment: A --- ACK ---> B • BUT B sends the 2nd segment to C, so that A cannot return the ACK to B without knowing the sequence number used by B
Sequence number prediction • BUT the ISN of B can be guessed!! • First, the hacker makes a real connection to B • because the connection is real, the 2nd segment sent by B will be received by the hacker • the 2nd TCP segment contains the number of B • after getting the number of B, the hacker launches the attack • return the 3rd packet using the guessed ISN • how to guess the number? • the number is incremented by 128000 for every new connection
Sequence number prediction • so that for two consecutive connection requests, the ISN will be differed by 128,000 • if there is no other connection request to the server during that time, the ISN can be guessed accurately and easily • the best time to attack is when there is little connection requests to the server • Christmas • so after sending the 1st packet to B, A sends the the 3rd packet to B with the guessed number
SYN flooding • but the story does not end here, note that when B sends the 2nd packet to C, C will return a packet (reset) and spoils the attack • To prevent C from returning the packet, A sends a large number of SYN packets (the first packet) to C using dead site as source address • C receives a lot of connection requests and opens up many half-open connections (waiting the the 3rd packet to return) • but since the source is a non-existing host, the 3rd handshake never come back • prevent C from receiving anything from B