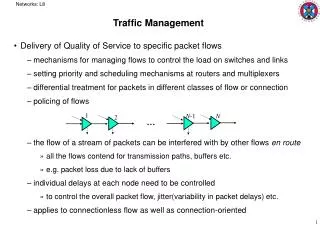
F5 Application Traffic Management
F5 Application Traffic Management. Radovan Gibala Senior Solutions Architect r.gibala@f5.com +420 731 137 223. 2010. Business Continuity HA Disaster Recovery. BIG-IP LTM • GTM • LC • WA FirePass • ARX • WJ. Application Delivery Architecture. WAN Virtualization File Virtualization

F5 Application Traffic Management
E N D
Presentation Transcript
F5 ApplicationTrafficManagement Radovan GibalaSenior Solutions Architectr.gibala@f5.com+420 731 137 223 2010
Business Continuity HA Disaster Recovery BIG-IP LTM • GTM • LC • WA FirePass • ARX • WJ Application Delivery Architecture • WAN Virtualization • File Virtualization • DC to DC Acceleration • Virtualized VPN Access User Experience & App Performance App Security & Data Integrity BIG-IP LTM • GTM • WA ARX • WJ BIG-IP LTM • ASM FirePass • AAA • Data Protection • Transaction Validation • Asymmetric & Symmetric Acceleration • Server Offload • Load Balancing People Apps Data • Virtualization • Migration • Tiering • Load Balancing • Virtualized App & Infrastructure • Server & App Offload • Load Balancing • Remote, WLAN & LAN Central Policy Enforcement • End-Point Security • Encryption • AAA Managing Scale & Consolidation Storage Growth ARX BIG-IP GTM BIG-IP LTM • GTM • LC • WA FirePass • ARX • WJ Unified Security Enforcement & Access Control FirePass BIG-IP LTM • GTM
Application How To Achieve the Requirements ? Multiple Point Solutions More Bandwidth Network Administrator Application Developer Add More Infrastructure? Hire an Army of Developers?
The Result: A Growing Network Problem Applications Users Network Point Solutions DoS Protection Mobile Phone SFA Rate Shaping SSL Acceleration CRM ERP CRM PDA Server Load Balancer ERP Laptop ERP CRM SFA ContentAcceleration ApplicationFirewall Desktop SFA Connection Optimisation TrafficCompression Customised Application Co-location
Traditional Infrastructure Model Corporate Employees LAN & wLAN Mobile Employees Remote Employees Branch Employees LAN & wLAN Customer, Partners, or Suppliers How do I connect all these applications and services to the right people, at the right moment in time, using the right amount of resources, meet all my SLAs, ensure security and save money? Cloud Services Hosted Applications Corporate Data Center SAAS Apps and Data in the Branch
What is Required to Fill the Gap - Unification Corporate Employees Mobile Employees Remote Employees Branch Employees Customer, Partners, or Suppliers Integration Visibility Context Unified Application and Data Delivery Model: Cloud Infrastructure Action Unification Enables the Dynamic Infrastructure Cloud Services Hosted Applications Corporate Data Center SAAS Branch apps and Data
F5’s Integrated Solution Applications Users The F5 Solution Application Delivery Network CRMDatabaseSiebelBEALegacy.NETSAPPeopleSoftIBMERPSFACustom Mobile Phone PDA Laptop Desktop TMOS Co-location
Flow Based TM/OS React to a Real Time, Two-Way Conversation Translate Between Parties A New Level of Intelligence Legacy Approach Packet Based React to a Single Communication, One Direction
Deliver Application Exactly as Intended Manage Entire Application Flows: • Independent Connection Control • Supporting All IP Applications • High Performance Framework • BI-Directional, Full Payload Inspection • Session Level Control Universal Inspection Engine (UIE) TM/OS Fast IP Interception Client Side Server Side
GUI-Based Application Profiles Repeatable Policies iRules and iControl Programmable Network Language Security Optimisation Delivery New Service The entire solution is built on top of the TMOS operating system that integrates all the tools Programmable Application Network Unified Application Infrastructure Services Targeted and Adaptable Functions Complete Visibility and Control of Application Flows Universal Inspection Engine (UIE) TMOS Fast IP Interception Client Side Server Side
Traffic Management Operating System iRules Rate Shaping / Rate Limiting Resource Cloaking Transaction Assurance Universal Persistence Caching Compression Selective Content Encryption Advanced Client Authentication Application Health Monitors Application Switching Shared Application Services TMOS Operating System Shared Network Services TCP Express Protocol Sanitization High Performance SSL DoS and DDoS Protection VLAN Segmentation Line Rate L2 Switching (Mirroring, Trunking, STP, LACP) IP Packet Filtering IPv6 Dynamic Routing Secure Network Address Translation Port Mapping Common Management Framework
Unique TMOS Architecture TrafficShield Web Accel 3rd Party Microkernel TCP Proxy Rate Shaping TCP Express SSL Caching XML Compression OneConnect TCP Express Client Side Server Side Client Server iRules High Performance HW iControl API • TMOS Traffic Plug-ins • High-Performance Networking Microkernel • Powerful Application Protocol Support • iControl – External Monitoring and Control • iRules – Network Programming Language
First Unified Application Infrastructure Services Delivering • Resource Cloaking • Advanced Client Authentication • Firewall - Packet Filtering • Selective Content Encryption • Cookie Encryption • Content Protection • Protocol Sanitization • DoS and DDos protection • Brute Force Attacks protection • DoS and SYN Flood Protection • Network Address/Port Translation • Application Attack Filtering • Certificate Management • Secure and Accelerated DC to DC data flow • Comprehensive Load Balancing • Advanced Application Switching • Customized Health Monitoring • Intelligent Network Address • Translation • Advanced Routing • Port Mirroring • SSL Acceleration • Quality of Service • Connection Pooling • Intelligent Compression • L7 Rate Shaping • Content Spooling/Buffering • TCP Optimization • Content Transformation • Caching • TCP Express • IPv6 Gateway • Universal Persistence • Response Error Handling • Session / Flow Switching • Network Virtualization • System resource Control • Application Templates • Dashboard
BIG-IP Local Traffic ManagerTurn your infrastructureinto an agile application delivery network Scale the application infrastructure Eliminate downtime Improve application performance Secure your applications and data Increase server capacity, reduce bandwidth Customize the delivery of the app for your needs BIG-IP Users Applications
It Starts with Load BalancingEnsure availability and plan for growth LTM load balances at the application level Ensures the best resources are always selected Has deep visibility into application health Proactively inspects and responds to errors Dynamic LB Methods Application Health Monitoring High Performance Hardware Session Persistence TransactionAssurance Eliminate downtime and scale the application
Comprehensive Load Balancing • Static • RoundRobin • Ratio • Dynamic • Fastest • LeastConnections • Observed • Predictive • Dynamic Ratio • Priority Groups
Feature Overview/BIG-IP • Availability Checking • Check any back-end process using EAV • Will work for any IP based application • Stateful failover between devices • Security • Firewall-like device to resist most attacks • All administration is encrypted • Integrated SSL/FIPS and secure NAT
Feature Overview/BIG-IP • SSL and E-Commerce • Only product with integrated SSL • Single certificate simplifies administration • Lowers certificate costs • Client certificate checking (Authentication) • Layer 7 Functionality • Can utilize all HTTP header/content or TCP content in traffic decisions • Can persist on anything • HTTP 1.1 keep-alives dramatically improve performance
Feature Overview/BIG-IP • Easy to Implement and Support • Can be deployed as either Layer 2 or 3 device • Simple and complete Graphical User Interface • Installation services by F5 and/or partner • Flexibility • BIG-IP works with any server or IP based service • iControl enables integration with internal and/or 3rd party applications
Powerful and Simplified Management “We have to deal with multiple products. The new user interface makes every other solution in this space look absolutely immature. F5’s solutions are 10 times easier to manage than Cisco.” - Major US Hosting Provider
Deliver Optimize Secure Profile Based Management • Profile Based Traffic Management • Improved vision of all resources and traffic
Ensure Higher Availability - Superior System Design • Processes Reporting and Control – Granular status, logging and configurable actions for component-level failures. Capable of warm restarts and upgrades. • 3-way HA Design – Robust Internal system checking and pass-through design.
Network VirtualizationRoute Domains Consolidation with control Host multiple groups on one BIG-IP without conflicts Granular control to provide separate routing domains and overlapping IPs
System Resource ControlModule Provisioning Consolidation with control Allocate CPU, memory, and disk per module Customize allocation to meet your needs
Simple Application Roll-outsApplication Templates 1 2 3 SharePoint 2007 VMware VDI Exchange Web Access 2007 IIS 7.0 HTTP BEA WebLogic 5.1, 8.1 Oracle Application Server 10g SAP ERP 6.0 and ERP 2006 Citrix Presentation Server DNS IP Forwarding LDAP RADIUS “The Application Templates allowed us to deploy Microsoft IIS in seconds instead of hours” - System Engineer, Fortune 500 Co.
Secure and Accelerate DC to DCiSessions Secure and accelerate between data centers Integrated and free with BIG-IP LTM v10 • Symmetric Compression • Adaptive • Deflate • LZO • SSL Encryption Note: Not available on the 1500 and 3400
Application Security Module Protect applications and data SSL Acceleration Protect data over the Internet Advanced Client Authentication Module Protect against unauthorised access BIG-IP Security Add-On Modules
Compression Module Increase performance Webaccelerator - Fast Cache Module Offload servers Rate Shaping Module Reserve bandwidth BIG-IP Software Add-On ModulesQuickly Adapt to Changing Application & Business Challenges
Intelligent HTTP Compression Most Intelligent and flexible solution to target HTTP compression where it matters most • URI/content filters – allow/disallow lists • Compress only specified file types • Based on URI or MIME type • Client-aware compression (patent pending) • Based on TCP latency – observe client RTT • Based on low bandwidth client connections • Granular L7 based compression • Tunable resource allocation • Devote more memory and CPU cycles for high priority compression jobs • Adaptable Compression • Scale back compression based on CPU load
Real Time Compression Tool www.f5demo.com/compression
Improve the End-User Experience LTM improves the application performance Optimize the connections and prioritize traffic Reduce the amount of data sent, both to the client and across the WAN TCP Express Intelligent Compression WebAccelerator (add-on module) iSessions
Secure the Applications and Data Security at Application, Protocol and Network Level Meet compliance requirements (PCI, HIPAA, etc.) Strong protection without interrupting legitimate traffic Authentication and Authorization (via client cert, AD, LDAP, RADIUS, RSA SecurID agents) Secure Remote Access (SSL-VPN) Optimization (caching, compression, web acceleration) Endpoint Security Policy Engine Network and Protocol Attack Prevention Resource Cloaking and Content Security Application Security Manager (add-on module) Selective Encryption Application Policy Manager (add-on module)
Let Servers Serve LTM offloads tasks from application servers Reduce the number of servers required Centralize SSL key management One Connect Fast Cache SSL Offload Compression 1/2 of BIG-IP owners have saved 20% or more on their total Capital Expenses with BIG-IP Source: TechValidate Survey of F5 BIG-IP Users
TCP Express • Behaviors of a good TCP/IP implementation. • Proper congestion detection. • Good congestion recovery. • High bandwidth utilization. • Being too aggressive can cause individual connections to consume all of the network. • Not being aggressive enough will leave unused bandwidth especially during a low number of connections. • Always needs to adapt to changing congestion. • Increased windowing and buffering will often help compensate for latency and can also offload the application equipment more quickly. • Most important tuning you can do in TCP typically has to do with window sizes and retransmission logic (aka congestion control behavior). • On today’s networks, loss is almost always caused from congestion. • Most TCP stacks are not aggressive enough.
F5’s TCP Congestion Control Algorithms • Reno Congestion Control • Original TCP fast recover algorithm based on BSD Reno. • Initially grows congestion window exponentially during the slow-start period. • After slow-start, increases CWND by 1MSS for each CWND acked (this is linear growth). • When loss or a recovery episode is detected, the CWND is cut in half. • New Reno modifications (this is currently the default mode) • Improves on the Reno behaviour. • When entering a recovery episode, implements a fast retransmit: • Each ACK less than the recovery threshold triggers a one-time resend of the data started by the ACK. • Results in more aggressively sending the missing data and exiting the recovery period. • Scalable TCP (added in 9.4) • Improves on the NewReno behaviour. • Upon loss, the CWND is reduced by only 1/8. • Once out of slow start, CWND increases by 1% of an MSS for each CWND ACK’d. • HighSpeed (F5's proprietary congestion control added in 9.4) • Similarly improves on the NewReno behaviour in combination with Scalable TCP. • Progressively switches from NewReno to Scalable TCP based on the size of the CWND. • Upon loss, the CWND is reduced by somewhere between ½ and 1/8. • CWND grows somewhere between 1% and 100% of an MSS for each CWND ACK’d.
OneConnect ™ – Connection Pooling • Increase server capacity by 30% • Aggregates massive number of client requests into fewer server side connections • Transformations form HTTP 1.0 to 1.1 for Server Connection Consolidation • Maintains Intelligent load balancing to dedicated content servers Good Sources: http://tech.f5.com/home/bigip/solutions/traffic/sol1548.html http://www.f5.com/solutions/archives/whitepapers/httpbigip.html
HTML server pool GIF server pool ASP server pool b.gif sales.htm c.asp e.gif a.gif d.gif index.htm f.asp OneConnect ™ New and Improved HTTP Request Pooling • Streamlines single client request to BIG-IP • Enabled by HTTP 1.1 • Avg. Reduction is 20 to 1 per Web Page 20 b.gif c.asp a.gif index.htm 1 b.gif c.asp a.gif index.htm 1) OneConnect ™ Content Switching • Intelligent load balancing to dedicated content servers • Maintain Server Logging index.htm b.gif a.gif b.gif c.asp a.gif index.htm c.asp 2) OneConnect ™ HTTP transformations New • Transformation form HTTP 1.0 to 1.1 for Server Connection Consolidation One b.gif c.asp a.gif index.htm Many b.gif c.asp a.gif index.htm 3) OneConnect ™ Connection Pooling • Aggregates massive number of client requests into fewer server side connections b.gif c.asp a.gif index.htm Server sales.htm e.gif d.gif f.asp
Content Spooling Problem: TCP Overhead on Servers • There is overhead for breaking apart…”chunking” content • Client and Server negotiate TCP segmentation • Client forces more segmentation that is good for the server • The Servers is burdened with breaking content up into small pieces for good client consumption Solution Slurp up server response Spoon feed clients Benefit: Increases server capacity up to 15%
L7 Rate Shaping Integrated and Fine Grained Bandwidth Control Rate Class • Sophisticated Bandwidth Control • Flexible bandwidth limits • Full support for bandwidth borrowing • Traffic queuing (stochastic fair queue, FIFO ToS priority queue) • Granular Traffic Classification L2 through L7 • iRules support can initiate a rate class on any traffic flow variable • Only Multi Direction Control • Control throughput in any direction Ceiling Rate Burst Base WAN Network Segments Pool of Servers
VIPRION Actual BIG-IP Platforms BIG-IP 8900 Price BIG-IP 6900 2 x Quad core CPU 16 10/100/1000 + 8x 1GB SFP 2x 320 GB HD (S/W RAID) + 8GB CF 16 GB memory SSL @ 58K TPS / 9.6Gb bulk 6 Gbps max hardware compression 12 Gbps Traffic Multiple Product Modules BIG-IP 3900 2 x Dual core CPU 16 10/100/1000 + 8x 1GB SFP 2x 320 GB HD (S/W RAID) + 8GB CF 8 GB memory SSL @ 25K TPS / 4 Gb bulk 5 Gbps max hardware compression 6 Gbps Traffic Multiple Product Modules Quad core CPU 8 10/100/1000 + 4x 1GB SFP 1x 300 GB HD + 8GB CF 8 GB memory SSL @ 15K TPS / 3.8 Gb bulk 3.8 Gbps max software compression 4 Gbps L7 Traffic Multiple Product Modules BIG-IP 3600 Dual core CPU 8 10/100/1000 + 2x 1GB SFP 1x 160 GB HD + 8GB CF 4 GB memory SSL @ 10K TPS / 2 Gb bulk 1 Gbps max software compression 2 Gbps Traffic 1 Advanced Product Module BIG-IP 1600 Dual core CPU 4 10/100/1000 + 2x 1GB SFP 1x 160GB HD 4 GB memorySSL @ 5K TPS / 1 Gb Bulk 1 Gbps max software compression 1 Gbps Traffic 1 Basic Product Module Function / Performance
2008: Hardware Architectur (Single-Board-Design) LCD-Panel HDD1 1 / 2 HDD2* 1 / 2 CFlash* SSL TMM: Traffic Management Microkernel FIPS*: Federal Information Processing Standards AOM: Always On Module (SCCP in former Versions) BCM: Broadcom Asic RAM SSL* CPU Hardware Compression Card* CPU CPU* CPU* AOM Powersupply TMM (Layer4-7) Powersupply* BCM (Layer 2) Failover Serial Mgmt x*10/100/1000Base-T Copper/SFP-GBIC 10GbEth* * Depends on platform (optional)
High-Performance Application Switches BIG-IP 8900 • Consolidate with Purpose-built Hardware • Designed specifically for application delivery • Integrated platform for security, acceleration, availability • Offload Application Servers • High performance hardware SSL and compression offload • Advanced connection management • Reduce Operating Costs • Simplified management with USB, front panel management, remote boot, and more • Increased uptime with hot swappable and redundant components BIG-IP 6900 BIG-IP 3900 BIG-IP 1600 - 3600
BIG-IP 1600High performance meets high value High Performance Dual-core CPU provides 1 Gb/s of L7 throughput Reliable and Adaptable Options for dual power and DC power Front-to-back cooling Basic security and acceleration options Protocol Security Module 1 Gb/s compression and SSL throughput
BIG-IP 3600Integrated ADC in a 1U platform Advanced security and acceleration options WebAccelerator option Application Security Module option High Performance Dual-core CPU provides 2 Gb/s of L7 throughput Reliable and Adaptable Options for dual power and DC power Front-to-back cooling
BIG-IP 3900Integrated ADC in a 1U platform Advanced security and acceleration options WebAccelerator and Application Security Module can run simultaneously High Performance Quad-core CPU provides 4 Gb/s of L7 throughput Reliable and Adaptable 4 SFP slots Options for dual power and DC power Front-to-back cooling
BIG-IP 6900Consolidation and Integration High Performance for Consolidation Dual CPU, Dual Core for 6 Gb/s of L7 throughput Hardware SSL and Compression offload Multi-module Integration Run multiple modules and unify application delivery functions onto a single device Reliable and Adaptable Dual power supplies and dual hard drives standard Front-to-back cooling