Access Control Lists
Access Control Lists. Types. Standard Extended. Standard ACLs. Use only the packet’s source address for comparison 1-99. Extended ACLs. Provide more precise (finer tuned) packet selection based on: Source and destination addresses Protocols Port numbers 100-199.

Access Control Lists
E N D
Presentation Transcript
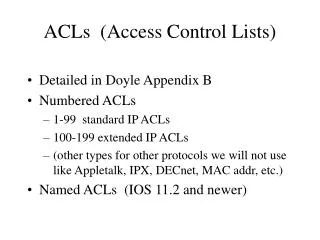
Types • Standard • Extended
Standard ACLs • Use only the packet’s source address for comparison • 1-99
Extended ACLs • Provide more precise (finer tuned) packet selection based on: • Source and destination addresses • Protocols • Port numbers • 100-199
Steps to Create an ACL • Create ACL in global config • Assign to interface • Decide the direction • In • Out
How do ACLs work? • Processing occurs line by line from top to bottom. • New lines are added at the end of the current list. • Last line of an ACL is an implicit “deny any.”
How does a Standard ACL work? • If source IP address is matched: • Permit or deny statement is processed • Permit – action in ACL is performed • Deny – packet is dropped • Implicit Deny – If a packet’s address does not match an earlier statement an implicit deny any occurs at the end of every ACL and the packet is dropped.
Wildcard Masks • Are used to specify (by bits) the traffic you are trying to filter by address. • Use 1s to ignore, 0s to match. • In the example below, only the 1st 2 octets will be examined: • 172.16.0.0 0.0.255.255
Global Standard ACL command • access-listaccess-list-number {permit |deny} source-ip-addresswildcard-mask [log] • Log – causes each packet that matches this statement to generate a log entry that is recorded by the router.
Examples of Standard ACLs • To permit all packets for the network number 172.16.0.0 • Access-list 20 permit 172.16.0.0 0.0.255.255
Examples Cont’d • To permit traffic from the host 172.16.1.1 only • Access-list 20 permit 172.16.1.1 0.0.0.0
Examples Cont’d • To permit traffic from any source address. • Access-list 20 permit 0.0.0.0 255.255.255.255 OR • Access-list 20 permit any
Examples Cont’d • To permit traffic from the subnet 12.16.0.0 through 12.31.0.0 • Access-list 20 permit 12.16.0.0 0.15.255.255
Identical Statements • Access-list 22 permit 0.0.0.0 255.255.255.255 • Access-list 22 permit any
Identical Statements • Access-list 23 permit 172.16.1.1 0.0.0.0 • Access-list 23 permit host 172.16.1.1
How does an Extended ACL work? • All conditions must match • Test sequence in this order • Source Address • Destination Address • Protocol • Port No. or Protocol Options • Permit or Deny decision
Extended ACL command • access-listnumber {permit|deny} protocolsource-ip-addresssource-wildcard-maskdestination-ip-addressdestination-wildcard-maskeqport-number [log]
Some Protocols with Port Numbers • FTP – 21 • Telnet – 23 • SMTP – 25 • DNS – 53 • TFTP – 69 • WWW, HTML – 80 • POP3 - 110 • SNMP - 161
Major differences • Standard ACL • Use only source address and requires fewer CPU cycles. • Place as close to destination as possible. • Extended ACL • More flexible and requires more CPU cycles. • Place as close to source as possible. (This keeps undesired traffic and ICMP messages away from the network backbone.)
Do I place an ACL in? • In • Requires less CPU processing because every packet bypasses processing before it is routed. • Filtering decision is made prior to the routing table.
Do I place an ACL out? • Out • Routing decision has been made and the packet is switched to the proper outbound interface before it is tested against the access list. • ACLs are outbound unless otherwise specified.