Using the wrong cryptography
Using the wrong cryptography. By VESMA System Architecture and Security. Home-grown cryptography. Don’t do it Rip the code out and replace it with library calls of respected algorithms. Protocol from low-level algorithms and wrong communication protocols.

Using the wrong cryptography
E N D
Presentation Transcript
Using the wrong cryptography By VESMA System Architecture and Security
Home-grown cryptography • Don’t do it • Rip the code out and replace it with library calls of respected algorithms
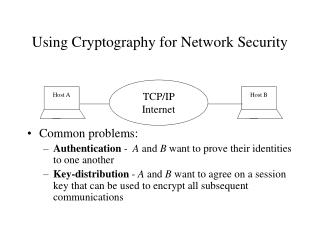
Protocol from low-level algorithms and wrong communication protocols • Don’t create your own security protocol • Use a well-understood/documented protocol • Don’t use outdated protocols (wrong!) • Use a high-level, tested security protocol - SSL 3 and TLS - IPSec - XMLDSig(signatures) - XMLEnc(encryption)
Weak key derivation function Failing to use salt • Use random salt • New salt for each stream • Ensure salt is generated from a strong random number generator • The worse the computational performance, the better the protection from brute-force attacks • Slow down the attacker
Failing to use random IV • Applies to block ciphers when using various chaining modes • Initialization vector must be cryptographically random
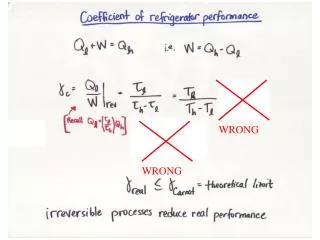
Weak cryptographic primitive • Don’t use outdated/broken security algorithms => Replace calls to weak algorithms with more secure versions Wrong cryptographic primitive • Don’t use encryption for tamper detection • Use some form of encoding • Ensure algorithms appropriateness • Ongoing “cryptographic inventory”
Cryptographic primitive – incorrect usage • Misusing stream ciphers • Hashing concatenated data • Electronic code book • Encrypting known plain text • Validating a hash incorrectly • Don’t use stream ciphers, Do Integrity checking, Don’t use the same key, Encrypt 1K and then start real encryption • Hash two things individually
÷ Integrity check • Stream cipher -> Integrity check • Provide independent password verifier and integrity checks • Correct way to do integrity check is to create an HMAC of the data • Don’t use your integrity check as password verifier
Failure to use Agile encryption • Accommodation of future software versions + new/updated encryption algorithms = agile encryption • KDF -> store the name of the derivation algorithm and the iteration count • Symmetric algorithms -> chaining and padding modes to be configurable • Protect cryptographic configuration data