ClearPath MCP Encryption
ClearPath MCP Encryption. Steve Koss, Distinguished Engineer and Chief Architect. The What and Why of Encryption. Terminology Symmetric Key Encryption Public Key Encryption (PKE) Certificates SSL/TLS - Combines all three Why Encrypt Reduces the chance of data exposure

ClearPath MCP Encryption
E N D
Presentation Transcript
ClearPath MCP Encryption Steve Koss, Distinguished Engineer and Chief Architect
The What and Why of Encryption • Terminology • Symmetric Key Encryption • Public Key Encryption (PKE) • Certificates • SSL/TLS - Combines all three • Why Encrypt • Reduces the chance of data exposure • Makes Auditors Happy
Data Privacy CapabilitiesOverview • Encryption of data across networks • File transfer via FTP/SFTP/NFT/DMV • Terminal emulator sessions • Transport Layer Security/Secure Sockets • IPsec – packet layer encryption • Encryption of data at rest • Tape encryption • Disk encryption • Security Center – Key Management • Stealth
Network SecurityFile Transfer Protocols/Products • Many different methods to transfer and protect files between MCP and other systems. • FTP/FTPS • SFTP (SSH) – introduced in MCP 14.0 • Secure File Transfer (NFT) • SAN DataMover • File transfer capabilities on remote systems determine most suitable product. • Security is configurable on all but SFTP (no unsecure version). • To use any of these on ClearPath MCP, MCP cryptography must be available.
Network SecurityFile Transfer Protocol (FTP) • File Transfer Protocol (RFC 959) supported by most systems • Transfers can be secured via SSL/TLS • IMPLICIT model – two sets of ports (one secure, one insecure) • EXPLICIT model – one set of ports (usually 21/20) and there are commands to turn SSL/TLS on/off • AUTHMODE controls where SSL/TLS is used • IMPLICIT, EXPLICIT, EXPLICITLOGON, EXPLICITCOMMAND • New features introduced in MCP 13.1 • Client Certificates – ability to specify an X.509 certificate for additional validation • Can allow acceptance of self-signed server certificates • Can secure data port when control port is not secured.
Network SecuritySecure File Transfer Protocol (SFTP) • Secure File Transfer Protocol (SFTP) is part of the SSH protocol suite • Defined by <draft-ietf-secsh-filexfer-02.txt> • MCP implementation supports version 3 (but does NOT support all of the commands yet) • Interoperable with implementations which use openssh() toolkit (most flavors of Linux) and psftp (part of PuTTY). • Full list at: • http://www.support.unisys.com/common/matrices/ViewMatrix.aspx?pla=MCP&nav=MCP&PageID=649
SFTPConfiguration • Support for SFTP has been integrated into the FTPSUPPORT product and can be accessed from: • Batch FTP Client (COPY) • Interactive FTP Client (U FTP) • SFTP configuration is through FTPSUPPORT configuration file (*SYSTEM/FTP/SUPPORT/CONFIGURATION) • Keys and trust are configured through SecurityCenter • Server public keys (management and trust) • Usercode public keys (management)
SFTPCopy – Example #1 Batch Client • COPY FILENAME (FTPTYPE=IMAGE) TO DISK(PACK, IPADDRESS=“xxx.xxx.xxx.xxx”,AUTHMODE=SSH, USERCODE=“GUEST”/”GUEST”) Interactive Client • U FTP • AUTHMODE SSH • OPEN xxx.xxx.xxx.xxx(with GUEST/GUEST credentials) • TYPE IMAGE • PUT FILENAME
SFTPCopy – Example #2 Remote username defaults tocalling usercode, but can beoverridden Batch Client • COPY [SFTP] FILENAME (FTPSITE=“SSH_CLIENT_SERVICENAME=‘SSH_USER’”)TO DISK(IPADDRESS=“xxx.xxx.xxx.xxx”) Interactive Client • U FTP • AUTHMODE SSH • SSH_CLIENT_SERVICENAME “SSH_USER” • OPEN xxx.xxx.xxx.xxx • PUT FILENAME FTP will prompt for the remote Username during the OPEN
SFTPServer configuration • To configure the MCP software as an SSH Server: • Create a public key for server’s identity (default name is SSH_SSHKEY) • Modify *SYSTEM/FTP/SUPPORT/CONFIGURATION [LIBRARY SECTION] INITIATE_SSH_SERVER = SSHSUPPORT • Detailed information can be found in FAQ 5847 on the Product Support Website and in standard MCP 14.0 documentation. • FAQ 5847 also contains the list of software (Interim Corrections) which must be downloaded.
SFTP Enhancements in MCP 15.0 • Server support for Windows SFTP clients. The ClearPath SFTP Server transfers files with the following Windows SFTP clients. • WinSCP • Attachmate Reflection FTP Client • FileZilla FTP Client • We’ll update the compatibility matrix on the support website. • Server support to append to ClearPath files. SFTP clients can append data to the end of existing ClearPath files. Example using WinSCP put -append TransactionHistory
Network SecuritySecure File Transfer (NFT) • Secure File Transfer for ClearPath MCP allows data transfer between two MCP hosts • New Feature introduced in MCP 13.1 • Does NOT require BNA network connectivity • MCP file attributes of source file are retained across the transfer • Can also be secured with SSL/TLS (cryptography support required) • Hazardous files controlled with the RESTRICTUNWRAP system security option • Transfers initiated with COPY [FTP] command or FTP Interactive and Batch clients
Secure File Transfer (NFT)Securing Hazardous Files Hazardous files (codefiles for example) are marked restricted unless: The RESTRICTUNWRAP system security option at the destination host is reset – or – The Library RESTRICTED option is reset by the FTP Administrator at the destination host - and - The RESTRICTED option is reset in the COPY command and the usercode at the destination host is a security administrator
Secure File Transfer (NFT)New MCPDATA transfer type • Transfers use data transfer type “MCPDATA” • COPY [FTP] TEST/CASE_1/= (FTPTYPE = MCPDATA) FROM DISK (PACK, IPADDRESS = “124.39.225.14”, USERCODE = SYSTEST/105639) • Copies all files under the TEST/CASE_1 directory on the remote MCP host to the local host • All attributes, including FILEKIND, are retained at the destination host. • No BNA network is required.
Secure File Transfer (NFT)Copying of codefiles COPY [FTP] (SYSTEST)OBJECT/TESTFILE (FTPTYPE=MCPDATA, FTPSITE=“OPT - RESTRICTED”) FROM TESTPACK(PACK) TO USERPACK (PACK, HOSTNAME=MCPEAST,USERCODE=ABC/ABC) The codefile (SYSTEST)OBJECT/TESTFILE on TESTPACK is copied to USERPACK at the remote MCP host, MCPEAST Resetting the RESTRICTED option prevents the codefile from being marked restricted, but only if user ABC is a security administrator at MCPEAST
Secure File Transfer (NFT)Network Security Data transmission can be secured by Secure Sockets Layer (SSL/TLS) Specify the level of security required for the file transfer (using the SSLMODE attribute) EXPLICIT IMPLICIT Command and data path are secured, different control ports are used. EXPLICITLOGON EXPLICITCOMMAND After logon command path can be optionally unsecured Data path security is independently selected COPY [FTP] DATADB (FTPTYPE = MCPDATA) FROM DISK (PACK, IPADDRESS = “124.39.225.14”, SSLMODE = IMPLICIT, USERCODE = SYSTEST/105639)
Secure File Transfer (NFT)Other Issues MCPDATA transfers are incompatible with older levels of FTPSUPPORT Non encrypted transfer speeds are similar with NFT Encrypted transfers are slower than non-encrypted transfers Non-MCP hosts running FTP can be used as store and forward hosts for MCPDATA transfers Documented in the TCP/IP Distributed System Services Operations Guide
Network SecuritySAN DataMover (DMV) • SAN DataMoverprovides an efficient way to move large amounts of disk data (local Windows environment required). • Between MCP and local Windows environment, • Between MCP and remote Windows, Linux or UNIX environment (by way of a local Windows environment) • Offloads data transfer to Windows environment (freeing ClearPath MCP MIPS) • Security Features (introduced in MCP 13.0) • SSL Support – Secure Communication between Windows and MCP SAN DataMoverComponents (requires MCP Cryptographic Services) • FTPS & SFTP Support – Secure Remote File Transfer • Both require MCP Cryptographic Services and configuration to enable and configure secure transfers.
Network SecuritySecuring Terminal Emulator Sessions • Protect data terminal emulator sessions to MCP servers • Many options available: • WebEnabler for ClearPath MCP – supports a 2-tier model – direct SSL connections from WebEnabler to ClearPath MCP • Secure TELNET – MCP Telnet can offer secure and/or unsecure sessions. Controlled via system security option (SECURECOMM) • Attachmate INFOConnectand MCP Telnet can also use a custom encryption protocol • SSH terminals are not supported at this time.
Network SecuritySecuring Print Data • Secure data between MCP and Print Server • Use the Secure Sockets Layer (SSL) or Transport Layer Security (TLS) protocols to protect data • MCPPRT Server (introduced in MCP 13.1) • Just Specify SSL in IOHandler Parameter • See PrintS Guide (8600 1039–514) • EOM (Depcon) Server (introduced in MCP 13.1) • Specify SSL in PC and MCP Configuration Files • See EOM Documentation
IP Security (IPsec)Security for the IPv6 network • Can authenticate and/or encrypt each IP packet in a data stream • Uses policies to define security at the MCP-to-network boundary. IP packets can be: • Forbidden from being transmitted unencrypted (DISCARD) • Allowed to be transmitted unencrypted (BYPASS) • Authenticated or encrypted prior to transmission (PROTECT) • Subject to US Government export control • Packaged in the operating environment encryption option • Supports 3DES and AES algorithms for packet encryption • IPv6 ONLY (no IPv4 support)
Tape / DVD Encryption Enhancements • Provides Enhanced Security for Encrypted Tapes/CDs/ DVDs • AESGCM encryption, the standard algorithm for tape encryption as specified by the IEEE • ESSIV scheme is used with CBC-mode to ensure each tape and each file on a tape are encrypted using a “random” Initialization Vector (IV) • Additional data integrity checking added to encrypted data • Enhancements are known as Version 2 Media Encryption • Format of Version 2 encrypted media is different from the original, Version 1, tape encryption format
Tape / DVD Encryption Enhancements • Examples • COPY F/= TO BACKUPTAPE(SERIALNO=“110812”, ENCRYPT=AESGCM) • Specifying ENCRYPT=AESGCM by definition creates a Version 2 Encrypted Tape • COPY F/= TO BACKUPCD(CD, ENCRYPT=AES256, ENCRYPTVERSION=V2) • Specifying ENCRYPTVERSION=V2 forces the use of ESSIV when doing AES with CBC-mode encryption
Tape / DVD Encryption Enhancements • Migration and Compatibility • Version 1 is used by default but Version 2 is recommended • A tape/CD/DVD created using Version 2 Media Encryption cannot be read on a system that only supports Version 1 tape encryption • Systems that support Version 2 Media Encryption can read and write both Version 1 and Version 2 tapes/CDs/DVDs • Library Maintenance will not support encryption using Version 1 in software released after October 2015 but decryption of media created using Version 1 will continue to be supported • Only Library Maintenance supports the new Media Encryption Version 2 enhancements – TapeStack and DMUTILITY do not
Tape / DVD Encryption Enhancements • Operator Controls • The existing LMENCRYPT SYSOP can now be set to AESGCM • Thus all tape/CD/DVD copies would be encrypted using AESGCM unless over-ridden in the COPY statement itself and would be in Media Encryption Version 2 format • A new LMDEFENCRYPT SYSOP can be set to “V1” or “V2” • LMDEFENCRYPT defaults to “V1” • LMDEFENCRYPT set to “V2” and LMENCRYPT set to “AES256” causes ESSIV to be used along with AES256 in CBC-mode and creates the encrypted media in Version 2 format • LMDEFENCRYPT set to “V1” and LMENCRYPT set to “AES256” uses AES256 in CBC-mode and creates the media in Version 1 format
Disk Encryption Options • Encryption Capable SANs • EMC VMAX: newer versions • EMC VNX: newer versions • Must be done at setup time. Can’t change a disk to be encrypted • BitLocker • FS1760 Internal Disk • Can be turned on and off • DMSII field level “obfuscation” • Not true encryption • Can’t search, sort, index, or replicate data with Databridge • What disk encryption is really for: • Data protection at time of disk dispose or theft
Security AdministrationSecurityCenter • Security Center • Preferred security administration tool • PC-based GUI and wizards • Enables security administrators to define, manage, and test/assess MCP security. • Replaces command line/batch tools such as MAKEUSER and SYSTEM/GUARDFILE. • Microsoft Management Console “snap-ins” • Security Policy Management • File Access Management • Cryptographic Services Management • Kerberos Configuration Management • User Account Management • Locum SafeSurvey • Locum SecureAudit • Locum RealTime Config
SecurityCenterCryptographic Services Manager • Used by security administrators to perform key management (create / import / export / renew) • SSL keys and certificates (used by WebTS, FTP, Sockets programs, User Programs) • Tape encryption keys (introduced in MCP 13.1) • IPsec keys (symmetric) • SSH Keys (introduced in MCP 14.0) • Also used for Certificate Management (SSL clients) • Certificate Stores • JAVA Certificate Stores
SecurityCenterTape Encryption - Compromised Key Sets • MCP-based software tape encryption can now mark a set of tape encryption keys as invalid for writing, and generate a replacement keyset • This may be done because: • A key of the set is thought to be compromised • The keyset’s lifetime (according to corporate policy) has been reached • Compromised keysets can still be used for decryption (retained indefinitely) • Only one active keyset per system / MCP mark release.
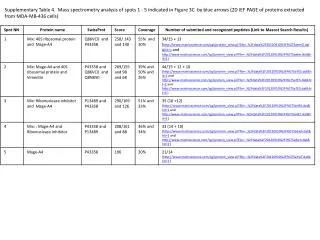
SecurityCenterTape Encryption - Managing Key Sets To manage sets: Under MCP Cryptographic Services, Trusted Keys, select node: Tape Encryption Keys Sets uniquely identified by Host name Release level Set number
SecurityCenterTape Encryption - Managing Key Sets Icon shows state of set: Green=Active Red=Inactive/Compromised Only the Active set for the local host is used to encrypt All sets are used for decryption. If a tape was encrypted with a key of that set, it will be automatically decrypted
SecurityCenterTape Encryption - Managing Key Sets • Create a set: • Right-click Tape Encryption Keys node, select “Create New Keyset” • Current (Highest-numbered) set is disabled, new set is created • Mark set compromised: • Right-click local host’s Active set, click “Mark as Compromised” • Selected set is disabled, new set is created
SecurityCenterTape Encryption - Best Practices • When a new keyset is generated, you must back up the keyset (via Export) and transport it to any systems that will need to decrypt tapes created on this host • Ensure that keys are stored securely • Ensure that keys are transported between systems securely
Stealth Solution SuiteYou Can’t Hack What You Can’t SeeChanging the Security Paradigm
Imagine a World… Where your sensitive data is invisibletohackers And is only visible… to users youselect
Unisys Stealth Solution Suite An NSA certified enterprise wide security innovation,incrementally and non-disruptively implemented, that makes data communication end points invisibleon a network and therefore be removed as a target for hackers. Stealth can reduce costs through consolidation and virtualization of a network and adds unprecedented protection to enterprise information. LAN/ Internet
Stealth Solution Key Elements Stealth consists of four important elements: 1 • Cryptographic Service Module • Provides FIPS 140-2 certified AES-256 encryption. 2 Information Dispersal Algorithm & Data Reconstitution Stealth formatted messages can only be reassembled by Stealth. 7. Application 6. Presentation 5. Session 4. Transport 3 Virtual Communities of Interest (COI) Hides users, data and servers from non-COI members. 3. Network 2. Link 1. Physical StealthDriver NIC 4 Executes Very Low in the Protocol Stack Protects device from attack. No changes required to Applications.
Unisys Stealth Solution Suite A Virtual Web Server B Virtual Web Server A Virtual App Server B Virtual App Server A Virtual DB Server B Virtual DB Server Enterprise wide – Consistent Security Approach Stealth Secure Remote Access Stealth secures information exchanged over public or private networks from many geographic locations. Stealth Regional Isolation LAN/WAN/Wireless Cloud Data Center Stealth Solution for Cloud Stealth protects data communication for teleworkers across the Internet superior to traditional VPN, using the Stealth driver loaded to a laptop or SSVT. Corporate Site External Network Stealth Data Center Segmentation Stealth cloaks the servers running sensitive applications or storing private information; these servers are not visible to anyone without the required Stealth crypto keys. Internet In a cloud, Stealth hides virtual workloads from unauthorized access in single or multi-tenant environments. Regional Site Internet Protected App Server Email Server (unprotected) Protected Database Server
Data Center Segmentation Enterprise Network • “Compartmentalize” data center using Communities of Interest (COI) instead of physical infrastructure • Mitigate Threats • Theft or Misuse of IP • Compliance Penalties • Minimizes scope of attacks • Benefits • Fosters Availability while ensuring Confidentiality and Data Integrity • Enhances application security by enforcing “Least Privilege” • Uses existing infrastructure • Security is not Port based • Facilitates regulatory compliance • Cost Savings potential 20%-50% • Reduce data center complexity; reduce VLANs and physical segmentation • Re-segment the data center using Active Directory • Simplified management Email Server (unprotected) Protected Server (Phys or VM) Protected App Server Protected Database Server Value: Protect high impact systems from intrusions on intranet
Regional Isolation • Regional Isolation prevents unauthorized access to information in the local region and on the corporate intranet • Mitigate Threats • Data communication eavesdropping by regional telecommunication providers and governments • Intrusions to corporate intranet • Intrusions to local site from within the region itself • Benefits • Assures only authorized access to corporate intranet • Protect regional assets from rogue endpoints • Segregate regional assets based on“need to know” • Segregate corporate assets based on “need to know” Enterprise Network A trusted country Enterprise MPLS Stealth GW Stealth Cloaked Geographic Region Value: Protect corporate data assets in a global topology
Stealth in the Cloud A Virtual Web Server B Virtual Web Server A Virtual App Server B Virtual App Server A Virtual DB Server B Virtual DB Server • Stealth in the Public or Private Cloud secures and isolates communication between virtual resources in a multi-tenant environment • Mitigates Threats • Theft or Misuse of IP within a tenant and between tenants • Workload is vulnerability to unauthorized access from inside or outside the cloud • Benefits • Protection follows the workload, regardless of where it is physically executing • Provides secure resource sharing within Communities of Interest • Isolates workloads between different COI • Integrated with Unisys Secure Private Cloud Solution for seamless deployment Stealth Solution for Cloud Cloud Data Center Internet Value: Bring Stealth security to the Cloud
Stealth Solution for Secure Virtual Terminal (SSVT) • SSVT secures and controls transmission over the Internet “from anywhere,” locking the communications channel to targeted endpoints. • SSVT is deployed via a locked down SecureUSB-based device running Stealth network security software. This virus-free, trusted environment is verified at each boot. • SSVT requires no change to your web enabled applications • SSVT enables workers to securely access • Their own desktop located in the enterprise, via an RDP session • Microsoft Remote Desktop Services or other VDI • Web enabled applications
Cost Reduction Stealth Organizational Value Security Business Benefits & Priorities Clients that want to increase security for their “crown jewel” applications and servers. Clients that need to protect corporate assets from regional facilities that may reside in hostile territories. Security Cost Savings Clients that want the simplicity of deployment and cost structure of public or flat networks but cannot sacrifice security…equally ideal for clients with multi-tier networks that need to contain costs while increasing security. Agility Agility Commercial Organizations Public Sector / Federal Clients that want to simplify data / resource access management
Stealth Extreme Security 2005 2006 2007 2008 2009 2010 2011 Stealth Crypto-Module DIACAP MAC-1 Certification JFCOM Network Risk Assessment CWID 05 AF Comm Agency DIACAP MAC-1 Certification CWID 10 SOCOM R&D Prototype JFCOM JIL Testbed IO Range IV&V National Center for Counter-terrorism and Cybercrime SOCOM FIPS 140-2 Certification NIST NSA EAL4+ Certification NIAP Export License Dept of Commerce 2012 Emerald Warrior ‘12 SIPRNet IATT CWID 05 USAF Combined Endeavour EUCOM CWID 08 DISA CWID 09 DISA CWID 10 SOCOM “Large Integrator” Tests and fails to break Stealth JUICE 09 CECOM GTRI DJC2 PMO SPAWAR Private Lab SSVT Validation: Failed to compromise DIACAP: DoD Information Assurance Certification and Accreditation Process MAC: Mission Assurance Category (Level 1 is Highest) DISA: Defence Systems Information Agency EUCOM : European Command SOCOM: Special Operations Command JFCOM: JOINT Forces Command JIL: Joint Intelligence Laboratory CWID: Coalition Warrior Interoperability Demonstration JUICE: Joint User Interoperability Communications Exercise CECOM: Communications Electronics Command (US Army) GTRI: Georgia Tech Research Institute DJC2: Deployable Joint Command and Control NIST: National Institute of Standards and Technology NIAP: National Information Assurance Partnership
Where is Stealth Deployed? Hertz, NZ uses Stealth to facilitate PCI DSS compliance The US Coast Guard uses SSVT for secure telecommuting We do use our own product! Unisys uses Stealth to secure and protect our high value application and database servers, and for secure remote telecommuting An Australian Military agency uses Stealth in a secure VDI Solution A large Midwestern Healthcare Agency is piloting Stealth to protect servers with sensitive data Many Commercial and Government pilots in progress
Stealth at Unisys Unisys not only sells Stealth to clients, we use it internally too. Data Center Segmentation: • At Unisys, Stealth has been deployed to secure some of our critical multi-tier applications. • With the web server, application logic and database on separate COIs, users cannot ping or even discover the existence of the application and database servers, ensuring that these cannot be tampered or hacked in any way. Users can only access the web server. Secure Remote Access: • More than 200 Unisys employees use Stealth on their laptops (with dual factor authentication) in order to securely access the corporate network when working from home or when travelling. • Unisys is deploying Stealth incrementally with our existing commercial VPN solution. Regional Isolation: • Currently in test! Stealth in the Cloud: • Unisys executes Stealth in our outsourcing Cloud environment to service our cloud clients.
Value-based Pricing Model Client pays relative to the differentiated value they receive from Stealth Example:Regional Isolation Example:Data Center Segmentation Example:Secure RemoteAccess