Quantum Cryptography
Quantum Cryptography. Qingqing Yuan. Outline. No-Cloning Theorem BB84 Cryptography Protocol Quantum Digital Signature. One Time Pad Encryption. Conventional cryptosystem: Alice and Bob share N random bits b 1 …b N Alice encrypt her message m 1 …m N b 1 m 1 ,…,b N m N

Quantum Cryptography
E N D
Presentation Transcript
Quantum Cryptography Qingqing Yuan
Outline • No-Cloning Theorem • BB84 Cryptography Protocol • Quantum Digital Signature
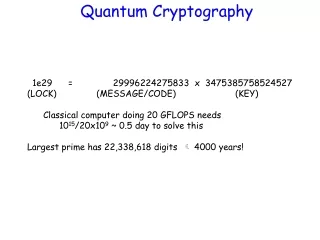
One Time Pad Encryption • Conventional cryptosystem: • Alice and Bob share N random bits b1…bN • Alice encrypt her message m1…mNb1m1,…,bNmN • Alice send the encrypted string to Bob • Bob decrypts the message: (mjbj)bj = mj • As long as b is unknown, this is secure • Can be passively monitored or copied
Two Qubit Bases • Define the four qubit states: • {0,1}(rectilinear) and {+,-}(diagonal) form an orthogonal qubit state. • They are indistinguishable from each other.
No-Cloning Theorem • |q = α|0+β|1 • To determine the amplitudes of an unknown qubit, need an unlimited copies • It is impossible to make a device that perfectly copies an unknown qubit. • Suppose there is a quantum process that implements: |q,_|q,q • Contradicts the unitary/linearity restriction of quantum physics
Wiesner’s Quantum Money • A quantum bill contains a serial number N, and 20 random qubits from {0,1,+,-} • The Bank knows which string {0,1,+,-}20 is associated with which N • The Bank can check validity of a bill N by measuring the qubits in the proper 0/1 or +/- bases • A counterfeiter cannot copy the bill if he does not know the 20 bases
Quantum Cryptography • In 1984 Bennett and Brassard describe how the quantum money idea with its basis {0,1} vs. {+,-} can be used in quantum key distribution protocol • Measuring a quantum system in general disturbs it and yields incomplete information about its state before the measurement
Quantum Channel Alice Classical public channel Bob Eve BB84 Protocol (I) • Central Idea: Quantum Key Distribution (QKD) via the {0,1,+,-} states between Alice and Bob O(N) classical and quantum communication to establish N shared key bits
Quantum Public & Classical Shared Key BB84 Protocol (II) • Alice sends 4N random qubits {0,1,+,-} to Bob • Bob measures each qubit randomly in 0/1 or +/- basis • Alice and Bob compare their 4N basis, and continue with 2N outcomes for which the same basis was used • Alice and Bob verify the measurement outcomes on random (size N) subset of the 2N bits • Remaining N outcomes function as the secrete key
Security of BB84 • Without knowing the proper basis, Eve not possible to • Copy the qubits • Measure the qubits without disturbing • Any serious attempt by Eve will be detected when Alice and Bob perform “equality check”
Quantum Coin Tossing Alice’s bit: 1 0 1 0 0 1 1 1 0 1 1 0 Alice’s basis: Diagonal Alice sends: - + - + + - - - + - - + Bob’s basis: R D D R D R D R D D R R Bob’s rect. table: 0 1 0 1 1 1 Bob’s Dia. table: 0 1 0 1 0 1 Bob guess: diagonal Alice reply: you win Alice sends original string to verify.
Quantum Coin Tossing (Cont.) • Alice may cheat • Alice create EPR pair for each bit • She sends one member of the pair and stores the other • When Bob makes his guess, Alice measure her parts in the opposite basis
Arguments Against QKD • QKD is not public key cryptography • Eve can sabotage the quantum channel to force Alice and Bob use classical channel • Expensive for long keys: Ω(N) qubits of communication for a key of size N
Practical Feasibility of QKD • Only single qubits are involved • Simple state preparations and measurements • Commercial Availability • id Quantique: http://www.idquantique.com
Outline • No-Cloning Theorem • BB84 Cryptography Protocol • Quantum Digital Signature
Pros of Public Key Cryptography • High efficiency • Better key distribution and management • No danger that public key is compromised • Certificate authorities • New protocols • Digital signature
Quantum One-way Function • Consider a map f: k fk. • k is the private key • fk is the public key • One-way function: For some maps f, it’s impossible (theoretically) to determine k, even given many copies of fk • we can give it to many people without revealing the private key k
Digital Signature (Classical scheme) • Lamport 1979 • One-way function f(x) • Private key (k0, k1) • Public key (0,f(k0)), (1,f(k1)) • Sign a bit b: (b, kb)
Quantum Scheme • Gottesman & Chuang 2001 • Private key (k0(i), k1(i))(i=1, ..., M) • Public key • To sign b, send (b, kb(1), kb(2), ..., kb(M)). • To verify, measure fkto check k = kb(i).
Levels of Acceptance • Suppose s keys fail the equality test • If sc1M: 1-ACC: Message comes from Alice, other recipients will agree. • If c1M < s c2M: 0-ACC: Message comes from Alice, other recipients mightdisagree. • If s > c2M: REJ: Message might not come from Alice
Reference • [BB84]: Bennett C. H. & Brassard G., “Quantum cryptography: Public key distribution and coin tossing” • Daniel Gottesman, Isaac Chuang, “Quantum Digital Signatures” • http://www.perimeterinstitute.ca/personal/dgottesman/Public-key.ppt
Discussions…… Thank you!