Quantum Cryptography
Quantum Cryptography. Berk Akinci. Overview. Classical Cryptography Quantum Random Number Generation Quantum Cryptography Using Entanglement Using Uncertainty Devices Single-Photon Emitter Single-Photon Detector. Classical Cryptography. Computational security Practical; widely used

Quantum Cryptography
E N D
Presentation Transcript
Quantum Cryptography Berk Akinci Berk Akinci
Overview • Classical Cryptography • Quantum Random Number Generation • Quantum Cryptography • Using Entanglement • Using Uncertainty • Devices • Single-Photon Emitter • Single-Photon Detector Berk Akinci
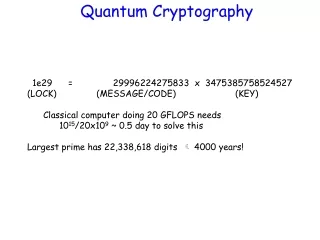
Classical Cryptography • Computational security • Practical; widely used • Examples: AES, DES, RC-4, RSA, DH… • Unconditional security • Breaking is impossible • Not practical for most applications • Example: One-time pad • Problem: Key Distribution Berk Akinci
One-time pad Insecure communication channel Eve Alice Encryption Decryption Bob ? Key Key Plaintext: 0000 1111 0000 1111… Random Key: 0110 0010 0110 1110… Ciphertext: 0110 1101 0110 0001… Berk Akinci
Q. Random Number Generator • True Random Numbers are critical! • Quantum processes are fundamentally random Semi-transparent mirror idQuantique - Quantis Photon source Single-photon detector ~50% 1 2” ~50% Single-photon detector Unbiasing 0100111011… 0 Berk Akinci
Quantum Cryptography • Quantum Key Distribution • Uses laws of quantum mechanics • Provides unconditional security • One of two fundamentals • Uncertainty • Entanglement Berk Akinci
Using Entanglement • Create pairs of entangled photons • Transmit them to Alice and Bob • Alice and Bob get ‘complementary’ photons • Difficult to keep states entangled for long time/distances • No commercial application yet Berk Akinci
Using Uncertainty • Measuring a quantum system disturbs it • Alice sends individual quanta • If Eve makes measurements, Bob can’t; that’s tamper-evident • Eve can’t reproduce the original • Neither Eve nor Bob can ever detect the entire state • Devices by idQuantique and MagiQ Berk Akinci
Using Uncertainty – Principles • Practical approach uses photons • Photons can be transmitted over long distances • Photons exhibit the required quantum mechanical properties • Quantum properties exploited • Photons can not be divided or duplicated • Single measurement is not sufficient to describe state fully Berk Akinci
Polarized Photons and Filters Source: id Quantix – Vectis… Berk Akinci
BB84 Protocol Source: id Quantix – Vectis… Berk Akinci
Using Uncertainty – Reality • Photon polarization is transformed through fiber • Autocompensation – Faraday orthoconjugation • No good single-photon emitter • No good single-photon detector • Quantum Error Correction • Privacy Amplification Berk Akinci
Faraday orthoconjugation Source: Risk – Bethune Berk Akinci
Single-Photon Detector • Avalanche Photodiode (APD) • InGaAs APD used in ‘Geiger’ mode • Reverse biased just below breakdown idle • Reverse biased just above breakdown for 1ns • Kept cool (e.g. 140K) to prevent thermally-induced avalanche Berk Akinci
Single-Photon Emitter • ‘Approximated’ by attenuating a train of laser pulses • If attenuating to average power matching a single photon • 37% 0 photon – no information • 37% 1 photon • 26% 2+ photons – security risk! Berk Akinci
Single-Photon Emitter (Cont.) • Practical systems attenuate to 0.1 photon • 89.5% 0 photon • 10% 1 photon • 0.5% 2+ photons Berk Akinci
Bibliography • Risk, W. P.; Bethune, D. S. – “Quantum Cryptography – Using Autocompensating Fiber-Optic Interferometers.” Optics and Photonics News. July 2002, pp 26-32 • id Quantique – “Quantis-OEM Datasheet.” v1.3, July 2004, http://www.idquantique.com • id Quantique – “White Paper – Random Numbers Generation using Quantum.” Version 2.0, August 2004, http://www.idquantique.com • id Quantique – “White Paper – Understanding Quantum Cryptography.” Version 1.0, April 2005, http://www.idquantique.com • Wikipedia community – “Quantum Cryptography.” Wikipedia – The Free Encyclopedia. Viewed on April 12, 2006. http://en.wikipedia.org/wiki/Quantum_cryptography Berk Akinci